Iran War: Kinetic, Cyber, Electronic and Psychological Warfare Convergence
Cyber Threat Intelligence


Executive Summary
On Saturday morning (2/28/26) in Iran, a joint Israel-US military action began another chapter in the Middle East conflict. Still, this one is claiming a goal of regime change and dramatically altering the political map of the Middle East and the global order. Iran is retaliating with ballistic missiles and drone strikes against Israel and its Persian Gulf neighbors, and it is much larger than June’s military operations. The US has an impressive naval and air armada in position and is clearly employing these assets to great effect. US military bases in the region have been targeted, and President Trump has warned the nation to expect casualties. That led to an expected spike in cyber activity against Iran, US interests, and others.
The situation remains highly kinetic as the U.S. and Israel continue operations and Iranian retaliatory actions persist across the region. Following the death of Ayatollah Ali Khamenei, Iranian President Masoud Pezeshkian stated Iran’s consideration of seeking justice and retaliation against perpetrators as a duty and legitimate right to be pursued with full determination. President Donald Trump released a video message stating military operations will continue “until all of our objectives are achieved.”
Iran continued to launch missiles and drones against civilian and military infrastructure, with explosions reported in Bahrain, Kuwait, Iraq, Saudi Arabia, the United Arab Emirates (UAE), Israel, and Qatar. Major airspace across the Middle East, including Iran, Israel, Kuwait, Qatar, Bahrain, the UAE, Iraq, and Syria, remains challenging, leading to widespread flight cancellations and diversions.
There has been a notable surge in electronic warfare and cyber activity following the recent US-Israeli strikes on Iran. These activities involve both Iranian-aligned hacktivist groups and pro-Western hacktivists, with cyberattacks targeting critical infrastructure, military logistics, and symbolic websites. However, cyberattacks are just one way both sides are using offensive cyber capabilities. Both sides are also employing cyber reconnaissance for kinetic targeting and kinetic action battle damage assessment. The escalation reflects the broader cyber threat landscape, which is often coordinated with kinetic military actions.
Notable Security Events Observed
- The U.S. advised Americans to immediately leave Bahrain, Egypt, Iran, Iraq, Israel, Jordan, Kuwait, Lebanon, Oman, Qatar, Saudi Arabia, Syria, the UAE, and Yemen, following the escalating Iranian strike and prior to the U.S. conducting “even more punishing” strikes on Iran.
- The U.K., along with Germany, Slovakia, and Czechia, has announced its intention to conduct evacuations for citizens in the region, scheduling flights from Riyadh, Saudi Arabia; Muscat, Oman; and Amman, Jordan. This will affect digital and cyber defense efforts, as expats doing this work may be unable to work in person or may only be able to work remotely. If performed remotely, it will also expand the attack surface for the victims and target-related companies.
- The Israel Defense Force (IDF) issued an evacuation order for 80 towns in southern Lebanon, amid limited ground operations. Triggered by Hezbollah rocket and missile salvos targeting Israel.
- Kataib Hezbollah issued a statement claiming U.S. and Israeli forces deployed from Jordan, increasing the risk of terror attacks against Jordan and Jordanian-linked assets.
- The U.S. destroyed all eleven major Iranian Navy assets present in the Gulf of Oman. Although the major surface vessels have been destroyed, the threat from missiles, aerial, and surface drones in the Gulf of Oman and Strait of Hormuz remains present.
- Iran has targeted key oil export infrastructure, including Fujairah, UAE, and Duqm and Salalah ports in Oman, as part of its wider retaliatory campaign following U.S. and Israeli strikes on Iranian territory. These attacks signal an expansion in Iran’s targeting profile from military and diplomatic sites to include energy infrastructure in Gulf states.
- Ground sources in Iraq reported mass pro-Iran demonstrations, with heightened civil unrest concerns across Baghdad, Basra, Dhi Qar, and other southern governorates. Assets in the country highlighted an increased risk of attacks on high-profile hotels and civilian-adjacent sites in the Kurdistan Region, triggered by Iranian targeting of Kurdish populations and the broader region.
- Multiple Pakistani television channels, websites, and mobile applications were targeted in coordinated cyberattacks, prompting the National Computer Emergency Response Team (CERT) to launch a formal investigation.
- At least three Amazon data centers have been damaged by Iranian drone strikes in the UAE and Bahrain. Several other organizations, including the U.S. Consulate in Dubai, were targeted.
- Multiple drones originating from Iran struck the Nakhchivan exclave of Azerbaijan, hitting the local international airport and a school, causing four injuries. Azerbaijan condemned the attack as a "terrorist act" by Iran, ordered the evacuation of its diplomatic staff from Tehran, and promised a "military response".
- U.S. Navy strikes hit three Iranian vessels in the Persian Gulf.
- Increased counterintelligence activity: Iraq arrests a spy ring of intelligence agents carrying Polish passports (reported by Sabreen News Agency); similar claims are circulating that the Kingdom of Saudi Arabia and Qatar are detecting possible espionage activity.
- Drones and rockets have been launched at the US embassy in Iraq's capital, Baghdad, in what's been described as "the most intense assault".
- The military conflict is escalating in Lebanon, targeting Hezbollah. Iran has warned Israel against “full-scale military aggression” in Lebanon and said it would lead to an “obliterating war”.
- UAE suspends Shah gas field operations after drone attack. Dubai flights were disrupted after another drone attack near the airport — similar attacks targeting oil and gas infrastructure have been conducted in the region. The French oil leader TotalEnergies announced that it has lost 15% of its oil and gas output as the U.S.-Israeli war with Iran shuts fields across the Middle East, including in the UAE, Qatar and Iraq.
- The Strait of Hormuz, a critical chokepoint in global oil, natural gas, and fertilizer trade, has been closed by Iran. The conflict pushes importers into energy triage as they conserve power and curb soaring prices.
- Israel and the US have targeted Iran’s energy facilities, including oil depots in Tehran, as well as military sites on Kharg Island, a vital port for Iran’s oil exports.
- Iran’s retaliatory attacks have targeted several sites across Israel as well as oil refineries, US military bases, airports, and commercial shipping across the six Gulf states and beyond.
- The Islamic Resistance in Iraq, an umbrella group of Iran-backed armed factions, claimed responsibility for downing a U.S. military refueling aircraft in western Iraq. Iran’s strategy involves widening the conflict geographically, using Iraq as a launchpad.
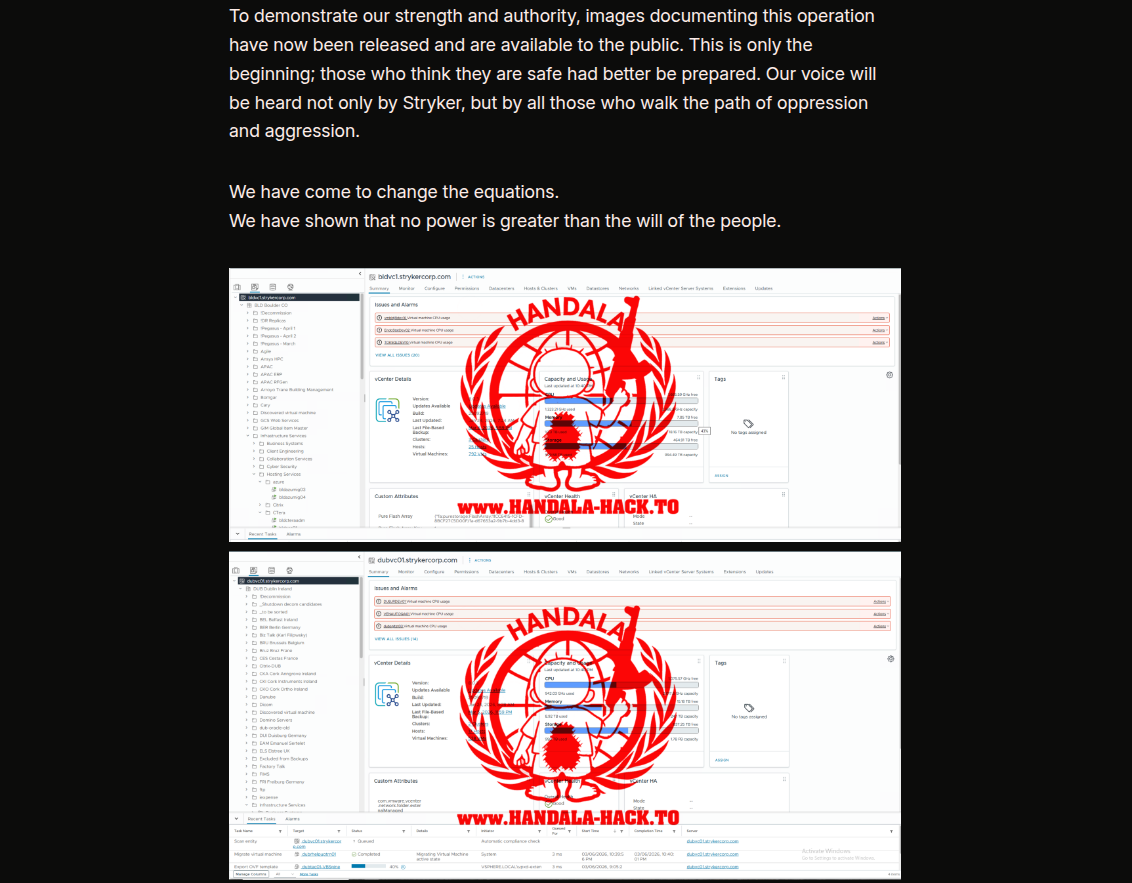
- Iran has declared all US financial institutions and other tech and multinational companies in the Middle East as justified targets. One of the most notable recent activities—Iran-linked hackers carried out a cyberattack on Stryker Corporation, a U.S.-based medical technology company, on March 11, 2026. The attack was claimed by a pro-Iranian hacking group called Handala, which stated that it was in retaliation for a missile strike on an elementary school in Minab, Iran. Stryker's global network was severely disrupted, with employees across multiple countries unable to access systems.
