Pro-Iranian Nasir Security is Targeting The Energy Sector in the Middle East
Cyber Threat Intelligence


Introduction
Resecurity is tracking a relatively new cybercriminal group called Nasir Security, presumably associated with Iran, that is targeting energy organizations in the Middle East. The energy sector is one of the most impacted areas because of Iranian malicious activity in the region, including the lockdown of the Strait of Hormuz and drone/missile attacks against the energy infrastructure of neighboring countries in the GCC, allies of the US.
Based on the artifacts collected by the threat intelligence team at Resecurity, the group is attacking supply chain vendors involved in engineering, safety, and construction. The data stolen as a result of such incidents is authentic but originates from a third party (of the target company), which may lead to incorrect assumptions about the origin of the breach. Notably, the focus of the attacks is centered on the energy sector, which has experienced significant financial and technological damage since the start of the war in Iran. Cyberspace is used to amplify it, following recent attacks against LNG and logistics providers.
As TTPs, the actors are leveraging business email compromise (BEC) via targeted spear phishing (T1566), impersonation (T1656), and exploiting public-facing applications (T0819), exfiltrating data from insecure cloud storage services (T1530). The identified activity illustrates a combination of supply chain attacks (targeting third parties, such as vendors, contractors) and a disinformation (propaganda) campaign by Iran and its proxies during the war.
Considering the significant pause in the group's activity (since October, 2025), along with the relatively low-profile nature of the group and the absence of social media profiles, the attribution of such activity to a specific actor, party, or country should be done with extreme caution—especially during active geopolitical conflicts. Resecurity expects an increase in 'false flags,' psychological operations (psy ops), and influence campaigns amplifying current events in Iran.
Background
The emergence of groups such as Nasir Security may suggest a collaborative effort by Iran and its proxies to conduct cyberattacks in retaliation. Resecurity is tracking multiple access brokers and cybercriminals engaged by Iran to acquire access and mobilize their offensive cyber capabilities. The actors also plant misinformation, overstating the real impact of their activity.
