PII Belonging to Indian Citizens, Including their Aadhaar IDs, Offered for Sale on the Dark Web
Cyber Threat Landscape
In early October, Resecurity’s HUNTER (HUMINT) unit identified millions of personally identifiable information (PII) records, including Aadhaar cards, belonging to Indian residents being offered for sale on the Dark Web. The total number of the affected citizens is a matter of in-depth investigation by authorities, but the concerning fact that the data is valid and sensitive.
Updated (October 31, 2023 - 20:29 PM PST): Following the public disclosure by Resecurity, the threat actor since removed the post. However, a cached version of the content still remains accessible through the Wayback Machine: https://web.archive.org/web/20231031073546/https://breachforums.is/Thread-815-Million-Indian-Citizen...
What is Aadhaar?
An Aadhaar is a unique, 12-digit individual identification number “issued by the Unique Identification Authority of India on behalf of the Government of India,” according to the UIDAI website. Aadhaar enrollment is strictly voluntary and only proves residence in India, not Indian citizenship. Beyond the PII found on traditional ID documents, Aadhaars include “core biometrics,” including 10 fingerprints and two iris scans, according to a September 2023 UIDAI brochure.
With roughly 1.4 billion Aadhaars issued by the UIDAI since this ID service launched in 2009, this system represents one of the largest biometric ID programs on the planet, according to a 2022 report published by think tank Brookings Institution. In a 2017 interview with Bloomberg, World Bank chief economist Paul Romer described the Aadhaar ID system as "the most sophisticated that I’ve seen."
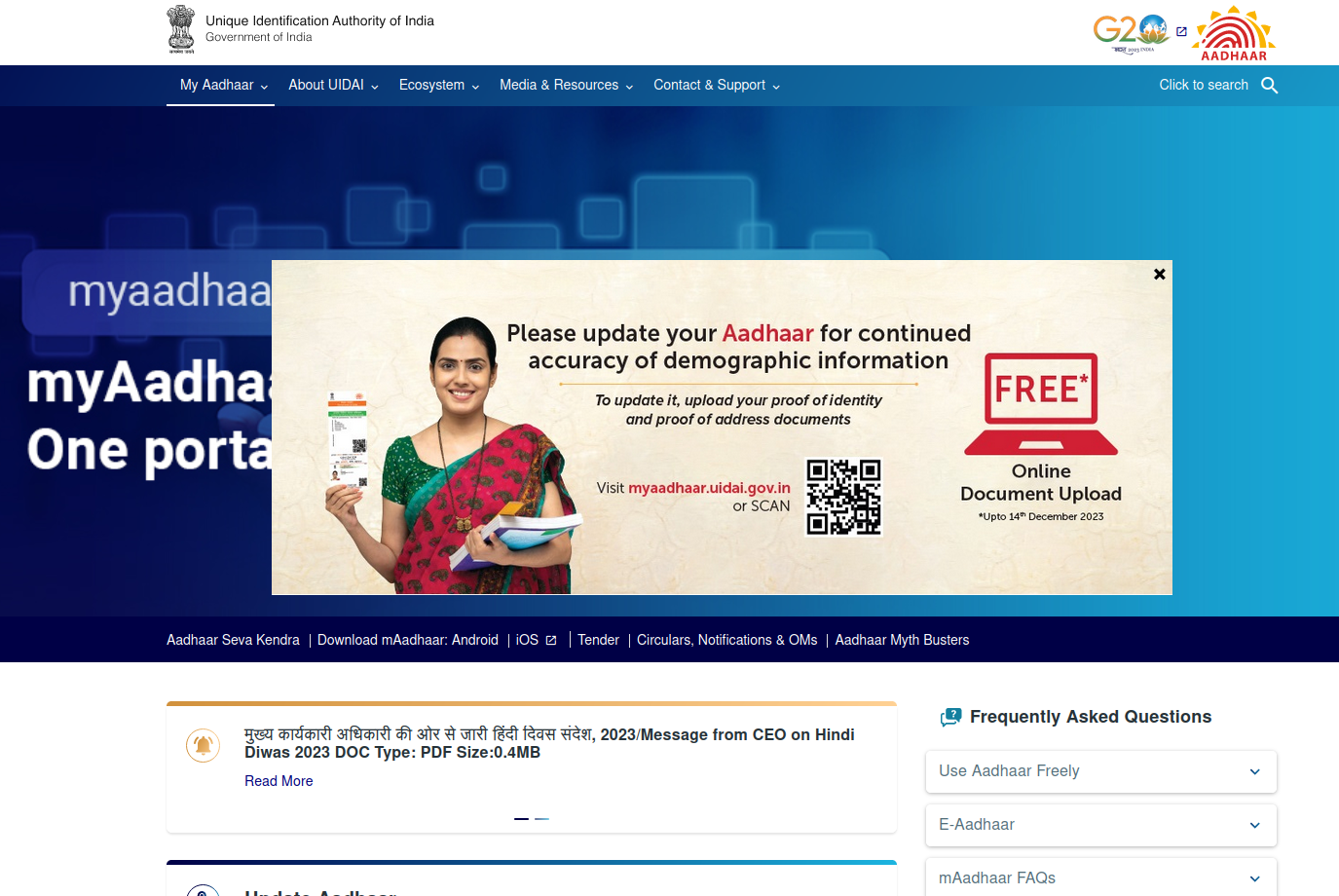
Powered by these biometric markers, Aadhaars function as digital IDs, facilitating electronic payments, online Know Your Customer (e-KYC) verification, and compatibility with various Indian financial platforms. Beyond digital payments, Aadhaars also enable e-tax filing, bill payments, and financial assets management, per the UIDAI brochure. Furthermore, Aadhaar has been “credited with making it easier for Indians to access subsidies and pension payments,” according to the Brookings report.
The Brookings report also noted that the “Election Commission of India wants to link their voter registration database with Aadhaar, a move that would have profound consequences not only for the privacy of Indian citizens but for the future of biometric databases worldwide.” The Election Laws Amendment Bill, passed by the Lok Sabha, the lower house of India’s bicameral Parliament, in December 2021, created a legal framework to integrate Aadhaar and Election Commission databases.
As of February 2023, 60% of India’s eligible voters, or 945 million people, had linked their Aadhaar card to their voter IDs, according to local media reports. Nevertheless, critics and activists have warned that this measure could disenfranchise some electors in states that make Aadhaar linkage to voter rolls mandatory. The Brookings report also flagged the risk of fraud and how “political microtargeting could result in a loss of privacy and exposure to selective information, providing fertile ground for mis- and dis-information to spread and polarization to increase.”
Indian citizens can voluntarily obtain Aadhaar credentialing. Non-resident Indians (NRIs) can also obtain an Aadhaar, provided they have spent 182 days or more in India over the twelve-month period immediately preceding the date of application for enrollment. Aadhaar enrollment data is collected by the UIDAI. First established in 2009, the UIDAI became a statutory authority in 2016, under the jurisdiction of the Ministry of Electronics and Information Technology, following the provisions of the Aadhaar (Targeted Delivery Of Financial And Other Subsidies, Benefits and Services) Act, that was passed the same year.
Over a year before Moody’s raised concerns about the reliability of Aadhaar’s biometric authentication controls, the 2022 Brookings report cited the digital ID program’s “insecure ecosystem, lack of data standards, and the UIDAI’s lack of transparency and accountability.” Specifically, the Comptroller and Auditor General (CAG) of India probed the UIDAI in April 2022 and found that the authority “had failed to properly regulate its client vendors and ensure the security of their data vaults,” according to the Brookings report.
