GEOINT in the Iran War: Targeting, Intelligence, and the Battle for Information Access
Cyber Threat Intelligence


Introduction
The Iran War has ushered in a new era of conflict where the digital and physical domains are deeply intertwined. At the heart of this transformation lies Geospatial Intelligence (GEOINT)—the fusion of satellite imagery, mapping data, and advanced analytics—which has become indispensable for military planning, air strikes, and kinetic operations. GEOINT is a decisive enabler of modern warfare, shaping both offensive and defensive operations.
This threat intelligence brief explores how GEOINT has been operationalized for targeting critical infrastructure, the evolving tactics of Iranian actors in collecting and exploiting geospatial data, the defensive measures taken by commercial imagery providers, and the ongoing underground market for geolocation intelligence. Iranian actors have leveraged open-source, commercial, and underground channels to sustain their targeting capabilities.
GEOINT has compressed the targeting cycle, allowing for rapid identification, precision strikes, and immediate battle damage assessment—reshaping the tempo and transparency of modern warfare. Imagery restrictions by GEOINT providers have altered the intelligence landscape, but have not eliminated the threat.
Operational Use of GEOINT in Air Strikes and Kinetic Operations
GEOINT has been a force multiplier in the Iran War, enabling both U.S.-Israeli and Iranian forces to identify, target, and assess strikes on high-value assets.
Sources
- Commercial Satellite Imagery: Platforms like Planet Labs and Sentinel-2 have provided high-resolution optical and multispectral data for both targeting and post-strike assessment.
- Synthetic Aperture Radar (SAR): Freely available Sentinel-1 SAR data, processed with algorithms like the Pixel-Wise T-Test (PWTT), has enabled near-real-time detection of building-level damage—even when optical imagery is unavailable.
- Classified and AI-Enhanced OSINT: U.S. and Israeli forces have leveraged classified reconnaissance, while Iranian and proxy forces have used AI-tagged open-source imagery to map and classify military assets.
Notable Strike Operations
Target Type |
Example Operation/Outcome |
|---|---|
Nuclear Facilities |
Strikes on Natanz and Isfahan, with visible destruction of enrichment infrastructure |
Missile Complexes |
Attacks on Khojir missile production complex and tunnel entrances, reducing launch capacity |
Oil/Energy Infrastructure |
Strikes on oil depots, refineries, and Kharg Island export terminal |
Data Centers |
IRGC drone strikes on Amazon-owned data centers in UAE and Bahrain |
Command & Control Nodes |
Drone strike on U.S. Fifth Fleet HQ in Bahrain, damaging communications radome (satellite communication terminal) at Naval Support Activity Bahrain |
Note: There were claims of targeting data centers of Oracle and OpenAI (Stargate) located in the GCC, but these claims did not result in any negative kinetic impact. The claims circulated through various Iranian media and social media controlled by proxies.
Iranian Collection and Exploitation of GEOINT
Iranian state actors and proxies have demonstrated sophisticated use of open-source and commercial geospatial tools for reconnaissance and targeting.
Methods of Collection
- Open-Source Mapping Platforms: Iranian operatives have systematically used Google Maps, OpenStreetMap, and Wikimapia to identify and geolocate critical infrastructure, including military bases, oil refineries, and data centers.
- Commercial Satellite Imagery: Platforms like Planet Labs have been used for both pre-strike reconnaissance and post-strike damage assessment, often cross-referenced with open-source maps.
- SAR Imagery: Freely available Sentinel-1 SAR data has been exploited to assess damage to military and civilian infrastructure, especially when commercial providers restrict access.
Case Study: Targeting Data Centers and Oil Facilities
- In March 2026, the IRGC launched kamikaze drone strikes against Amazon-owned data centers in the UAE and Bahrain, marking the first deliberate military targeting of private sector data centers in modern conflict. These attacks were enabled by lists of regional data centers compiled from open-source mapping, commercial satellite imagery, and possibly insider intelligence.
- Iranian drones and missiles have repeatedly targeted oil facilities in Saudi Arabia and the Gulf, with precise geospatial targeting facilitated by satellite imagery and mapping data.