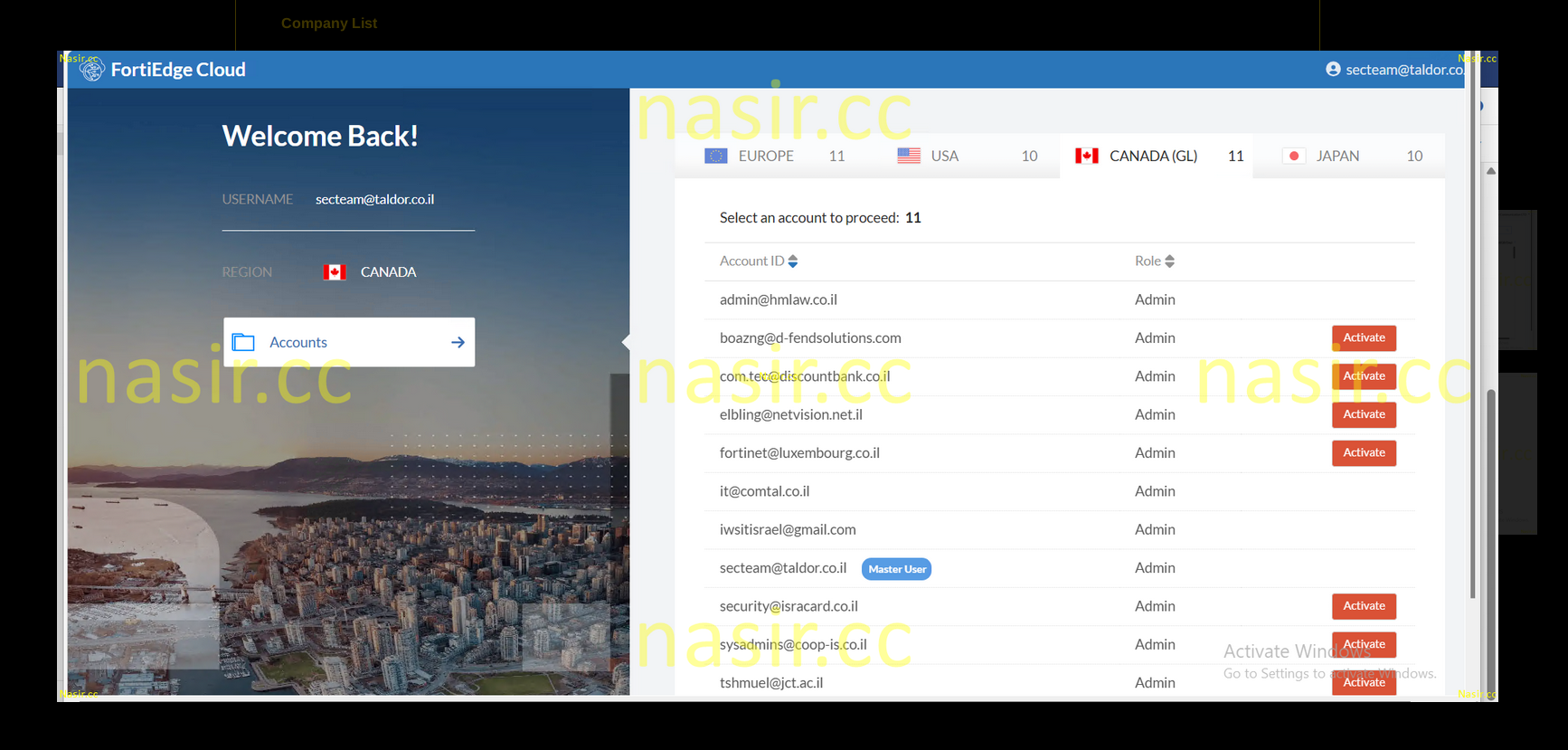
The group emerged around October 5, 2025, and since that time has carried out only one attack—against Taldor, one of Israel's leading IT companies. In this incident, the actors released screenshots confirming unauthorized access to FortiGate Cloud, FortiEdge Cloud, and other IT operations solutions. The group claimed to "find information belonging to Elbit Systems, the IDF, Rafael, the Ministry of Defense, and Mossad within [the victim's] systems..."
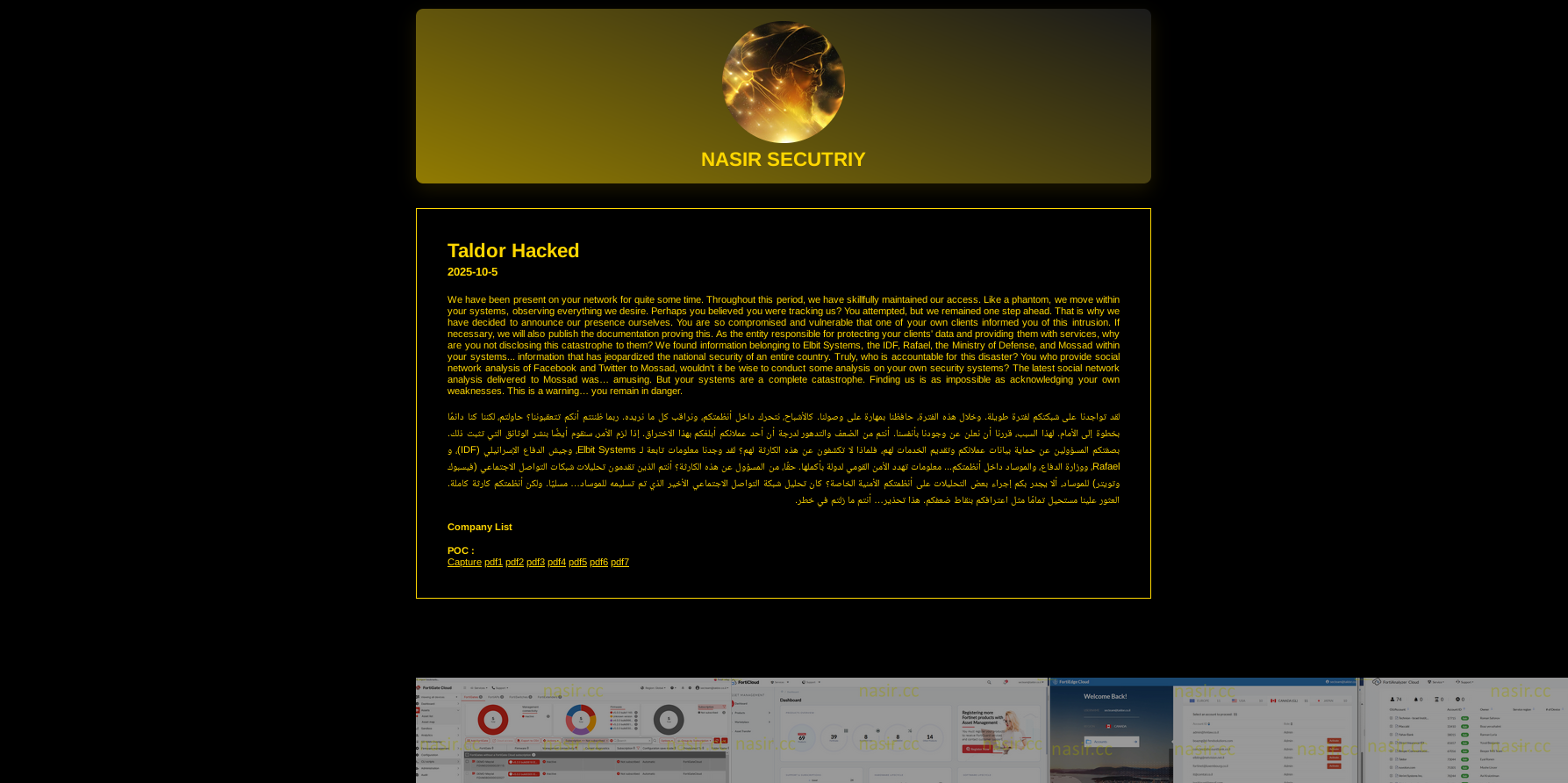
Notably, the breach could also affect third parties, as the affected organization is a major provider in the IT supply chain. That was the first episode in which Nasir Security demonstrated a strong focus on targeting the supply chain to scale malicious cyber activity. Unlikely it could generate severe damage—rather, optics of a major attack targeting Israel. Regardless of published artifacts of compromised remote access by threat actors, there was no confirmed evidence of any risks (including material breaches) to other organizations following these claims. The malicious activity has been contained at an early stage with no further impact.
Proxy Activity