Indian Data for Sale in Dark Web
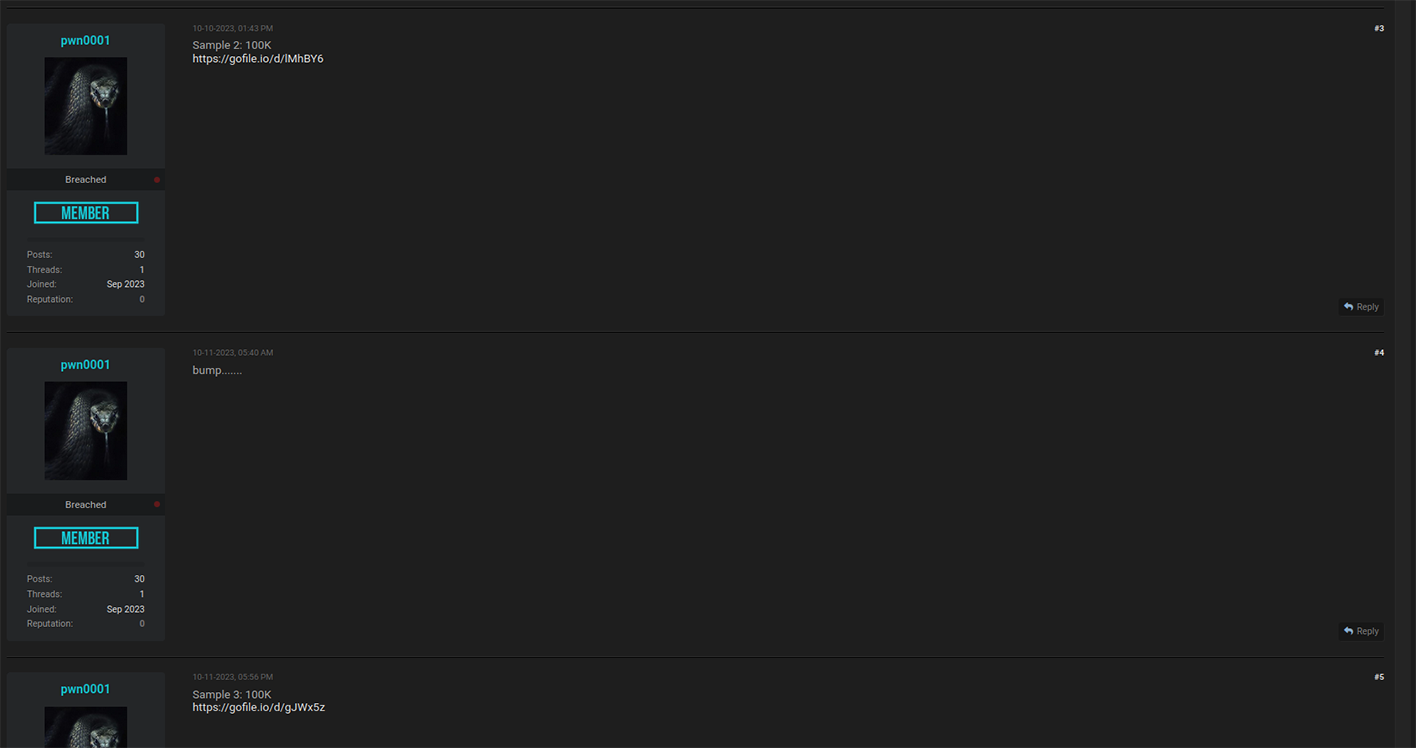
On October 9th, a threat actor going by the alias ‘pwn0001’ posted a thread on Breach Forums brokering access to 815 million “Indian Citizen Aadhaar & Passport” records. To put this victim group in perspective, India’s entire population is just over 1.486 billion people.
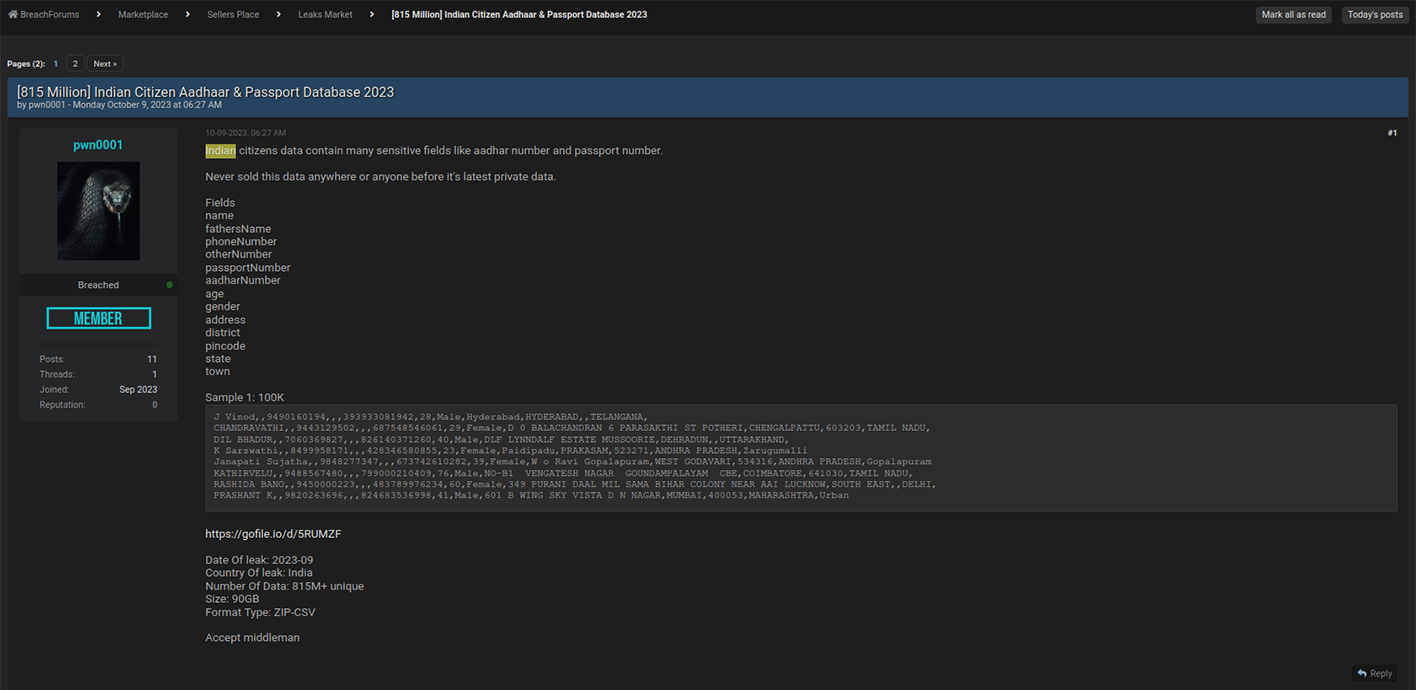
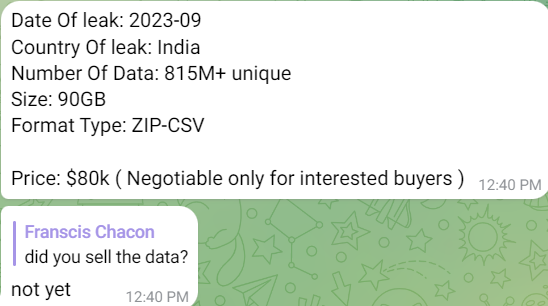
HUNTER investigators established contact with the threat actor and learned they were willing to sell the entire Aadhaar and Indian passport dataset for $80,000.