Conflict Map
The Iran war in early 2026 is a multi-front, region-wide conflict involving direct US and Israeli strikes on Iran, widespread Iranian retaliation, and proxy warfare. The conflict map is highly dynamic, with active combat, missile attacks, and maritime disruptions across the Middle East.
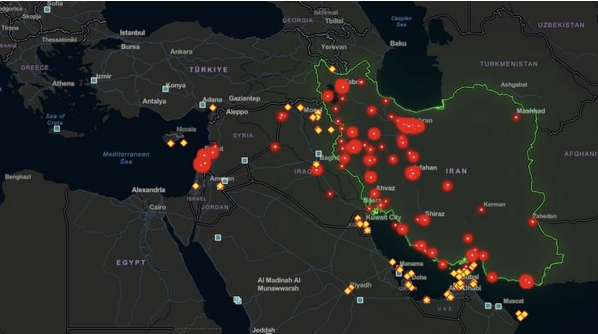
The conflict map of the current Iran war (March 2026) shows Iran under sustained air and missile attack from the US and Israel, with major strikes concentrated on Tehran, strategic oil and military infrastructure, and border provinces. Simultaneously, Iran and its proxies (Hezbollah, Houthis, Iraqi militias, Hamas) are launching retaliatory attacks on Israel, US bases, Gulf states, and commercial shipping. The map features multiple geographic flashpoints: within Iran; across Lebanon, Syria, Iraq, and Yemen; in Gaza; and in critical maritime zones such as the Strait of Hormuz and the Red Sea.
Key Activities Observed
1. DDoS Attacks and Reconnaissance
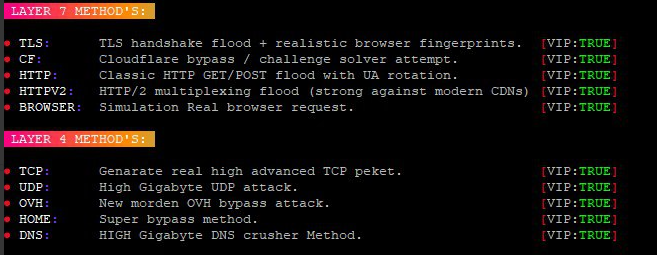
- Hacktivist groups, including Iranian-aligned actors, have initiated Distributed Denial of Service (DDoS) attacks and reconnaissance operations targeting US and Israeli assets. These attacks aim to disrupt services and gather intelligence for further operations.
- These activities are consistent with Iranian-aligned threat actors and hacktivist groups, signaling a coordinated response to the strikes.
- In many cases, such claims generate a lot of 'noise' and require a reallocation of limited defenses, and not actual damage. The observed DDoS campaigns were highly disorganized and used primitive tools to generate malicious traffic. Such attacks have been conducted against government and private-sector organizations in the UAE, Bahrain, the Kingdom of Saudi Arabia, Jordan, and Oman.