In their first statement, they called themselves "Sons of Hezbollah Lebanon." Such attribution is possible (but not fully confirmed) because the joint actions of the US–Israel coalition have heavily damaged Iran's current cyber capabilities. This is why other actors and groups with similar ideologies may be providing them with cyber offensive support. Based on Resecurity's assessment, the group may include several members from other regions with pro-Iranian ideology but are not directly affiliated with Hezbollah. Resecurity may indicate a broad spectrum of actors involved in the conflict, including mercenaries recruited to conduct attacks.
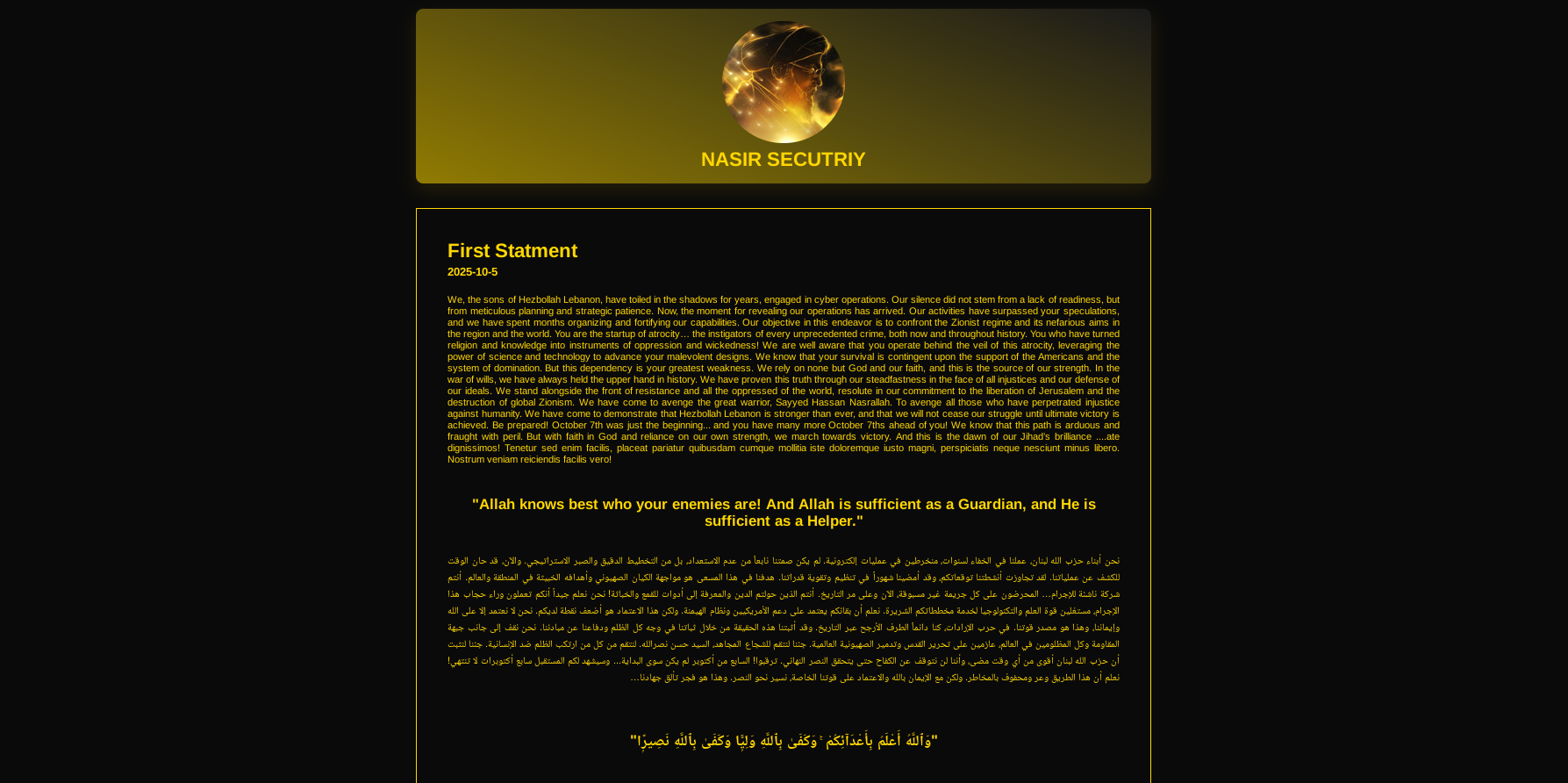
Almost one year later, the group published their mission and new targets—most of which are in the energy (oil and gas) sector. In the updated message, the group attributed themselves as "the Sons of Al-Nusayr," targeting "American, Israeli, and Zionist targets throughout the entire region." Anti-Semitic rhetoric is typical for such actors—it is also used to plant social polarization and conflict via digital media.
Targeted Organizations
The group has targeted Dubai Petroleum (UAE), CC Energy Development (Oman), and an Iraq-based organization in the oil & gas field. The claims, which could be interpreted as fake, were published after a long pause by the group.