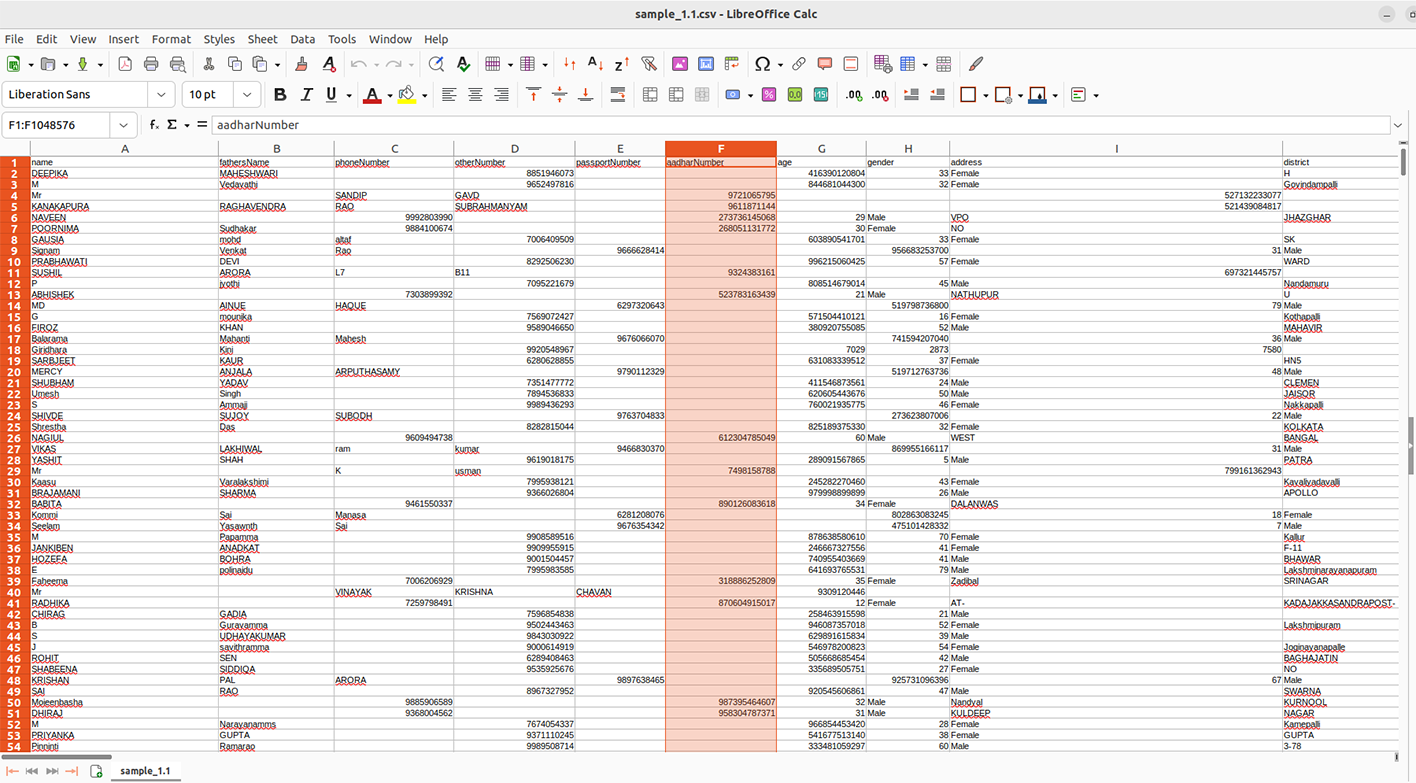
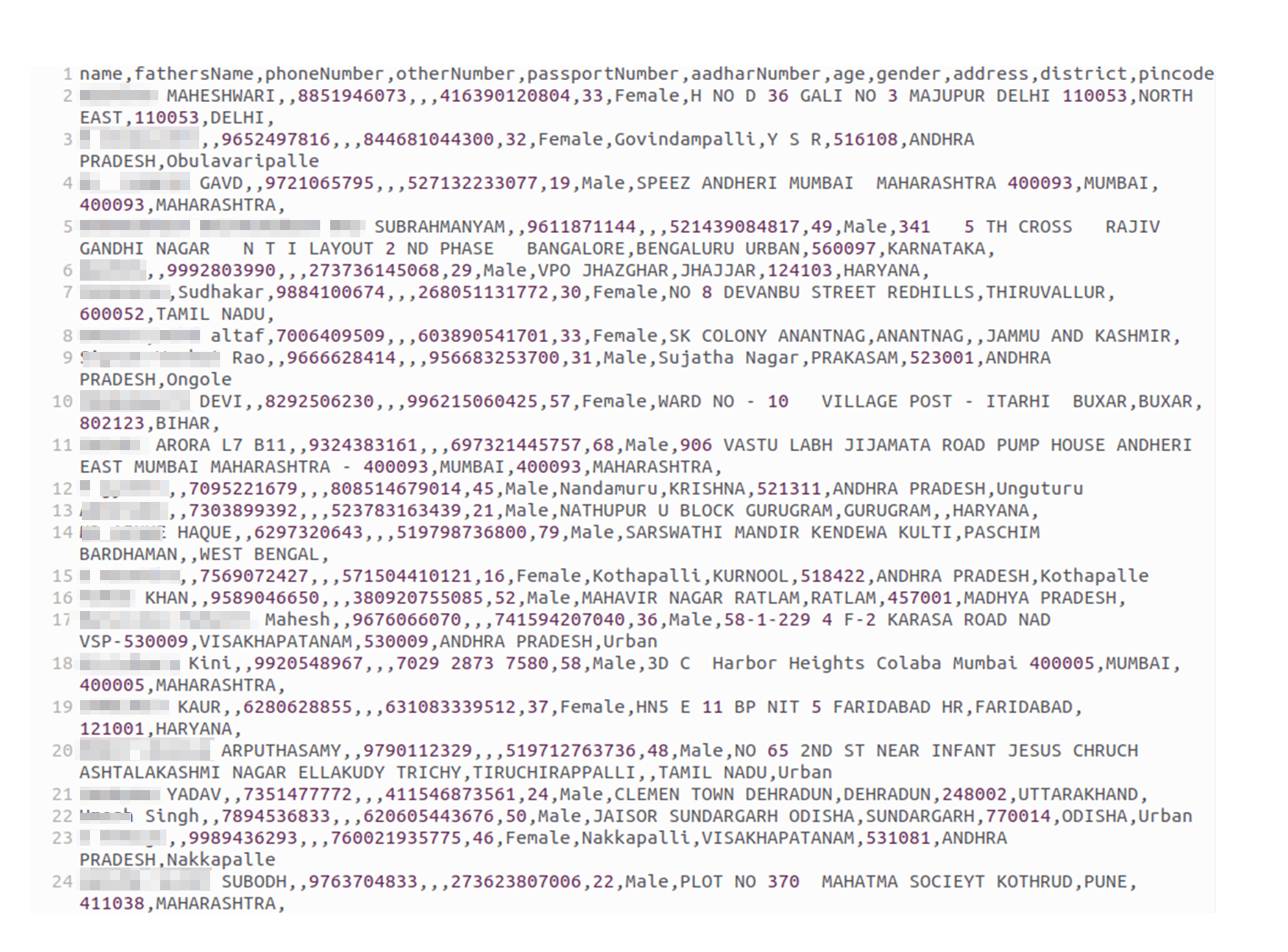
The data set offered by pwn0001 contains multiple fields related to the PII of Indian citizens, including but not limited to:
- name
- fathersName
- phoneNumber
- otherNumber
- passportNumber
- aadharNumber
- age
- gender
- address
- district
- pincode
- state
Pwn0001 declined to specify how they obtained the data. Without the threat actor disclosing the source of the data leak any effort to diagnose the cause of the beach will be speculative.