- Based on Resecurity's assessment, Iran lacks the capacity to generate DDoS attack volumes required for a significant impact and has had to engage with hacktivists and third-party underground services. Many of these actors have refused to provide any services.
- Cyber operations center in Iran, associated with the Islamic Revolutionary Guard Corps (IRGC), was bombed during the ongoing Iran war (compound in eastern Tehran). This compound reportedly included the Cyber Warfare headquarters of the IRGC and elements of its intelligence directorate.
In fact, many of the activities are driven by the same alliances built in 2024-2025, nicknamed the Islamic Resilience Cyber Axis, a conglomerate of several ideologically motivated groups. These actors are actively recruiting new members to their movement and can generate influence campaigns via social media, including the use of artificial intelligence (AI).
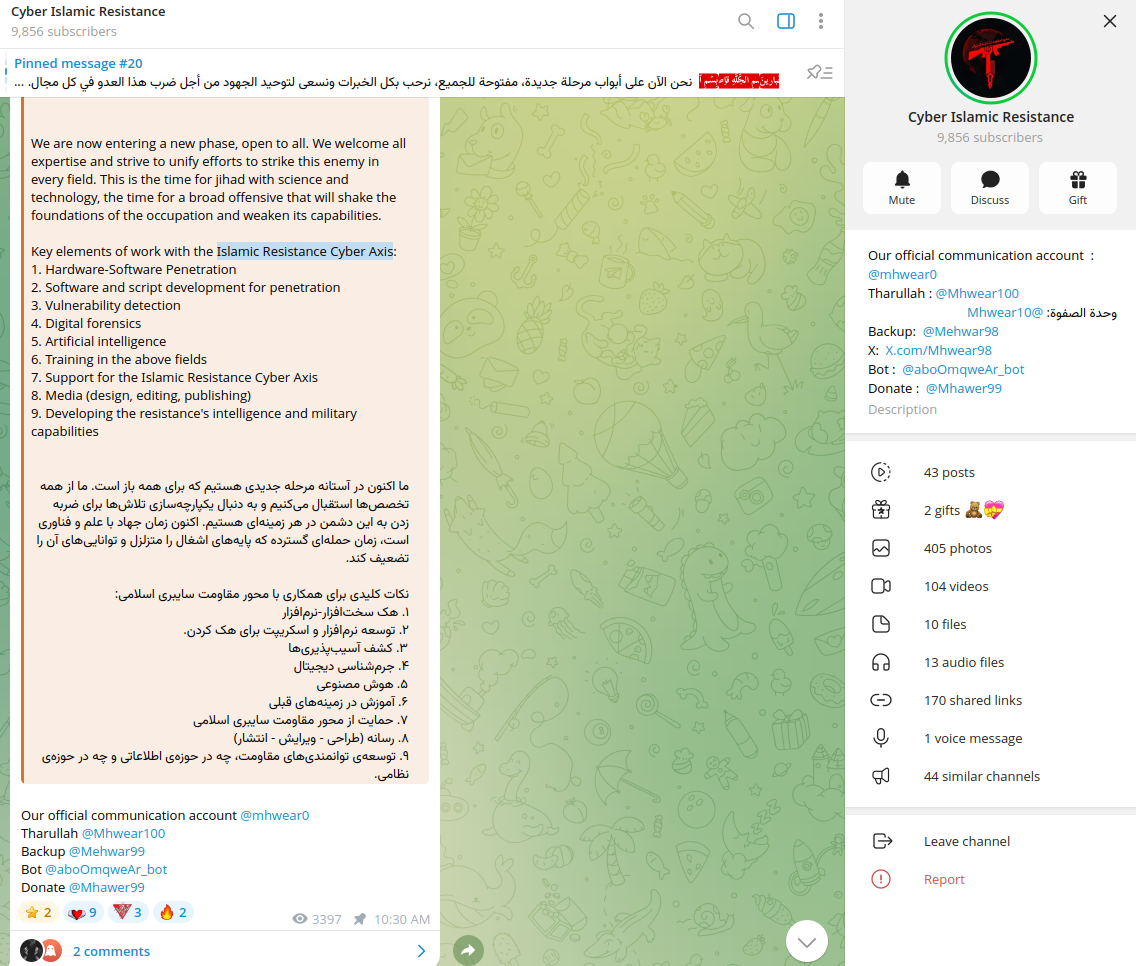
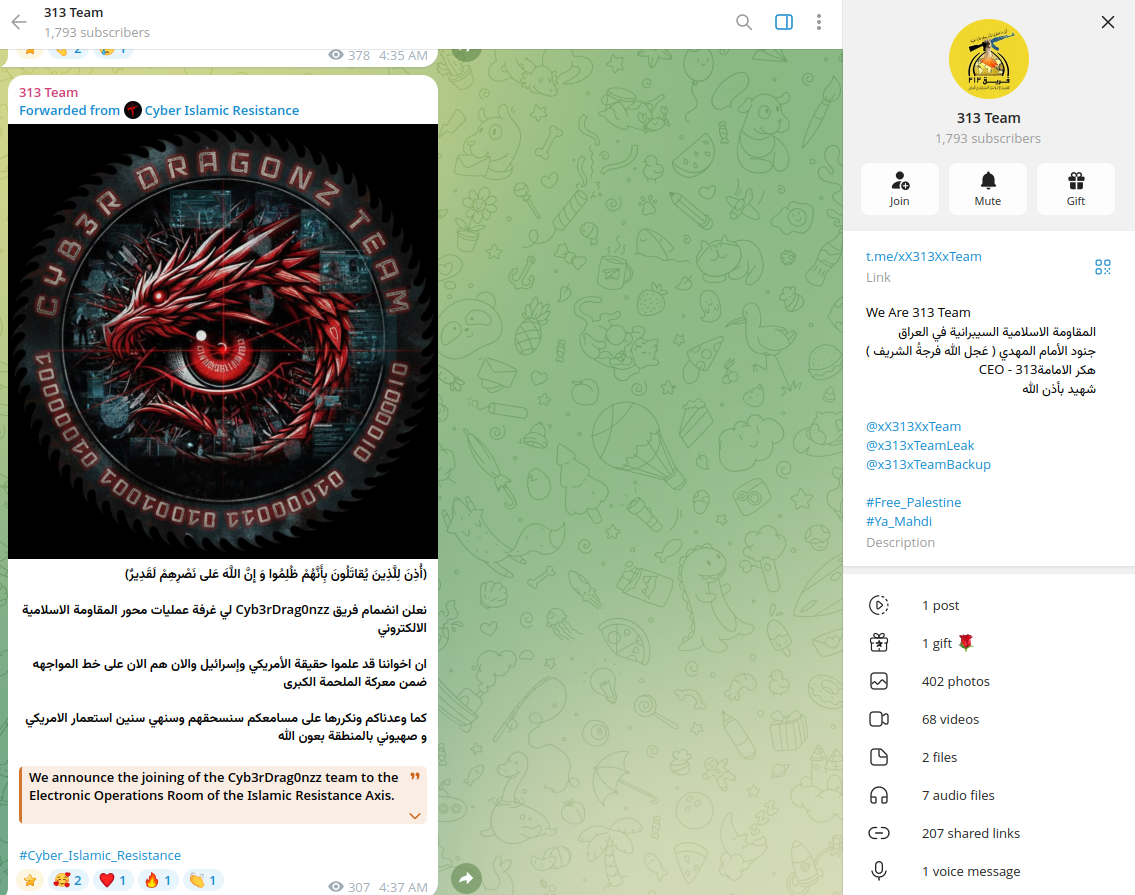
One of its subdivisions, the Electronic Operations Room, is responsible for malicious cyber activity. These actors are often associated not only with Iranian but also with pro-Hamas groups. The ecosystem of such groups is extremely dynamic and may involve actors from other geographies joining them who follow a similar ideology.
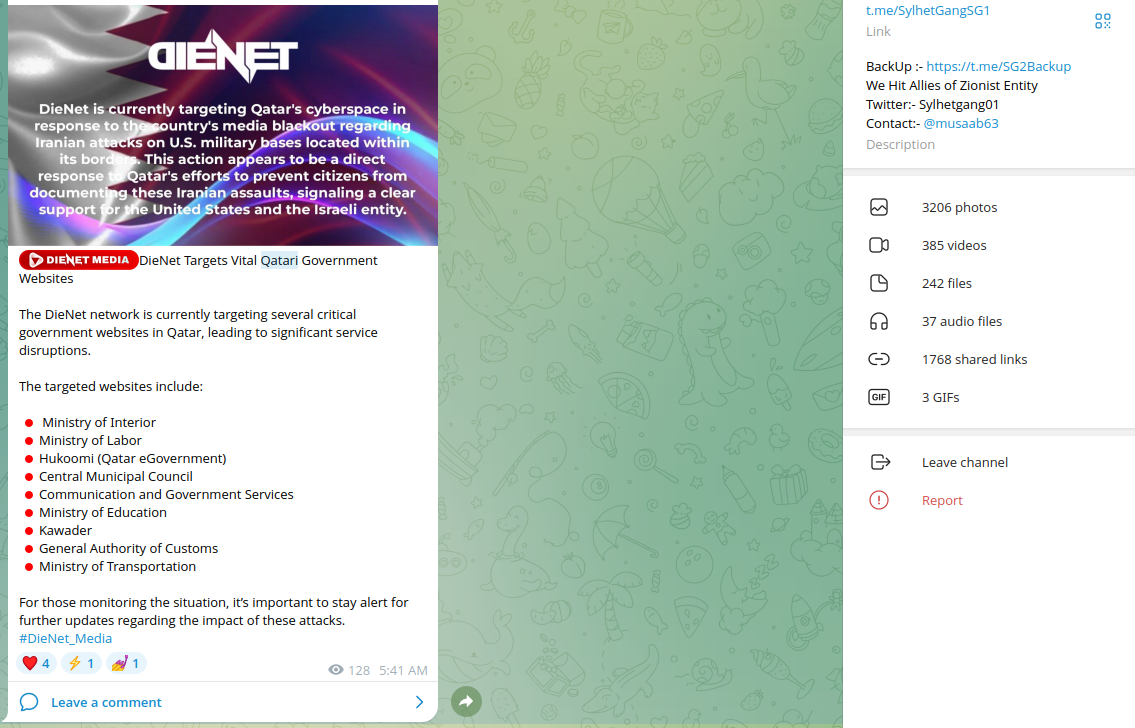
Notably, the hacktivist activities observed were targeting not only Americans and Israeli resources but also countries with political establishments loyal to Iran. The beginning of the conflict led to social polarization within hacking communities due to attacks on American military bases by Iran located in the region. The activity could be interpreted as chaotic, with sudden claims of attacks against countries in the GCC and even the EU.
Multiple e-government resources in Kuwait have been targeted by pro-Iranian groups.