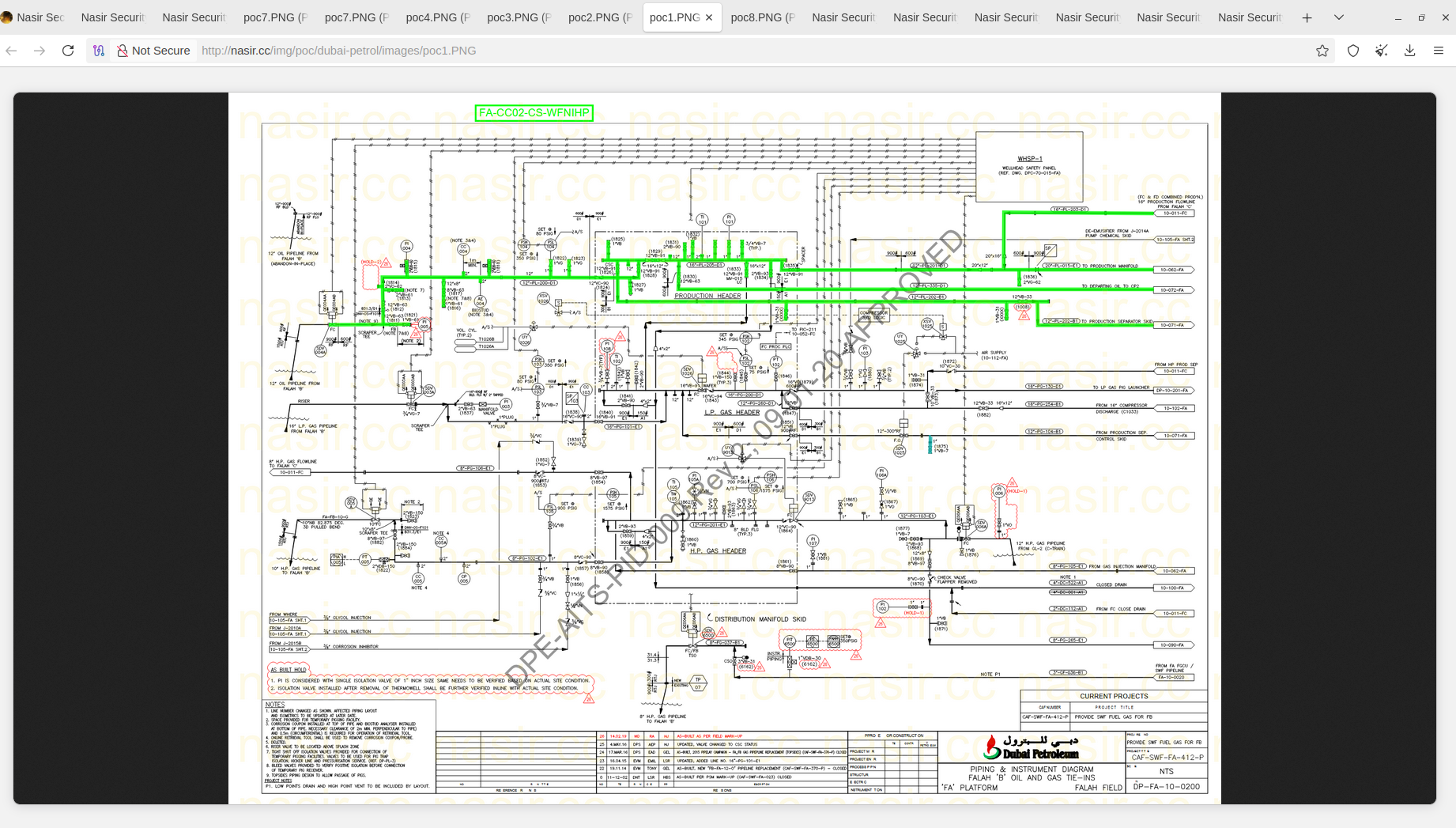
The stolen data includes schemes, contracts, risk assessment reports, and other documents. The group claimed to have exfiltrated over 413 GB of data from Dubai Petroleum, but according to Resecurity's insights, this does not appear to be true. In fact, based on collected intelligence, the data originates from a third party. However, there are still risks associated with this activity, as the documents acquired are authentic and may contain important information for adversaries.
Documents acquired by Iranian threat actors may provide them with additional context and insights to plan further attacks and serve as a pre-positioning stage for targeted strikes against oil fields and pipeline infrastructure. This includes identifying key infrastructure components that, if damaged, would impact the facility and be difficult to repair. Both factors will make recovery from the attack challenging and likely time-consuming, especially since some equipment has long lead times with global supply chain disruptions. Stolen files from contractors could be also used as weaponized attachments containing malicious code.
The leak claims regarding major GCC-based energy companies were published on March 13, 2026. Interestingly, the group accelerated its activity after a long period of silence - since October 5, 2025, there were no updates, which is not common for traditional ransomware or financially motivated cybercriminal groups. The increase in their activity has been observed since the start of the war with Iran.