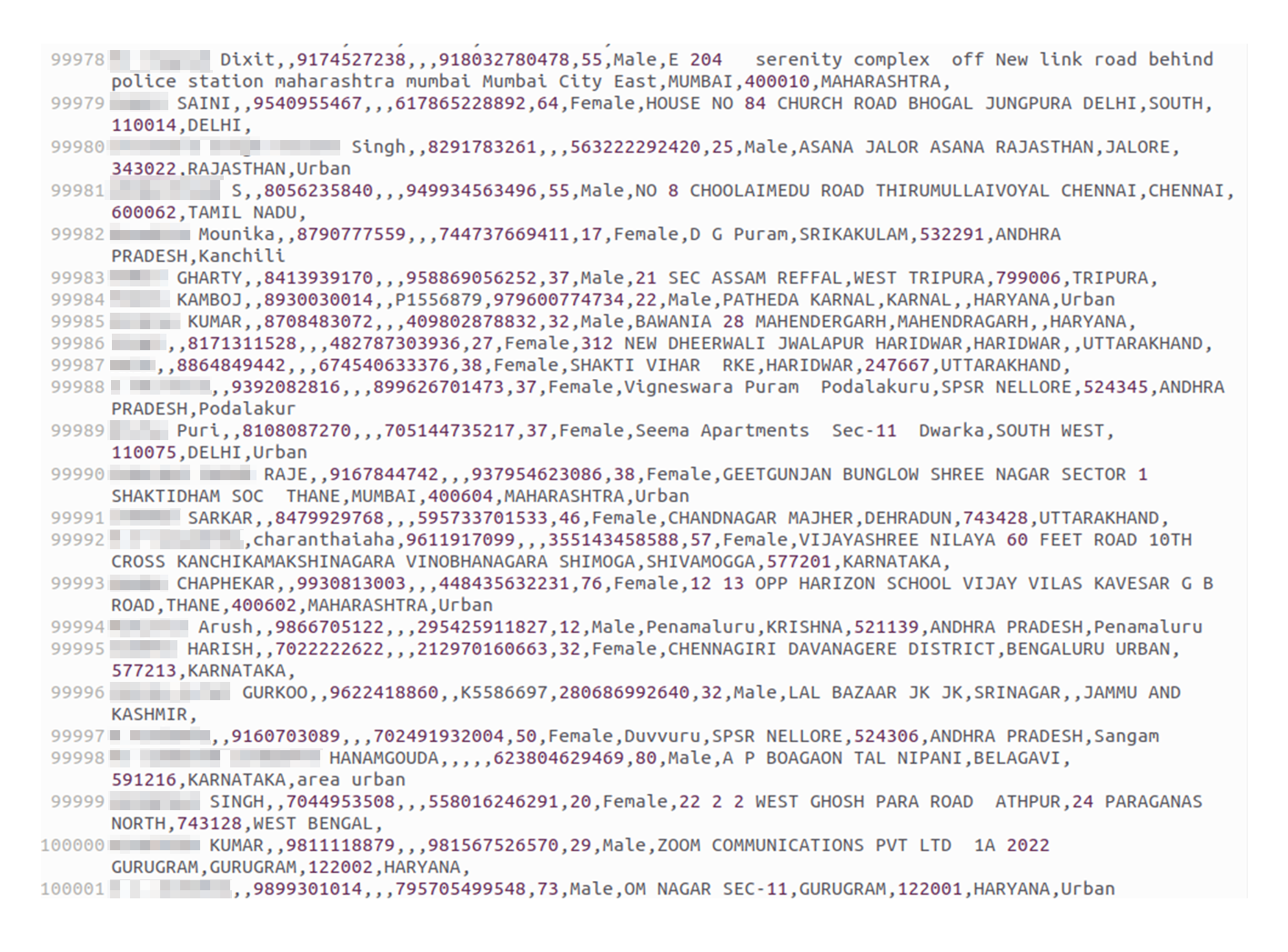
Concurrently, pwn0001 shared spreadsheets containing four large leak samples with fragments of Aadhaar data as a proof. One of the leaked samples contains 100,000 records of PII related to Indian residents. In this sample leak, HUNTER analysts identified valid Aadhaar Card IDs, which were corroborated via a government portal that provides a "Verify Aadhaar" feature. This feature allows people to validate the authenticity of Aadhaar credentials.
On October 9th, The threat actor shared a sample containing 100,000 records.

Then, on October 10th and 11th, additional samples were leaked by the actor as proof, making a total of 300,000 records exposed.
The actor then shared their last sample on October 13th. In total the actor leaked 400,000 records containing AADHAAR details.
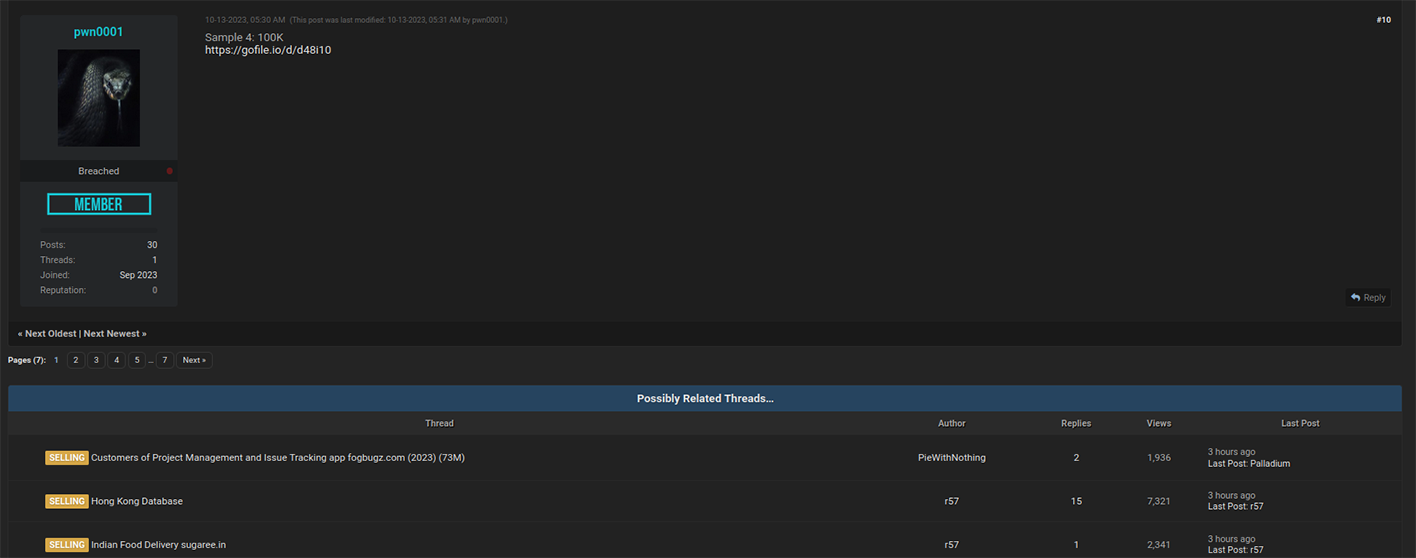
Resecurity acquired all 400,000 records and contacted multiple victims to validate the information, as well as used "Verify Aadhaar" feature available via official government WEB-resource in India.
The contacted victims from the acquired data set confirmed the validity of their data, and stated they have never been notified about it before. It is not clear, if the affected (breached) parties are aware about the incident and will be disclosing it responsibly to notify victims of the data breach and the Indian government.
On August 30th, another threat actor going by the alias ‘Lucius’ posted a thread on Breach Forums promoting a 1.8 terabyte data leak impacting an unnamed “India internal law enforcement organization.”