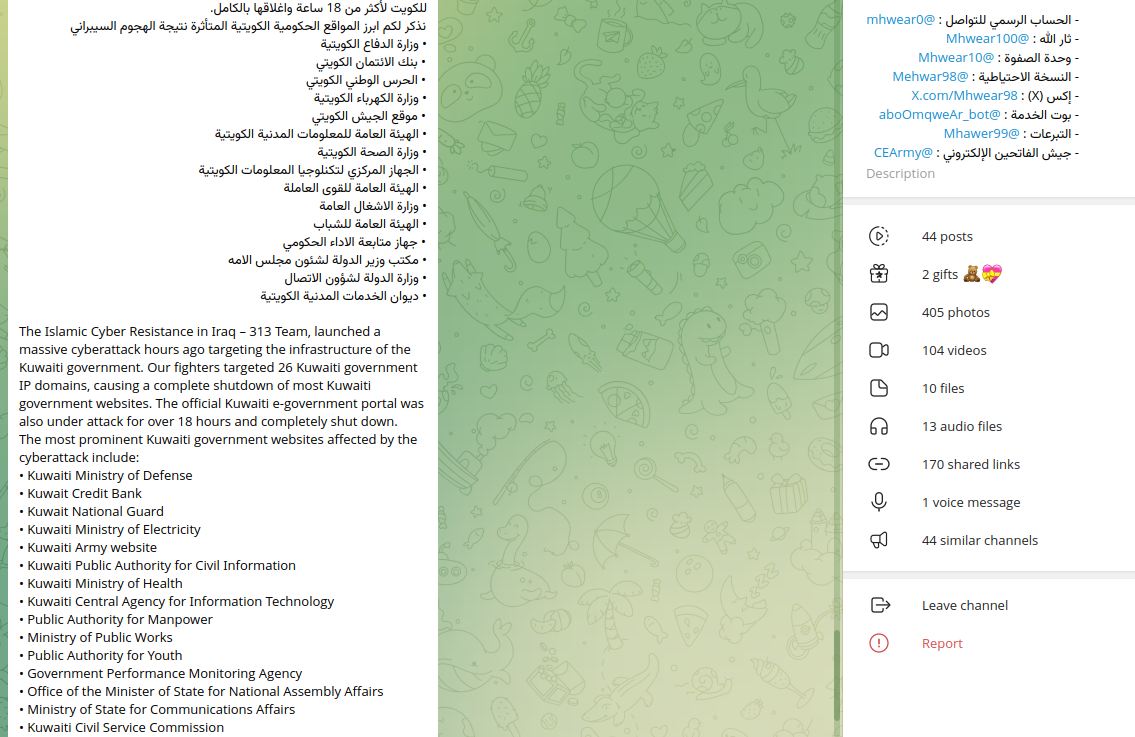
Similar attacks have been arranged against Jordan and KSA. Notably, not all these claims could be interpreted as material. In many cases investigated by Resecurity, the attacks did not cause any meaningful impact or were not even executed.
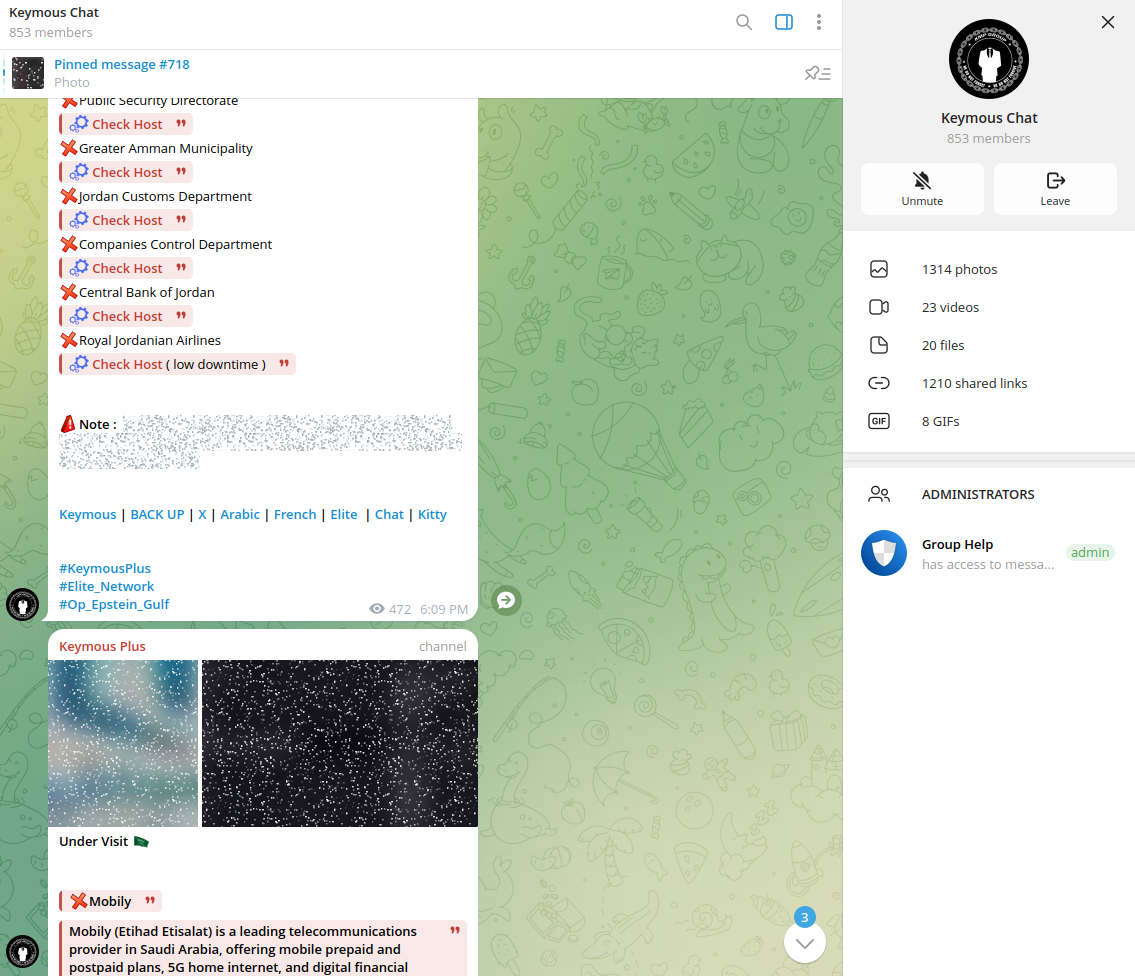
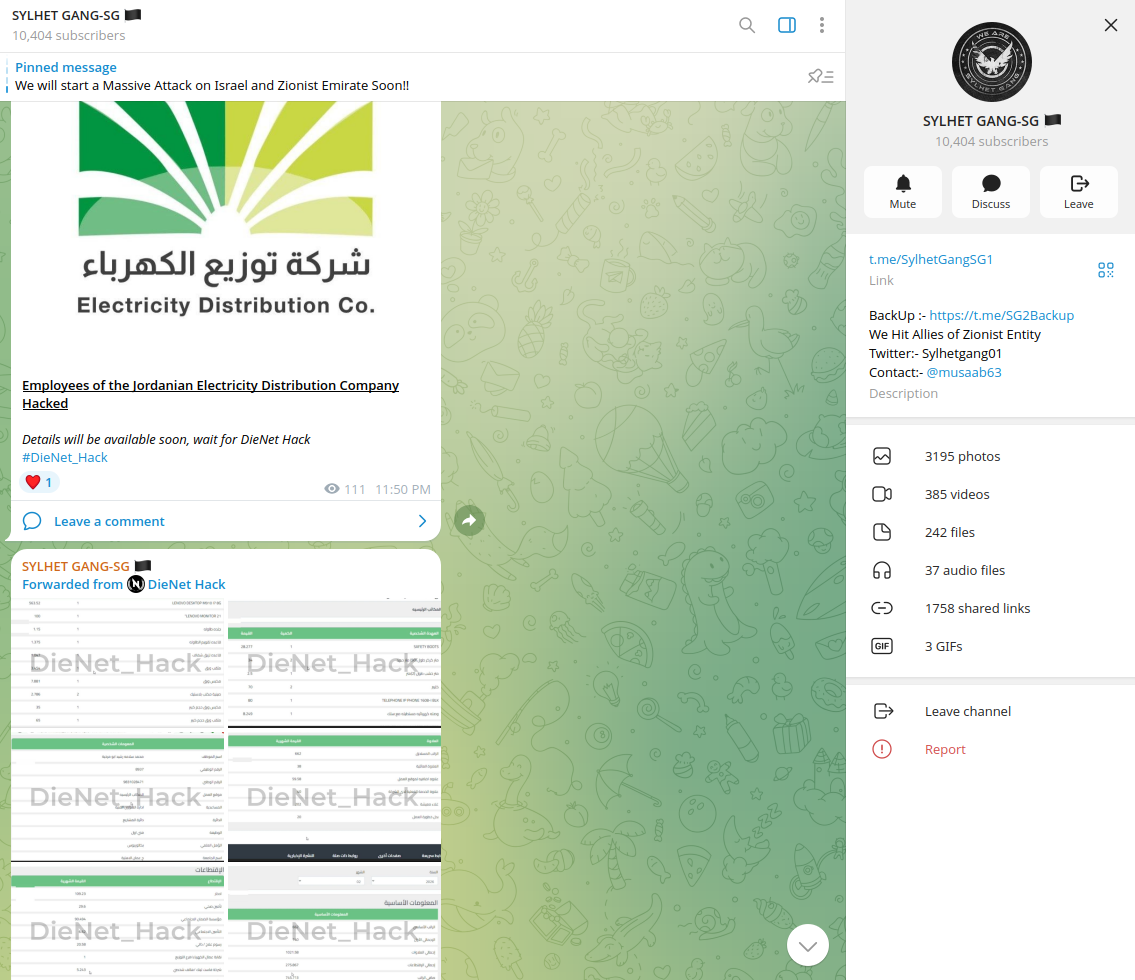
Groups like DieNet and Sylhet Gang-SG claimed to attack over 400 Israeli resources, including national identity providers and e-government portals. These groups are also known for providing DDoS services in the underground, which may confirm that they could be tasked (and paid) to conduct such activities.