Based on Resecurity's assessment, the group has not hacked into the above-mentioned organizations directly, but rather their contractors and third parties—part of their supply chain. The group claimed to have stolen over 827 gigabytes of data, which is a clear overstatement compared to the scope of third-party compromise. The actors attempted to capitalize on the authentic documents (stolen from third party), and the complexity of investigating the point of compromise, which can be time-consuming, leaving the audience in uncertainty. Such tactics are widely used by threat actors to plant misleading narratives.
March 21, 2026 - the group has added a new victim to the list: Al-Safi Oil Company (PURE IN), operating gas stations in the Kingdom of Saudi Arabia (KSA) and other regions. In fact, this was the first time Nasir Security had mentioned an organization with a footprint in KSA.

In the new announcement, the group called themselves 'Al-Nasir Resistance'.
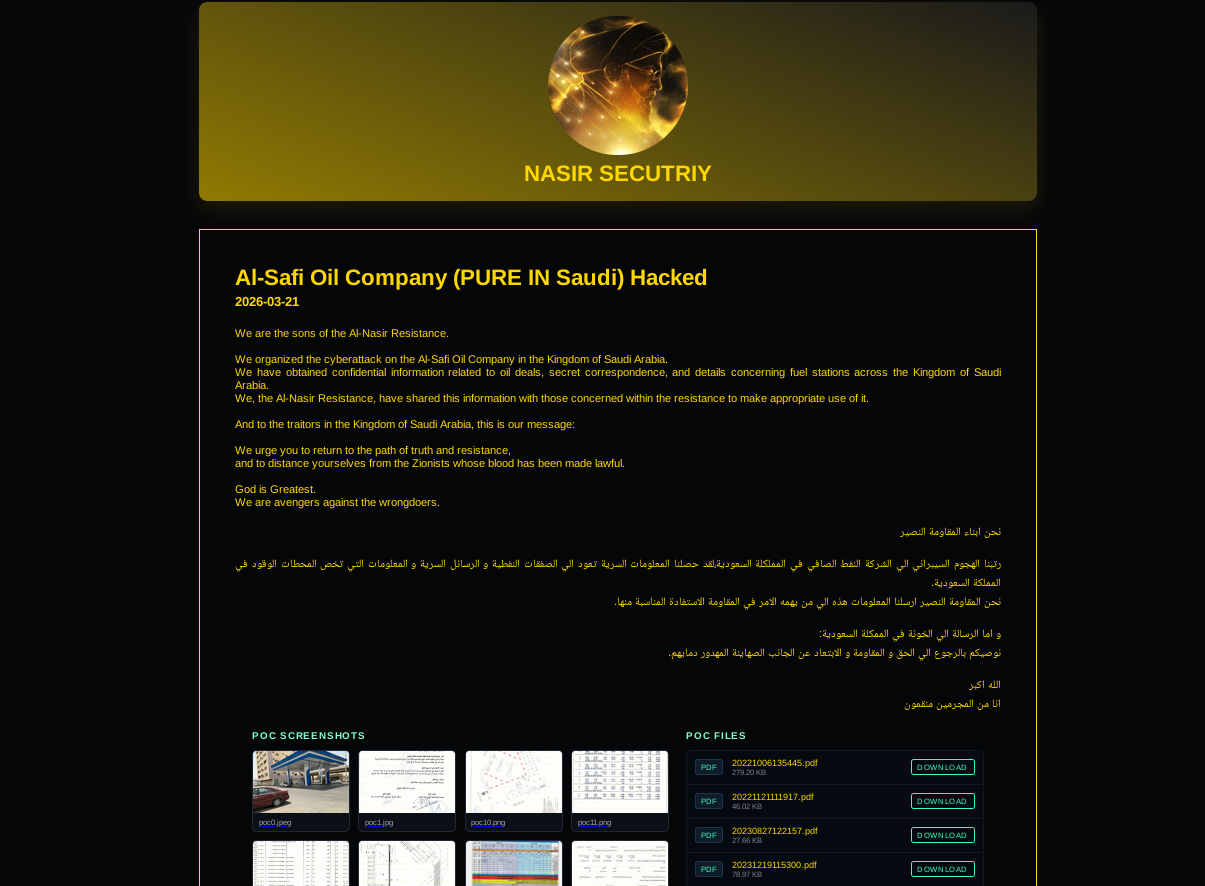
Based on the Resecurity assessment, the data was exfiltrated from a fire alarm and safety equipment vendor rather than directly from the energy company.