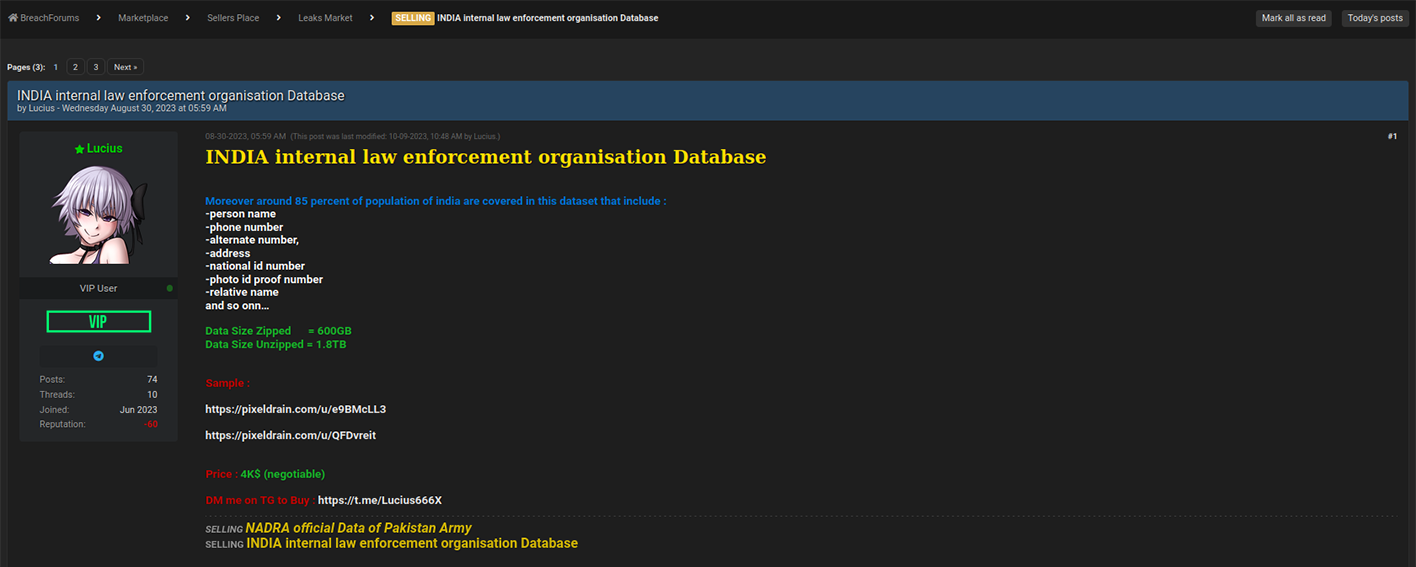
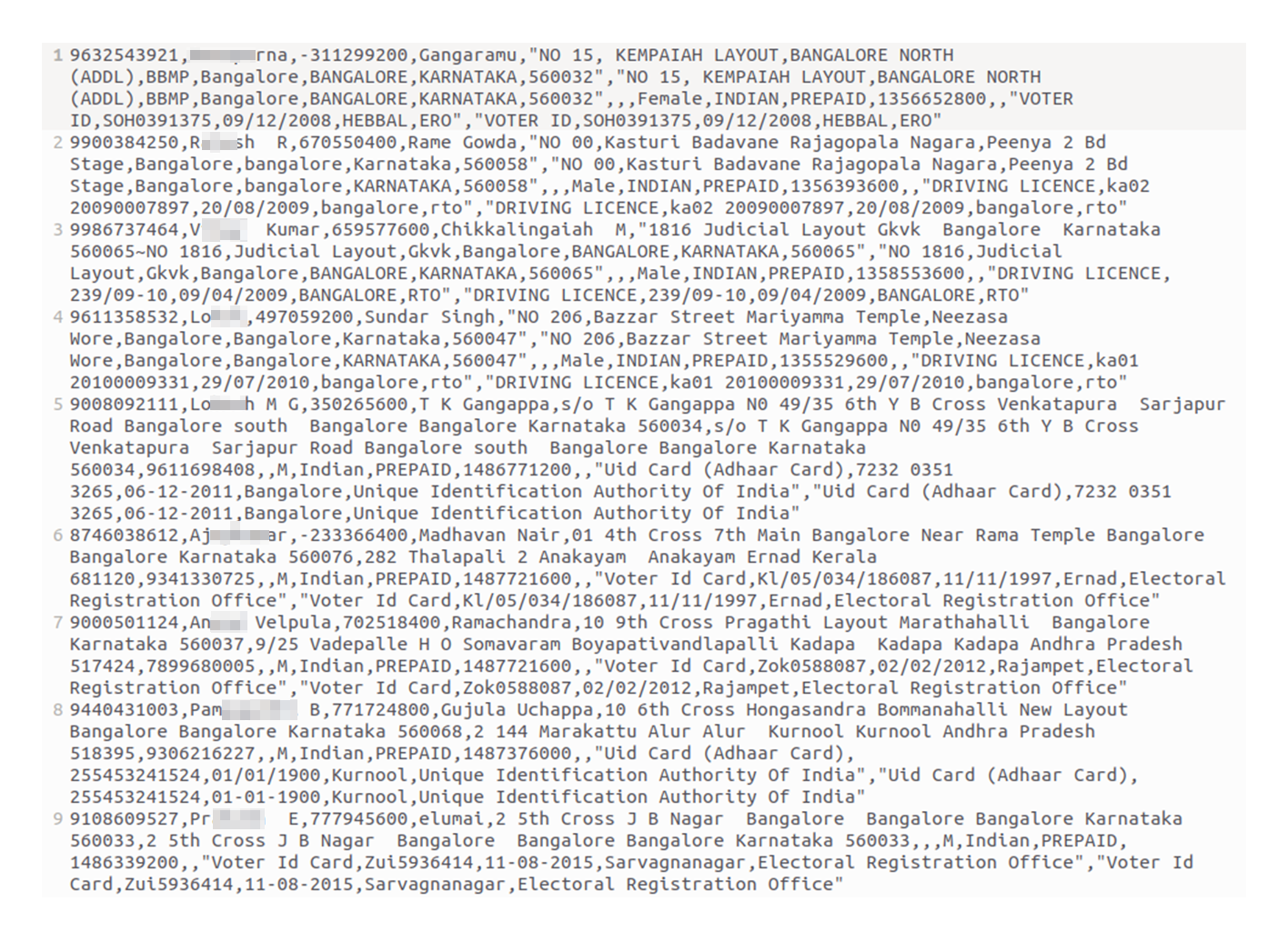
This data set contained an even more extensive array of PII data than pwn0001's. Beyond Aadhaar IDs, Lucius’ leak contained Voter IDs and driving license records. The threat actor may be referencing law enforcement to plant a red herring and conceal the real intrusion vector that enabled them to acquire the data. Lucius may also just be trying to generate hype around their offering.
Highlighting the first breach scenario, HUNTER analysts identified multiple records with the signature "PREPAID." This signature may be related to the leak from one of the telecommunication carriers that offer pre-paid SIM cards and similar services using such information for KYC (Know Your Customer). These service offerings also entail the collection of PII data to validate customers prior to the activation of mobile services.
In any case, the mass-leakage of Indian PII data on the Dark Web creates a significant risk for digital identity theft. By exploiting these stolen credentials, cybercriminals targeting India can perform a range of financially motivated scams like online-banking theft and e-tax refund frauds.