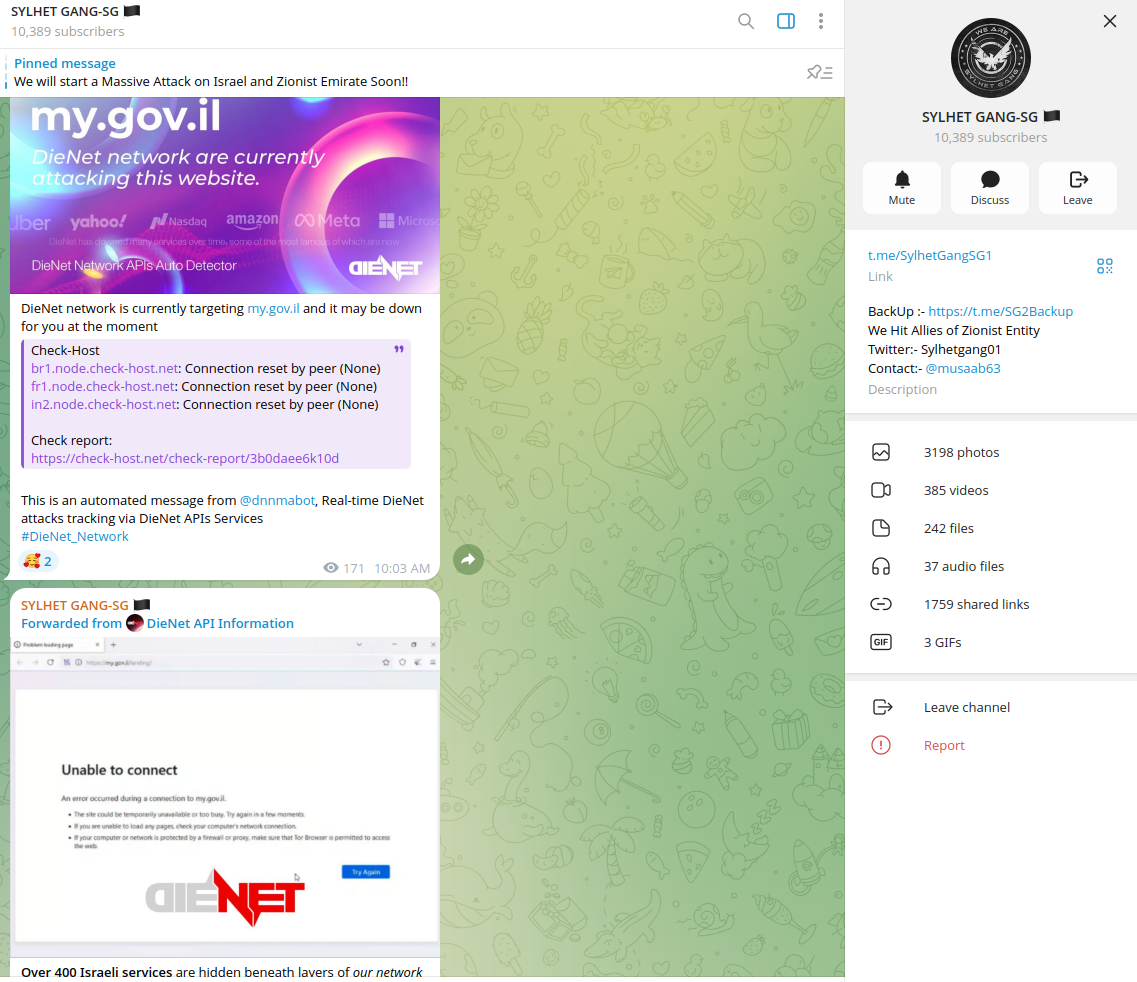
Many such DDoS attacks have been conducted using third-party underground services, such as 'stressers' for rent, including Cosmic Network (V2), SpaceStresser, TheFlashDDOS, and EliteStresser. Such tooling may cause short-term outages and load on web servers and applications, especially when leveraging a combination of attacks against commercial CDNs and WAFs. To scale the volume of attacks, threat actors leverage residential proxies, compromised servers, and IoT devices to generate malicious traffic.
Notably, some of the actors associated with these groups encourage followers to collect intelligence about the US and Israeli forces abroad, which shows potential Human Intelligence (HUMINT) gathering efforts by Iran, still limited by Iran due to a lack of network connectivity and disrupted communications.
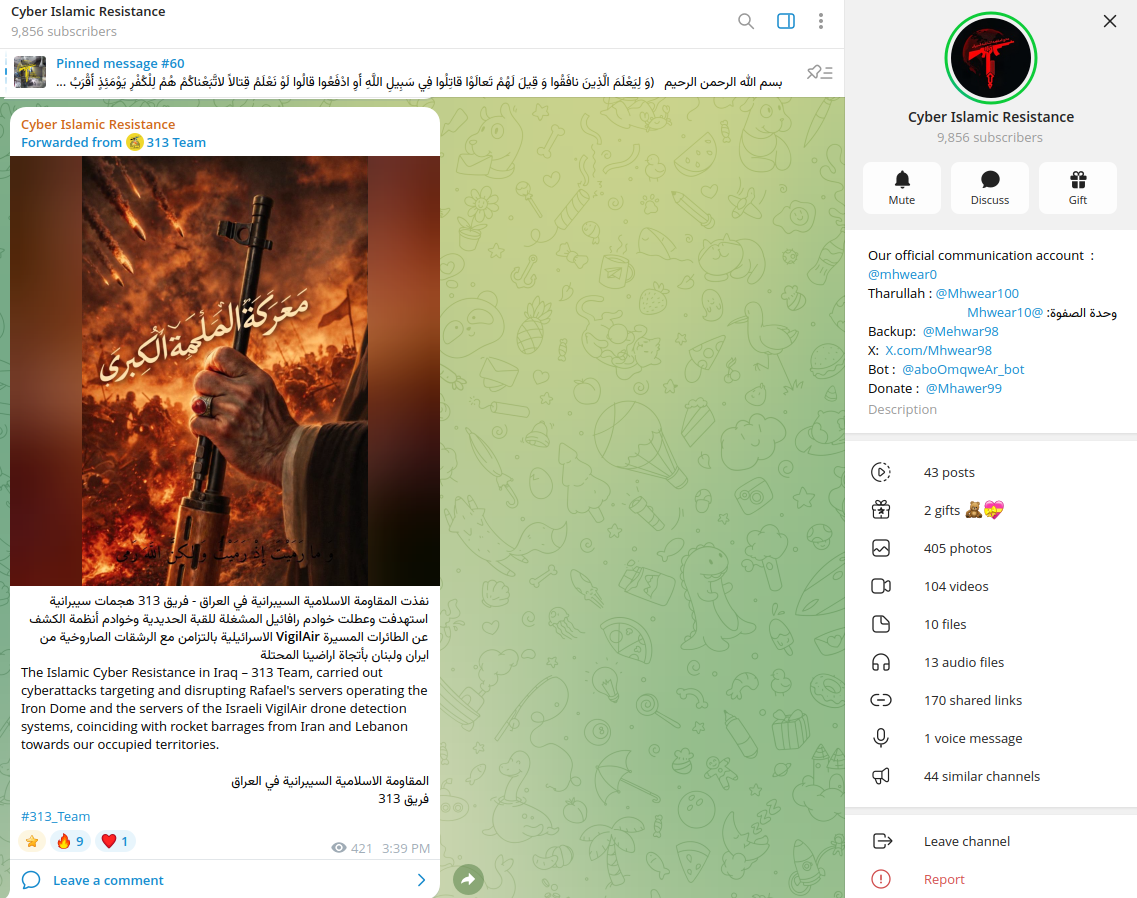
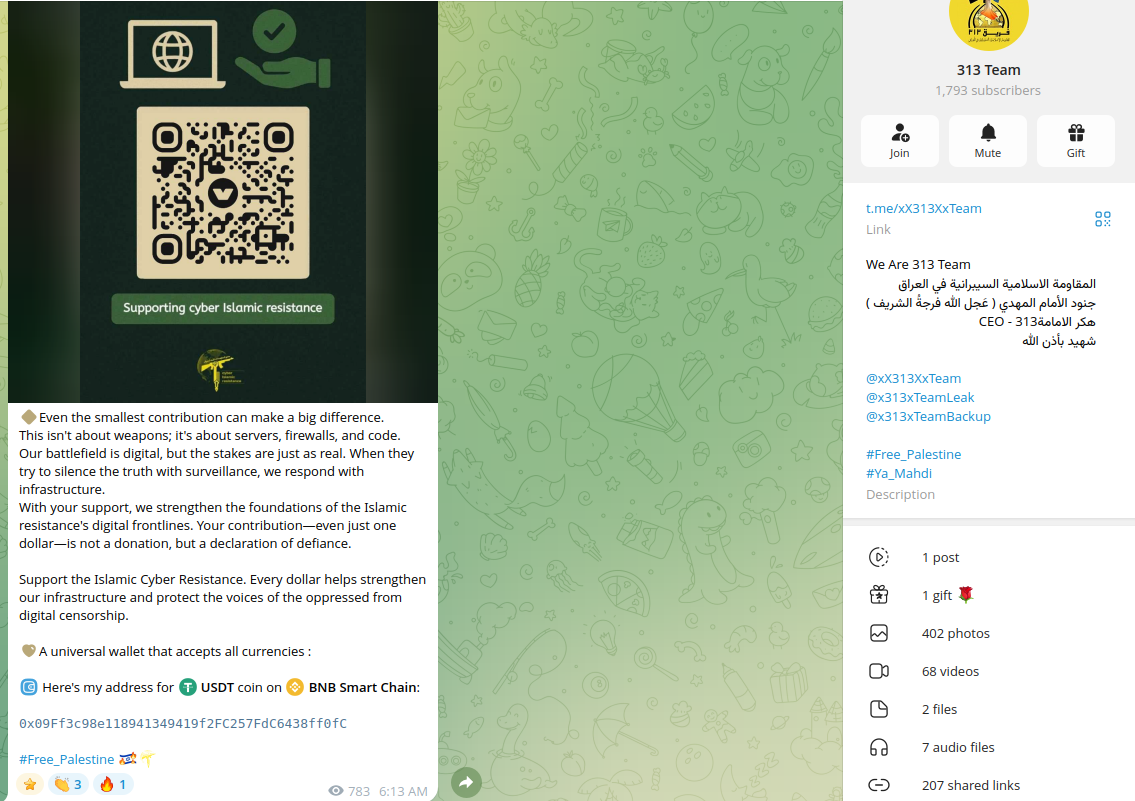