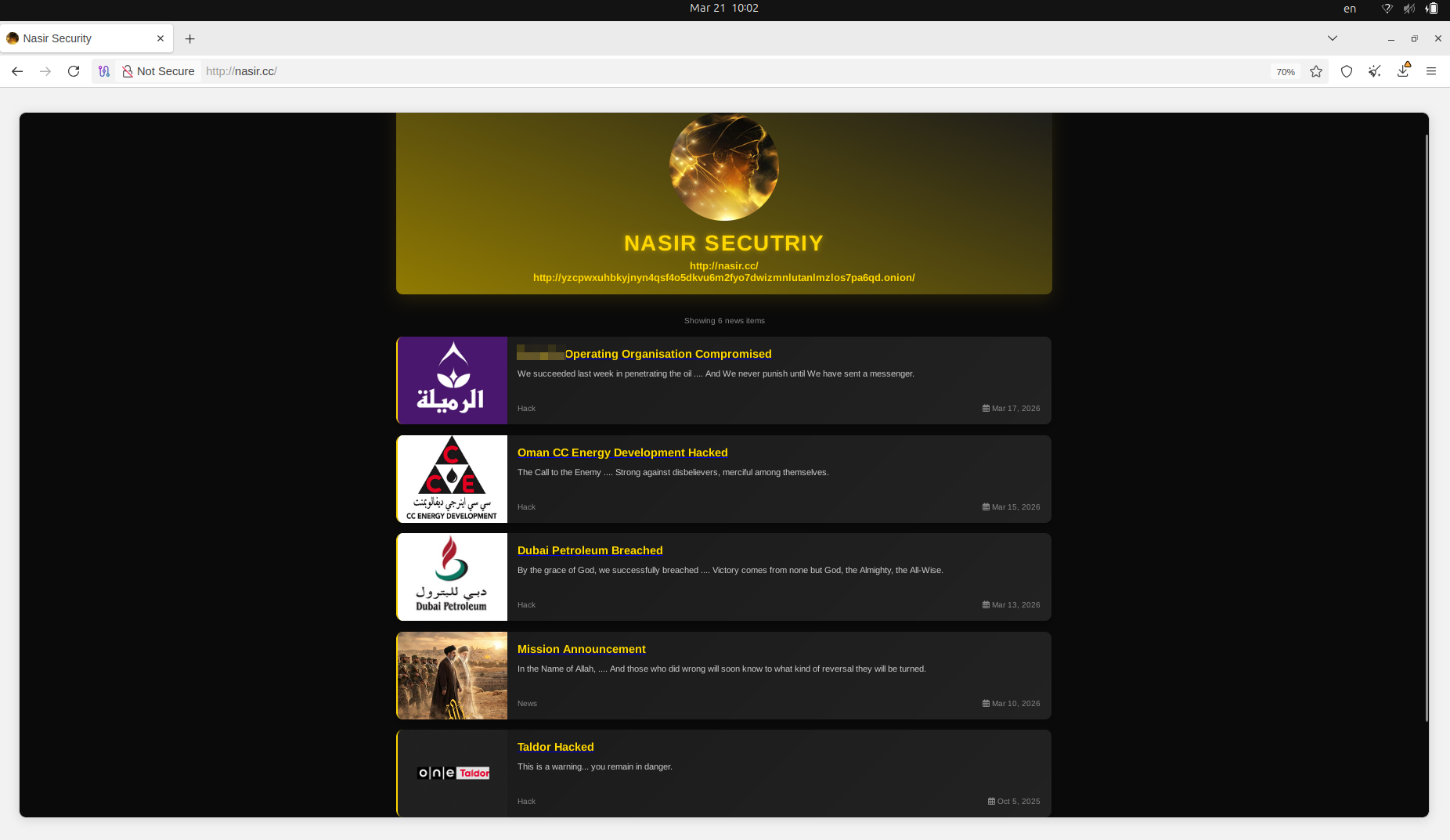
Data Leak Site (DLS)
The Data Leak Site (DLS) of Nasir Security has both a clearnet domain and a TOR mirror. The domain was registered via Namecheap because it accepts cryptocurrency payments.