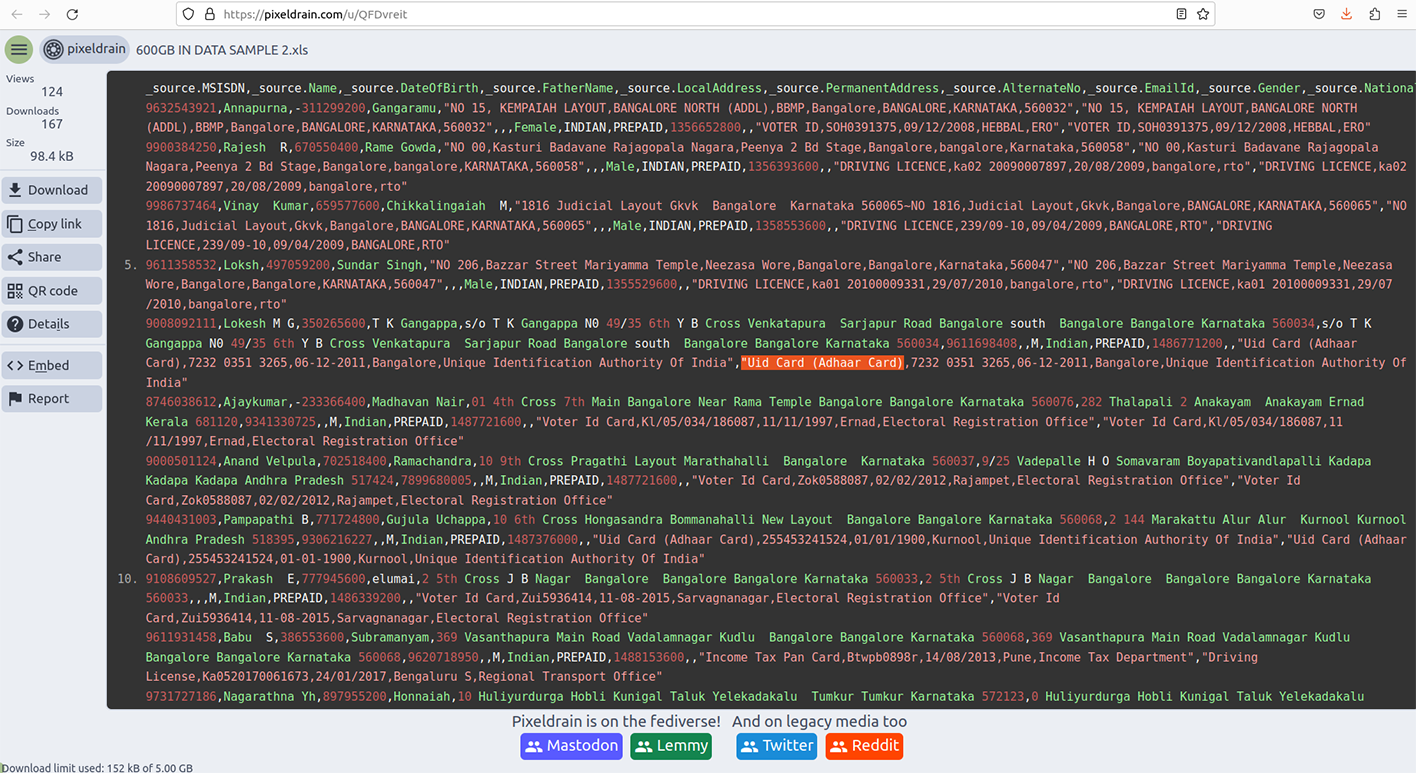
Resecurity inspected the data set shared by "Lucious" and based on our assessment the data may be coming from a breached 3d party (presumably, telecom/mobile operator, collecting PII/AADHAAR for KYC). The data set is different from the one shared by 'pwn0001' and contains the following fields with reference to MSISDN and SIM Activation Date relevant to mobile carrier subscribers:
- _source.MSISDN
- _source.Name,
- _source.DateOfBirth,
- _source.FatherName,
- _source.LocalAddress,
- _source.PermanentAddress,
- _source.AlternateNo,
- _source.EmailId,
- _source.Gender,
- _source.Nationality,
- _source.ConnectionType,
- _source.SIMActivationDate,
- _source.Aadhar,
- _source.PhotoIdProofDetails,
- _source.AddressProofDetails
The sample of data observed by Resecurity contains multiple references to the Unique Identification Authority of India and AADHAAR card, as well as Voter ID cards. It is possible, the actor successfully breached a 3rd party aggregating these details. Our analysts contacted multiple victims independently and confirmed the validity of data. None of the victims were aware about the exposure of this data in Dark Web, and had never received any notifications with regards to this as of today.
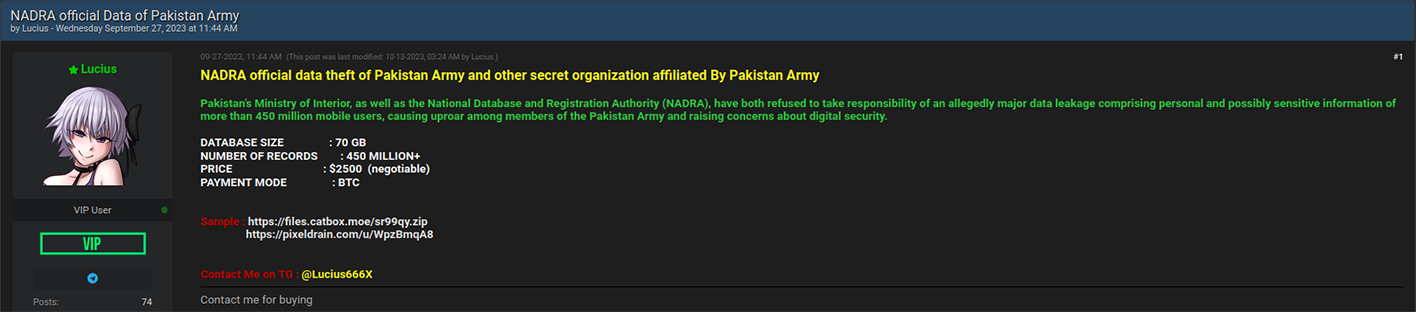
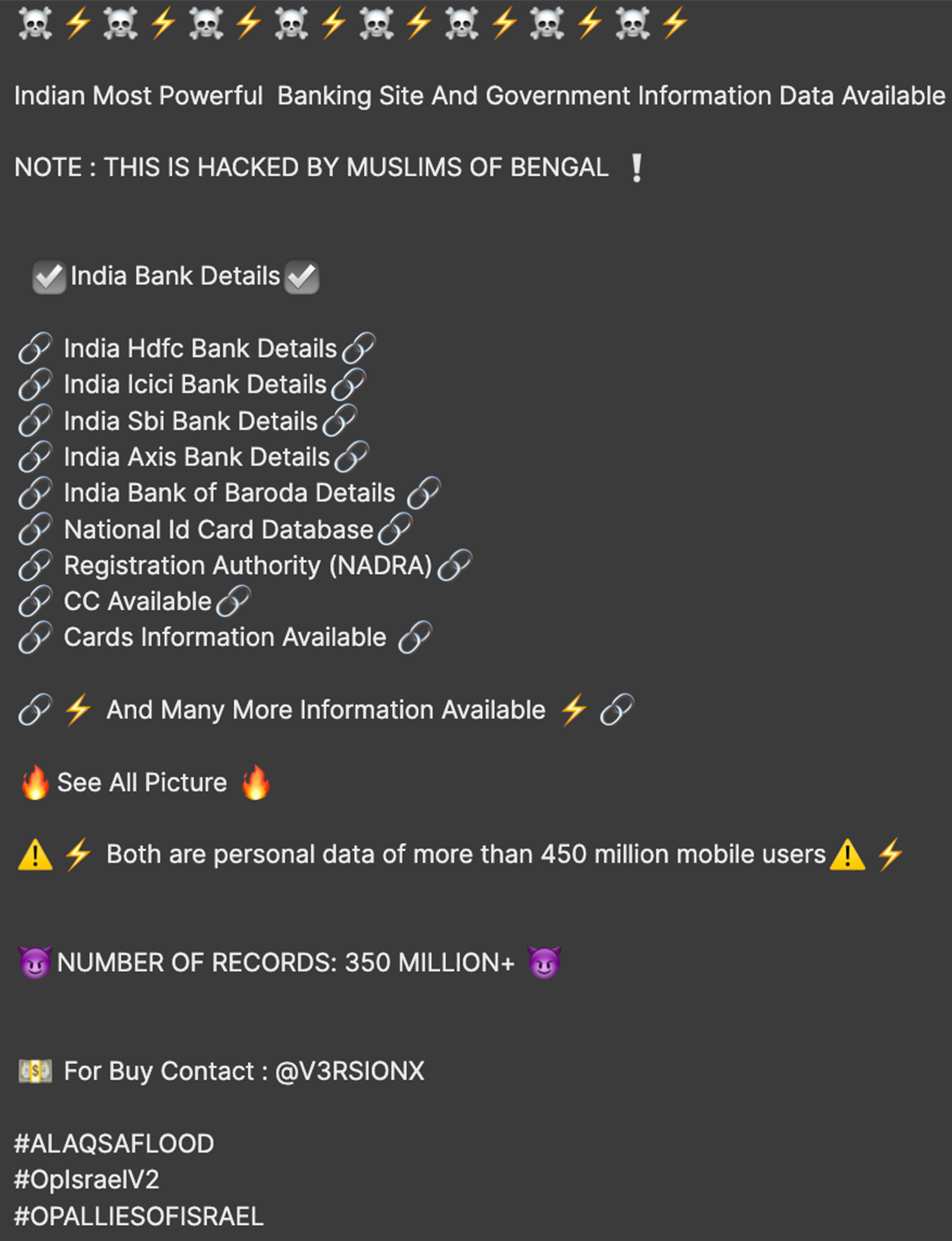
On September 27th, Lucius also posted a thread on Breach Forums promoting access to 70 GB of data stolen from Pakistan’s army and a “secret organization” affiliated with it. Lucius said this leak impacts over 450 million mobile subscribers.