The identified attacks were also targeting Israeli defense contractors and entities associated with the defense industrial base in other countries cooperating with Israel. One of the most active groups releasing such claims is 313 Team, presumably associated with the Islamic Cyber Resistance in Iraq.
Attacks against energy infrastructure have been detected targeting Jordan. The actors have already used exposed infostealer data to obtain credentials and access web panels and applications.
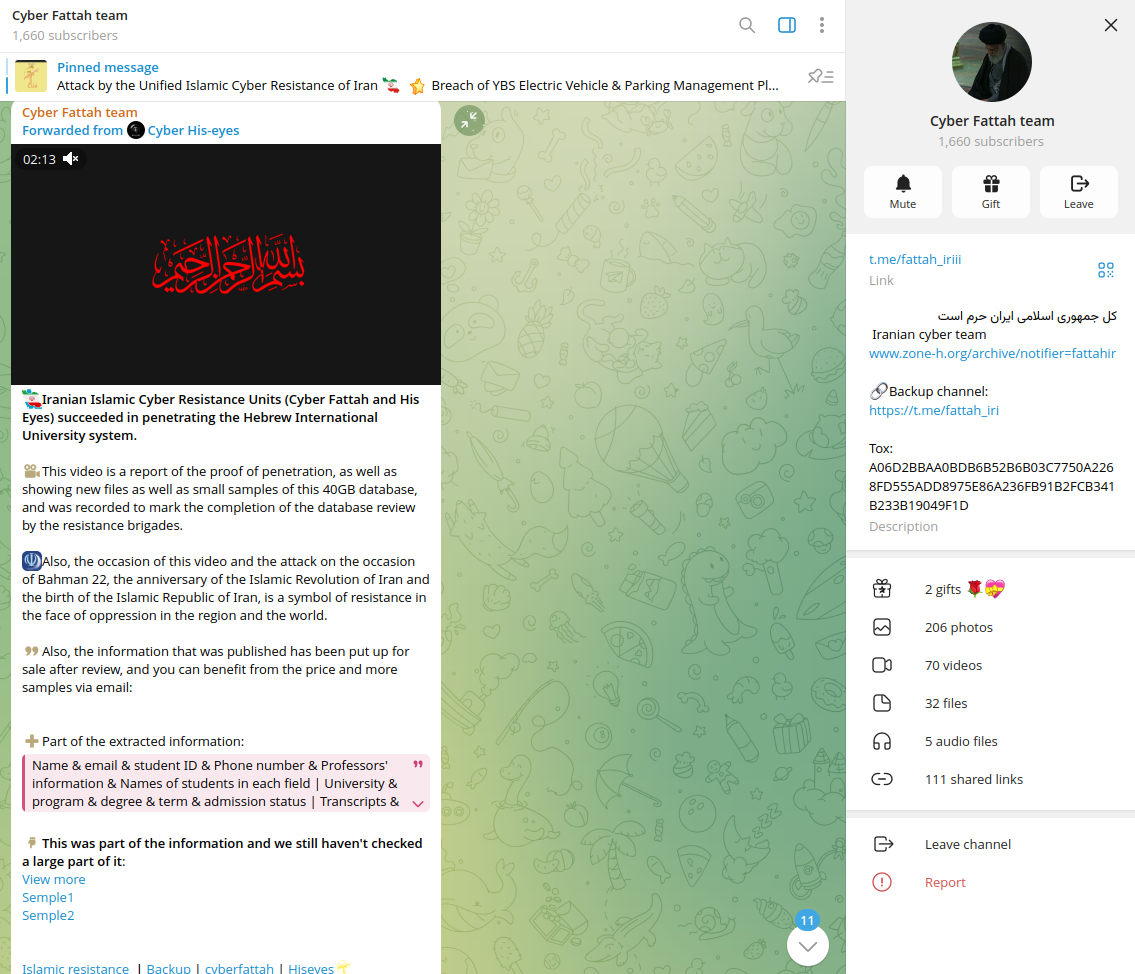
Besides DDoS claims, Pro-Iranian hacktivists such as Cyber Fattah (which calls itself an "Iranian Cyber Team") were targeting other sectors, including educational institutions in Israel.
Hacktivists attempted to attack publicly exposed IoT devicess by scanning Israeli-based IP ranges.
The pro-Iranian actors were also targeting popular Hikvision and Dahua cameras with several authentication and command-related vulnerabilities. The bugs they use include CVE-2017-7921, CVE-2021-36260, CVE-2023-6895, and CVE-2025-34067 for Hikvision; and CVE-2021-33044 for Dahua. Patches for all vulnerabilities are available now.