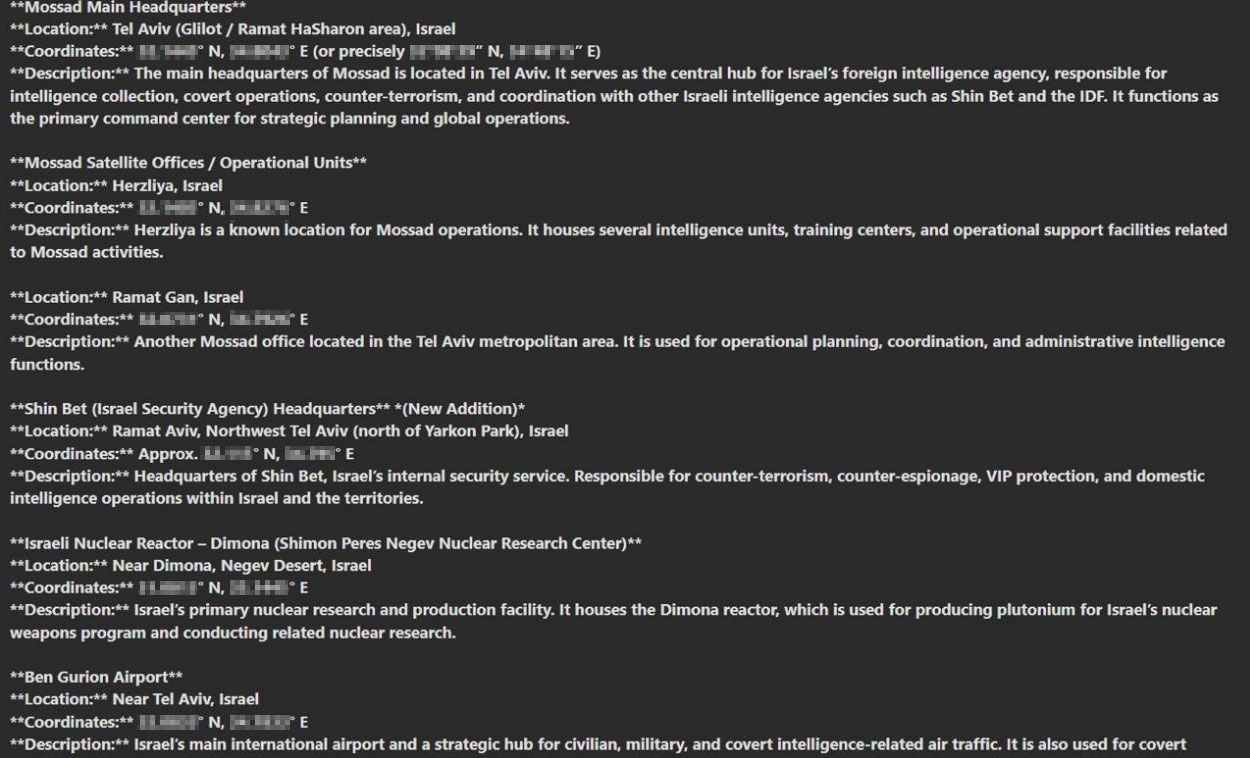
Case Study: Dark Web Activity and GEOINT Data
- Iranian threat actors and their proxies have been actively collecting and sharing coordinates of critical infrastructure in Israel on the Dark Web. Such postings have been identified in traditional cybercriminal underground communities as well as in Telegram groups.
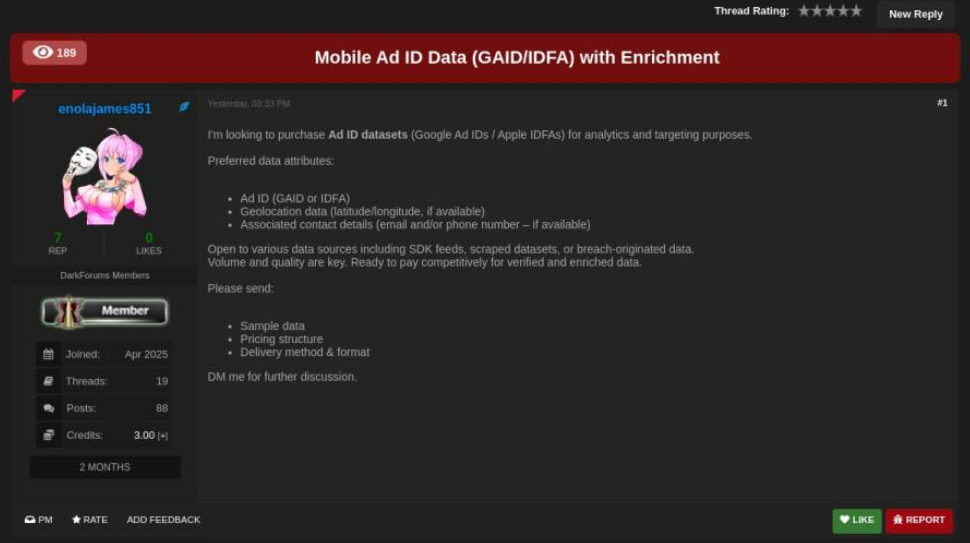
- The shared information reportedly involves geolocation data about key infrastructure assets, posing significant risks to public safety and operational stability. Several actors, presumably associated with Iran, were also interested in acquiring specific records from geolocation data brokers, including ads telemetry—using unauthorized access (infostealer logs and compromised accounts).