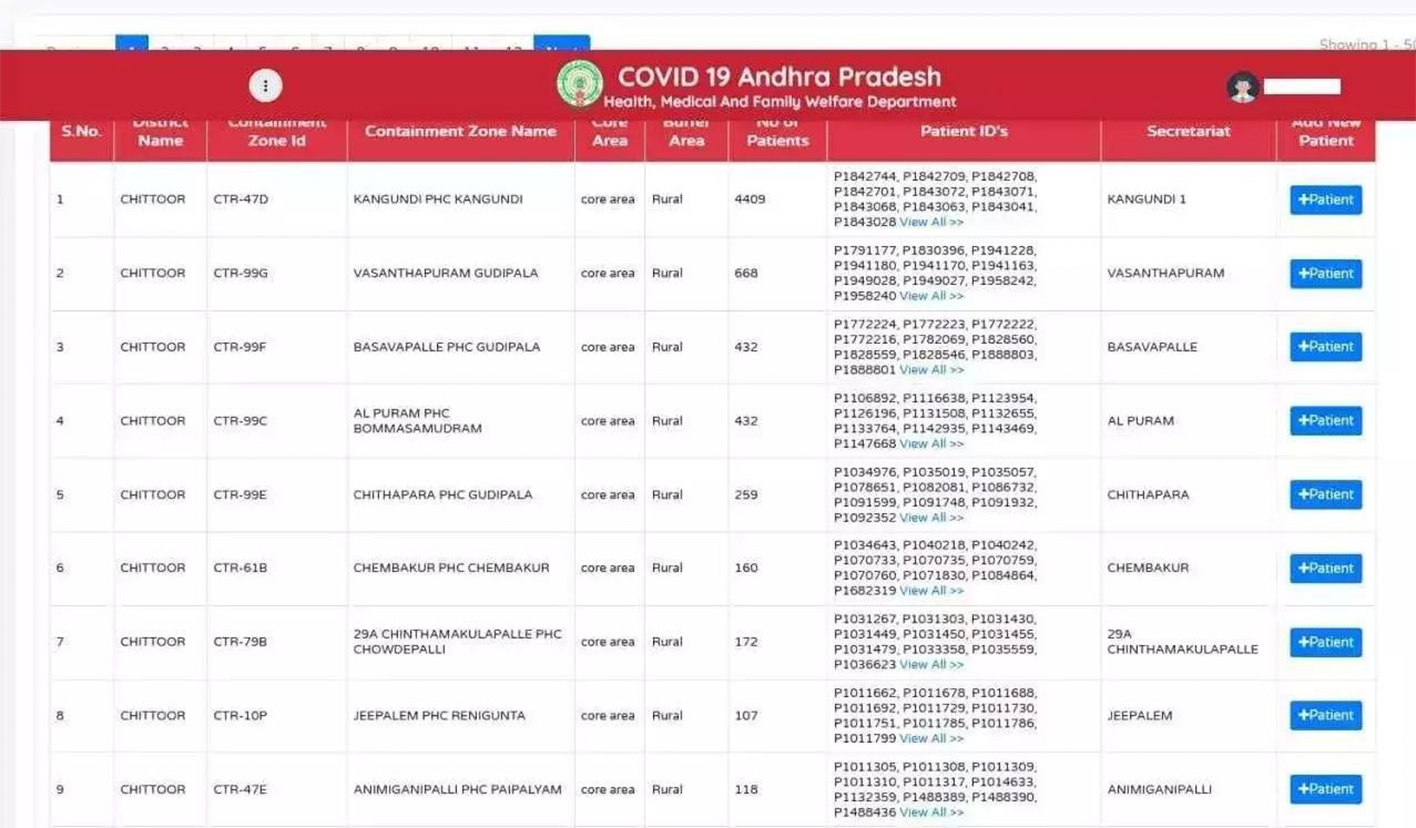
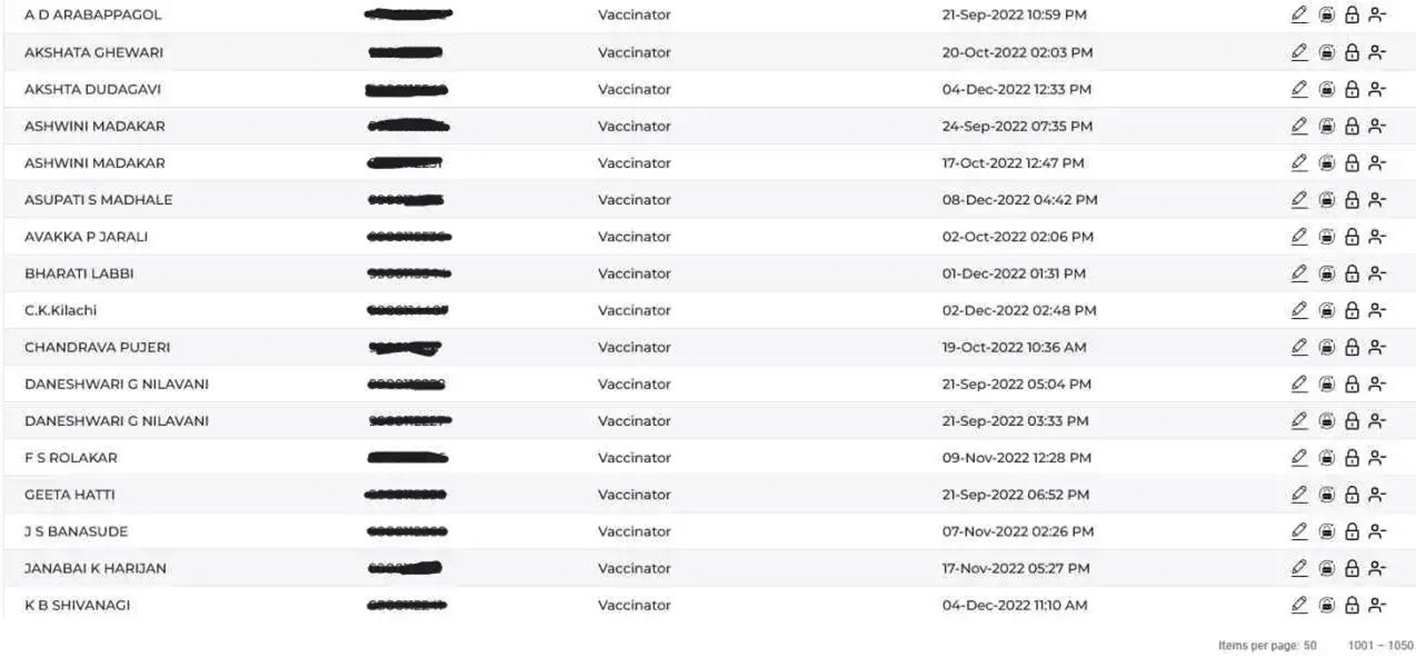
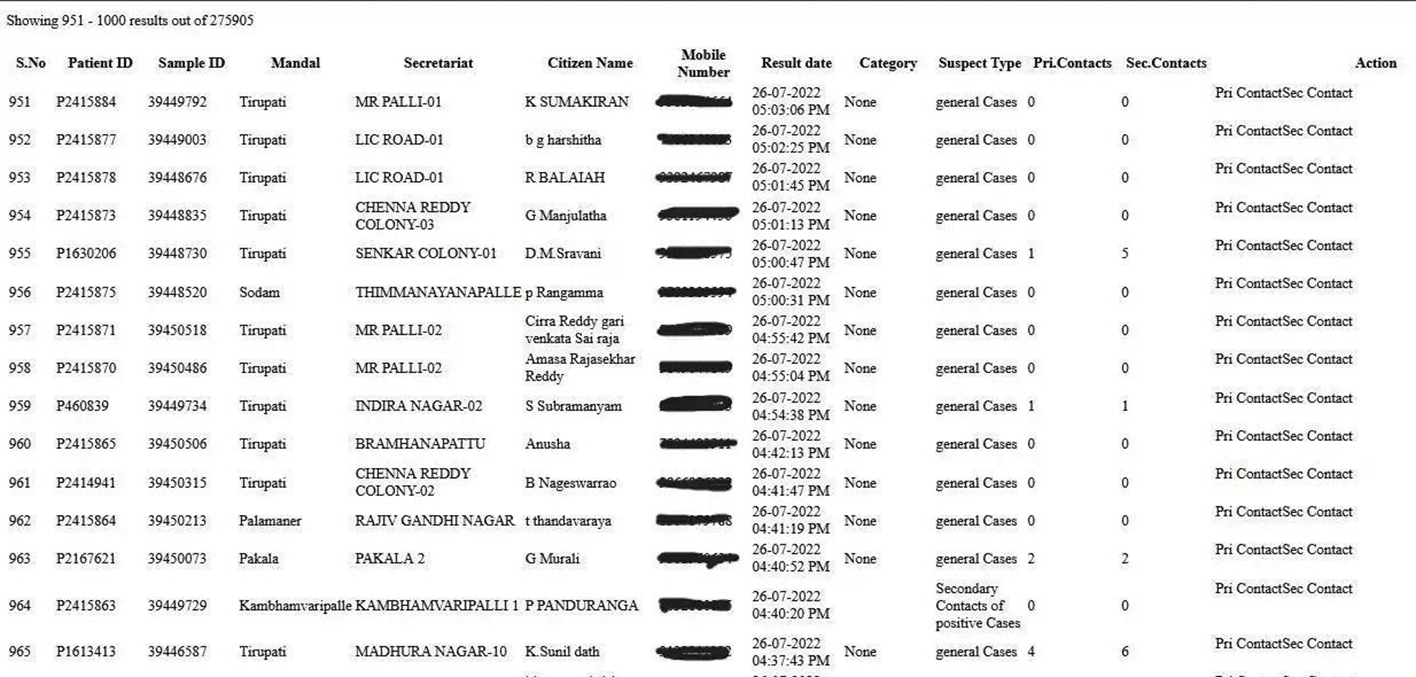
COVID-19 Data Leak
Notably, the incidents of leaked AADHAAR data was new and continues to affect citizens of India. On June 12th, 2023, multiple reports surfaced indicating several records from the CoWin database were leaked by a threat actor, exposing the personal information of individuals registered on the CoWin website for the COVID-19 vaccination. The leaked data included details such as AADHAAR numbers, PAN card information, mobile numbers, and home addresses.
Why is it important?
Resecurity’s findings coincide with a global threat landscape that has seen India emerge as a top-five geography for cyberattacks, according to a recent vendor survey. This survey found that India ranked fourth globally in online banking malware detection and top-five globally in all malware detections in the first half of 2023.
A separate vendor survey of 200 Indian IT decision-makers published in September produced similar findings. This report noted that 45% of Indian businesses experienced more than a 50% rise in disruptive cyberattacks last year – the highest in the Asia-Pacific region. The report also found that 67% of Indian government and essential services organizations experienced over a 50% increase in disruptive cyberattacks.
Fifty-seven percent of IT decision makers at telecom firms worry about ransomware attacks the most. To wit, the more recent October survey found that India bears the highest ransomware incidence in southern Asia. This malicious activity also coincides with an era where India is becoming more geopolitically and economically significant on the global stage.
India is one of the fastest-growing economies in the world, according to the World Bank. With India’s middle class expanding at a 6.3% clip between 1995 and 2021, the fastest-growing segment of the population, it now represents over 30% of the nation. The enhanced domestic earning power, smartphone connectivity, and bank access projected by this demographic trend all make India a much more appetizing target for threat actors.
As such, it’s only logical that Indian PII data would attract proportionally higher interest in the cybercriminal underground. As for nation-state-level threats, China has emerged as India’s greatest regional rival. Despite longstanding tensions with Pakistan, India’s rivalry with its Northern neighbor has increasingly escalated. The United States has “sought to deepen its security and economic relationship with India as the U.S.-China rivalry intensifies,” according to the think tank United States Institute for Peace.