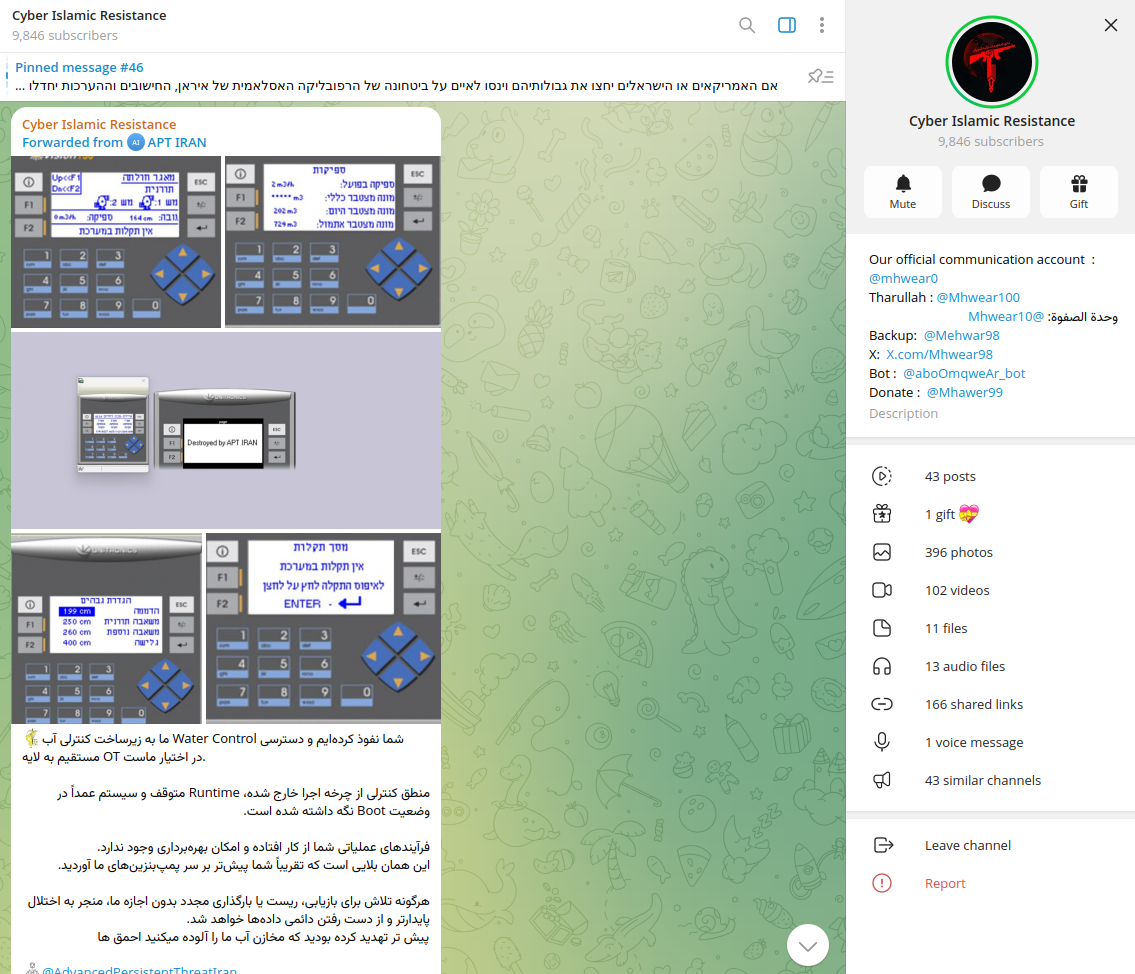
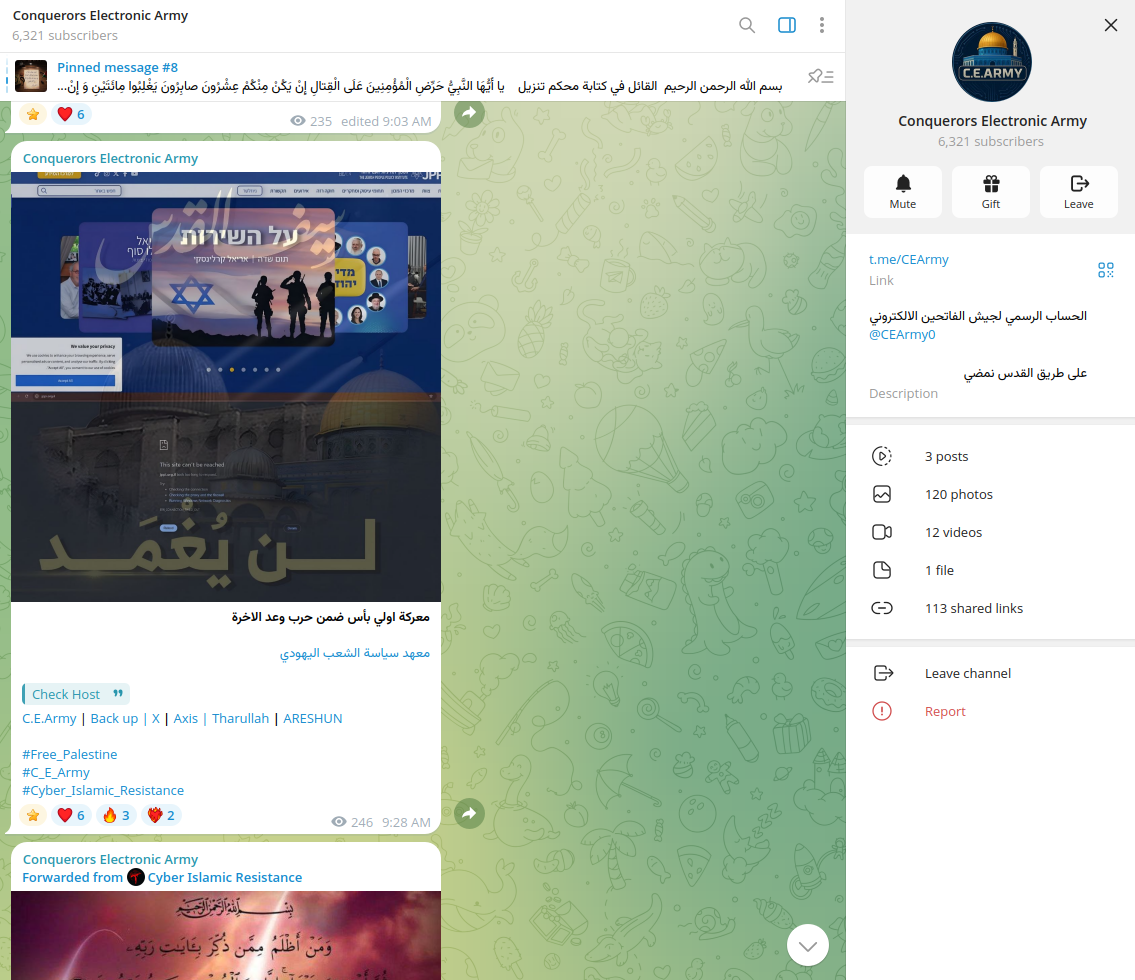
DDoS attempts also targeted Israeli military resources by groups such as Conquerors Electronic Army.
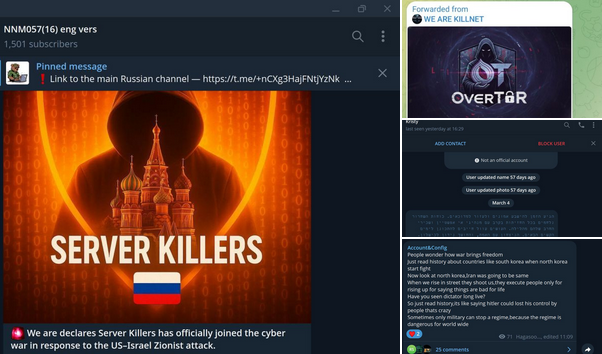
A Telegram channel presumably operated by Russian-speaking actors announced that the group Server Killers was joining the cyber war against the US and Israel. With a high level of confidence, this group's activity is more opportunistic than state-directed. Their claims of providing substantial support to Iran are exaggerated. Other groups, such as Killnet, NNM057 (16), and Russian Legion, have also been involved in similar activities. Regardless of claims that Russia is providing Iran with intelligence to target U.S. forces, activity in cyberspace appears to be uncoordinated and conducted by multiple disconnected groups.