- The integration of GEOINT, HUMINT, and dark web activity underscores the adaptability and persistence of Iranian intelligence efforts, even in the face of commercial imagery restrictions.
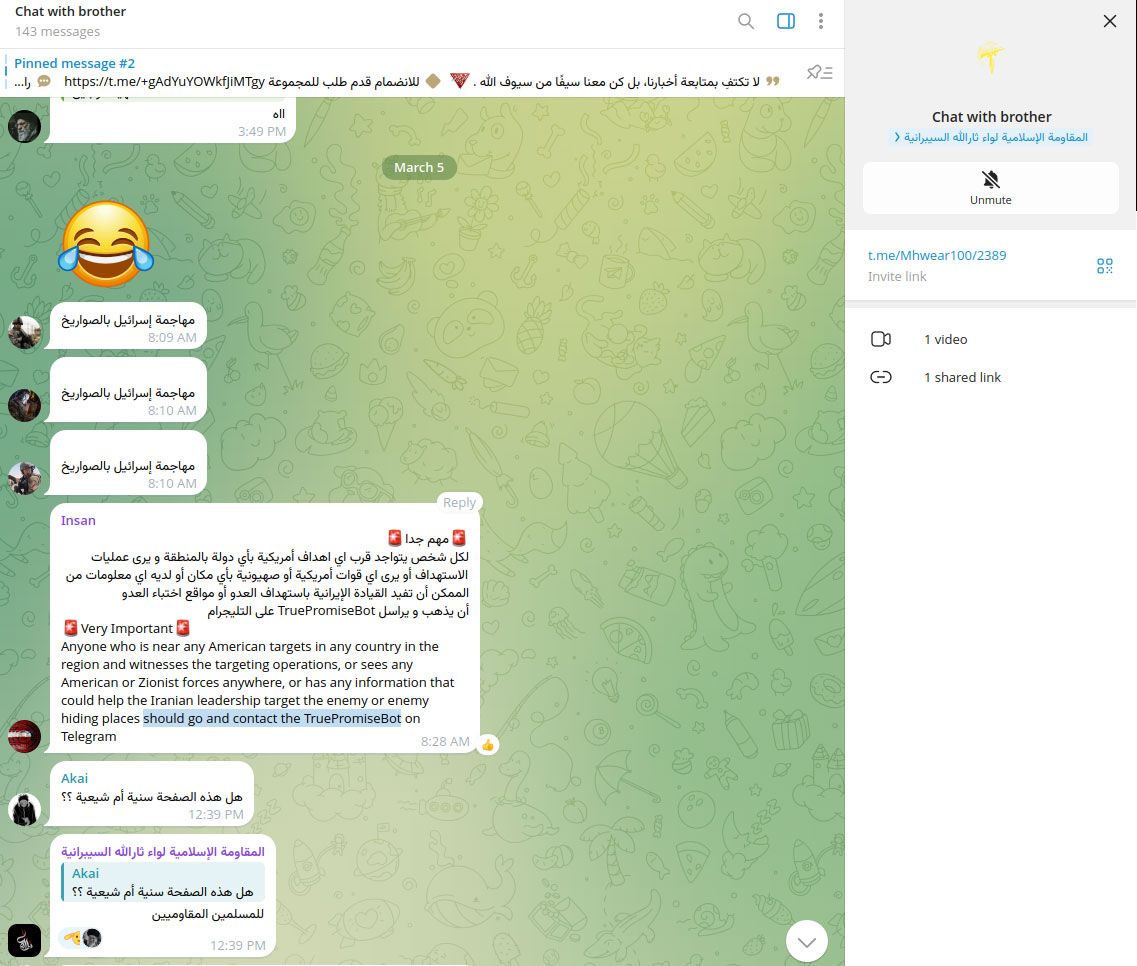
Case Study: Human Intelligence (HUMINT) and GEOINT Data
- Iranian threat actors and their proxies encouraged followers on social media to collect intelligence about the U.S. and Israeli forces abroad, which shows Human Intelligence (HUMINT) gathering efforts by Iran.