Highlighting these bilateral tensions is Indian Prime Minister Narendra Modi's conspicuous absence from China’s Belt and Road Forum, the third such event hosted by Beijing to promote its ambitious, global infrastructure program. Irrespective of state-sponsored threats, the more immediate danger facing Indian citizens and residents is that many are unaware that their data is being sold online. Furthermore, as early as last month, the Indian government’s official press agency was vociferously defending the reliability and security of Aadhaar data.
The surge in Aadhaar data breaches has also been notably attributed to the current unrest in the Middle East. Hacktivists, capitalizing on the chaos, have intensified their assaults on online resources, subsequently profiting from these infringements by trading the compromised data within the shadowy recesses of the Dark Web.
Beyond text data, cybercriminals are also marketing scanned IDs from breached systems. These stolen IDs heighten the risk of identity theft and fraud, especially in online banking and e-commerce.

Significance
The leak of PII data containing Aadhaar (and other details) of Indian citizens on the Dark Web creates significant risk of digital identity theft. Threat actors leverage stolen identity information to commit online-banking theft, tax refund frauds, and other cyber-enabled financial crimes. Resecurity observed a spike in incidents involving Aadhaar IDs and their leakage on underground cybercriminal forums by threat actors looking to harm Indian nationals and residents.
It is expected to see growth of such data leaks involving AADHAAR records in the future, including those which happened due to the insecurity of 3rd parties.
Organizations like CERT-In (Computer Emergency Response Team of India) dedicate significant efforts to investigate such cases from an incident response perspective to formulate proper guidance on how to contain it. One of the key problems today is the lack of visibility and citizen awareness regarding leaks of their personal information.
In order to build a cybersecure society and safeguard the citizens identity information, it is critical to implement proper identity protection mechanisms with proactive notifications for citizens when such leaks are detected in dark web.
Resecurity notified the affected victims and enabled monitoring of leaked AADHAAR records via the Identity Protection solution and mobile app which is available for Android and Apple iOS.