Clearnet domain:
Domain Name: NASIR.CC
Registry Domain ID: 206658540_DOMAIN_CC-VRSN
Registrar WHOIS Server: whois.namecheap.com
Registrar URL: http://www.namecheap.com
Updated Date: 2025-10-04T11:51:27Z
Creation Date: 2025-10-04T11:51:24Z
Registry Expiry Date: 2026-10-04T11:51:24Z
Registrar: NameCheap, Inc.
Registrar IANA ID: 1068
Registrar Abuse Contact Email: abuse@namecheap.com
Registrar Abuse Contact Phone: +1.6613102107
Domain Status: clientTransferProhibited https://icann.org/epp#clientTransferProhibited
Name Server: DNS1.REGISTRAR-SERVERS.COM
Name Server: DNS2.REGISTRAR-SERVERS.COM
TOR-based DLS:
http[://]yzcpwxuhbkyjnyn4qsf4o5dkvu6m2fyo7dwizmnlutanlmzlos7pa6qd[.]onion
Attribution
The supply chain attacks attributed to Nasir Security are likely carried out by cyber-mercenaries or individuals hired or sponsored by Iran or its proxies. The group's statements contain misleading narratives, with attributions to both "the Sons of Hezbollah Lebanon" and "the Sons of Al-Nusayr."
In the latter case, the actors may be referring to the Nusayris (or Alawites), a sectarian group in Syria and Turkey with a history spanning over 1,200 years, founded by followers of Muhammad ibn Nusayr. Secretive, esoteric beliefs, including the divinity of Ali, reincarnation, and a trinity, characterize them. The sect holds significant power in Syria through the Al-Assad family. From another perspective, by mentioning "Al-Nasir Resistance" in the March 21 update, they may also be aiming to associate themselves with the military wing of the Popular Resistance Committees (PRC), a major Palestinian militant group based in the Gaza Strip.
The naming of some of the groups mentioned is deliberately misspelled, which creates an optics of legitimacy but introduces uncertainty about the actual responsibility of those groups and their involvement. Unlikely, the above-mentioned groups are somehow connected to efforts to compromise energy companies, as they are currently heavily focused on kinetic conflict rather than cyber operations.
Propaganda, Misinformation, Pseudo-Leaks and False Flags
The data leak claims are heavily exaggerated—the group targeted a business email account of a contractor in the Middle East involved in engineering and construction, working with major energy companies. Such campaigns are typical misinformation efforts by Iranian operators and their proxies.
The pattern across all observed claims is an overstated volume of stolen information, with a misinterpreted source for the actual leak. The actors release 8-10 files as samples without releasing the full data. Our threat intelligence team engaged with some of the impacted organizations. It confirmed that they have never been contacted or extorted by the group, which may indicate an ideological rather than a profit-driven motivation. By planting such claims, Iran continues its propaganda efforts via cyberspace to highlight the possibility of a counter-attack against countries in the GCC.
In fact, none of the Iran-linked, pro-Iranian groups and/or state-sponsored groups are making any meaningful impact on the Iran conflict, as confirmed by numerous independent assessments. At the same time, it may highlight supply chain cybersecurity risks and 'low-hanging fruit' (such as vendors and contractors) that Iran could exploit. Resecurity recommends enterprises stay vigilant and accelerate third-party cybersecurity monitoring and vendor risk assessments.
Significance
The IT and OT supply chain is expected to be a high-priority target for Iran, enabling it to generate quantitative rather than qualitative results to demonstrate counteraction during the war, leveraging cyberspace as a critical domain of warfare and psychological operations (psyops).
Our previous Threat Landscape Reporting on recent developments and malicious cyber activity observed during the war with Iran is available at the following URL:
Iran War: Kinetic, Cyber, Electronic, and Psychological Warfare Convergence
https://www.resecurity.com/blog/article/iran-war-kinetic-cyber-electronic-and-psychological-warfare-...