- HUMINT is used to collect GEOINT and location data by tasking human sources—such as informants, operatives, or local contacts—to observe, report, and sometimes physically record the locations, layouts, and activities of targets.
- This information is then integrated with technical geospatial data (from satellites, drones, or mapping tools) to create a more accurate and actionable intelligence picture, which is crucial for planning and executing airstrikes and other military operations.
GEOINT Provider Response: Imagery Restrictions and Blackouts
The weaponization of commercial GEOINT has forced providers to adapt their policies during active conflict. The interplay between Iranian reconnaissance and GEOINT provider restrictions has created a dynamic intelligence environment, with both sides adapting rapidly to changes in data availability.
Restriction Measures
- Imagery Blackouts: Providers such as Maxar Technologies and Planet Labs have restricted, blurred, or delayed the release of high-resolution imagery over sensitive sites during periods of heightened military activity.
- Reliance on SAR Data: With commercial optical imagery restricted, analysts and open-source investigators have increasingly relied on freely available SAR data (e.g., Sentinel-1) for independent assessment and verification.
- Policy and Security: These restrictions align with both internal provider policies and, in some cases, government mandates to prevent exploitation of commercial GEOINT for targeting purposes.
Provider |
Restriction Type |
Impact on Analysis |
|---|---|---|
Maxar Technologies |
Blurring/Blocking |
Limited real-time assessment of strikes |
Planet Labs |
Delayed Imagery Release |
Reliance on SAR and open-source data |
Sentinel-1 (ESA) |
Open Access SAR |
Primary source for damage proxy mapping |
The Dark Web and HUMINT: The Underground Market for GEOINT
Despite imagery restrictions, Iranian actors have turned to underground channels to sustain their intelligence efforts.
Dark Web Activity and HUMINT Acquisition
- Underground Forums: Iranian government contractors and proxies actively mine closed-trust communities and dark web marketplaces to recruit individuals with access to sensitive GEOINT, including physical location data and infrastructure blueprints.
- HUMINT Recruitment: Iranian APT groups (APT35, APT34, Tortoiseshell) use social engineering—fake job offers, journalist solicitations, and impersonation—to approach potential insiders and extract valuable information.
- Contractor Networks: Iran’s cyber operations are structured around a competitive contractor model, incentivizing aggressive pursuit of high-value intelligence, including GEOINT.
- Threat Intelligence: Cybersecurity firms have documented Iranian campaigns targeting energy, government, and critical infrastructure sectors, with a focus on acquiring data that could facilitate physical attacks or sabotage.
Location data (for sale) is not limited to traditional geospatial data but also includes digital telemetry produced by software applications, which may contain device identifiers and other artifacts used for tracking, geofencing and analytics. The location-enriched records could be generated by consumers' mobile devices, but also by IoT devices and industrial equipment using GNSS (GPS, GLONASS (Russia), Galileo (EU), and BeiDou (China).
Resecurity identified several underground brokers monetizing illegally obtained geolocation data on the Dark Web, as well as foreign threat actors seeking to acquire it. This activity may not only violate the privacy of consumers but also pose national security risks for enterprises operating in sensitive areas (government / military) and critical infrastructure.
Conclusion
The Iran War has demonstrated the centrality of GEOINT in modern conflict—enabling precision targeting, rapid damage assessment, and adaptive campaign planning. Iranian actors have exploited every available avenue, from open-source mapping tools to dark web forums, to collect and operationalize geospatial intelligence against critical infrastructure. The response by commercial GEOINT providers—restricting access to sensitive imagery—has forced a shift toward alternative data sources and underground acquisition methods. As the conflict continues, the battle for information access remains as contested as the physical battlefields themselves, with profound implications for the security of digital and physical infrastructure across the region.
Resecurity predicts that the convergence of GEOINT, SIGINT, HUMINT, and Cyber Operations (CYBERINT) will become increasingly prominent and decisive in future local conflicts, with lessons from Ukraine and Iran providing a blueprint for what to expect in other regions. Enterprises, especially those involved in critical infrastructure such as defense, energy, transport, logistics, and telecommunications, should consider this risk and implement additional defensive measures to minimize the exposure of location-enriched records of their staff and facilities. Such data could be acquired by foreign threat actors for malicious targeting.