It is expected to see actors originating from other geographies joining the Iran conflict. The darknet ecosystem is amplifying the conflict, with hacktivist propaganda, Iran-related data-leak trading, and recruitment efforts, indicating a rise in opportunistic cyber activity amid the geopolitical situation.
2. Website Defacements, Data Theft, and Data-Wiping Operations
- Iranian-affiliated hacktivist groups, such as the Cyber Islamic Resistance, have conducted website defacements and data-wiping attacks. These operations targeted US and Israeli military logistics providers, aiming to destroy data and disrupt operations.
- Several Iranian hacker groups have announced the recruitment of cyber experts and resources for what they call “the Great Epic Battle,” urging supporters to join their digital combat network.
- Based on Resecurity's assessment, this activity does not affect operational or processes activities and is considered opportunistic. Due to time constraints and damaged network infrastructure, Iran lacks the digital resources to regroup and will need time to formulate a broader response.
- It is expected that this activity will shift towards ransomware operations, where sensitive or critical data for operations will be taken hostage by Iran, accompanied by further demands beyond just financial compensation.
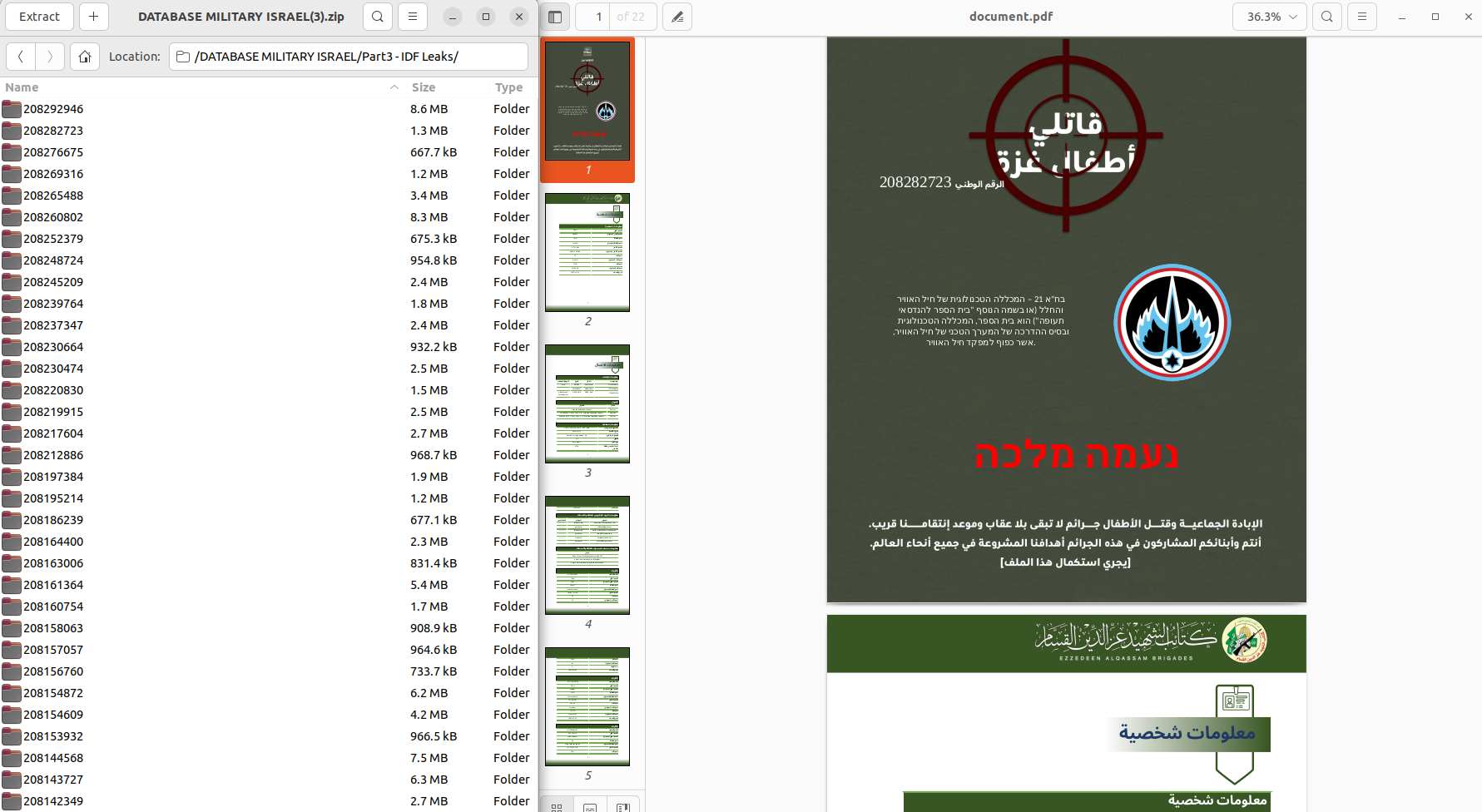
Several pro-Iranian channels were circulating data about Israeli military personnel. Based on a Resecurity assessment, those records were also part of misinformation campaigns and contained previously leaked records involving IDF members. Such data creates optics of a possible leak planting uncertainty via social media.
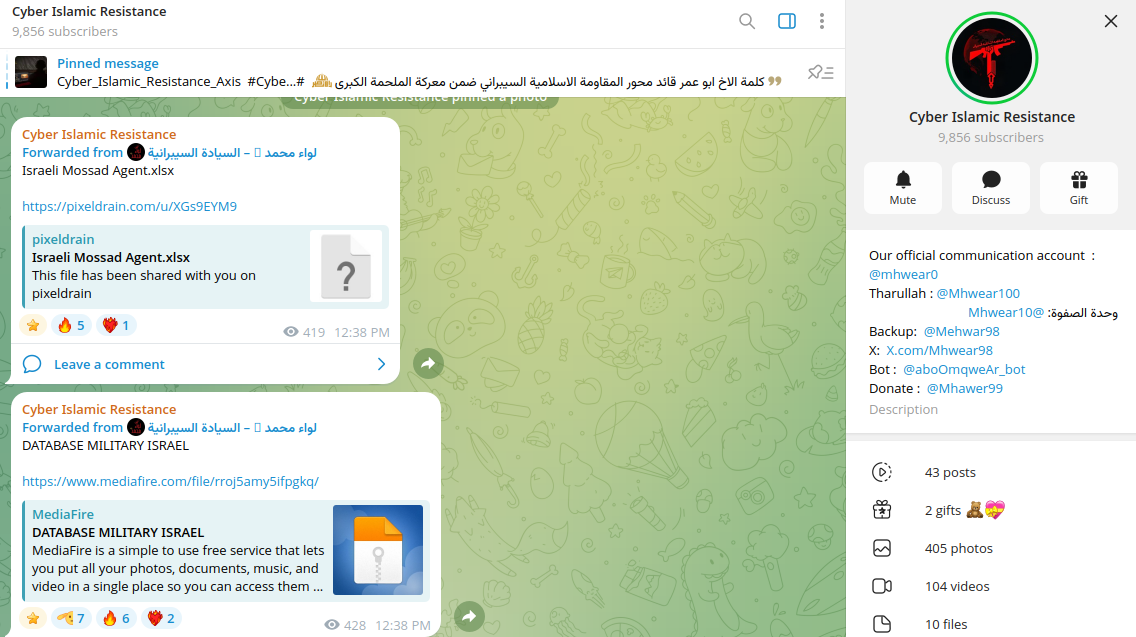
Some of these files have been previously shared by the Ezzedeen Alqassam Brigades (also known as the Izz al-Din Al-Qassem Brigades), a military wing of Hamas.
Resecurity interprets Hamas and Hezbollah as the key actors involved in malicious cyber activity due to the limited capabilities from within Iran to conduct any counterattacks. Their proxies located abroad provide them with various forms of support.

The Telegram channels associated with these movements accelerated their collection of donations to support their operations via cryptocurrencies.
Around the beginning of March, Resecurity identified the emergence of relatively new groups, such as Cyber Isnaad Front.
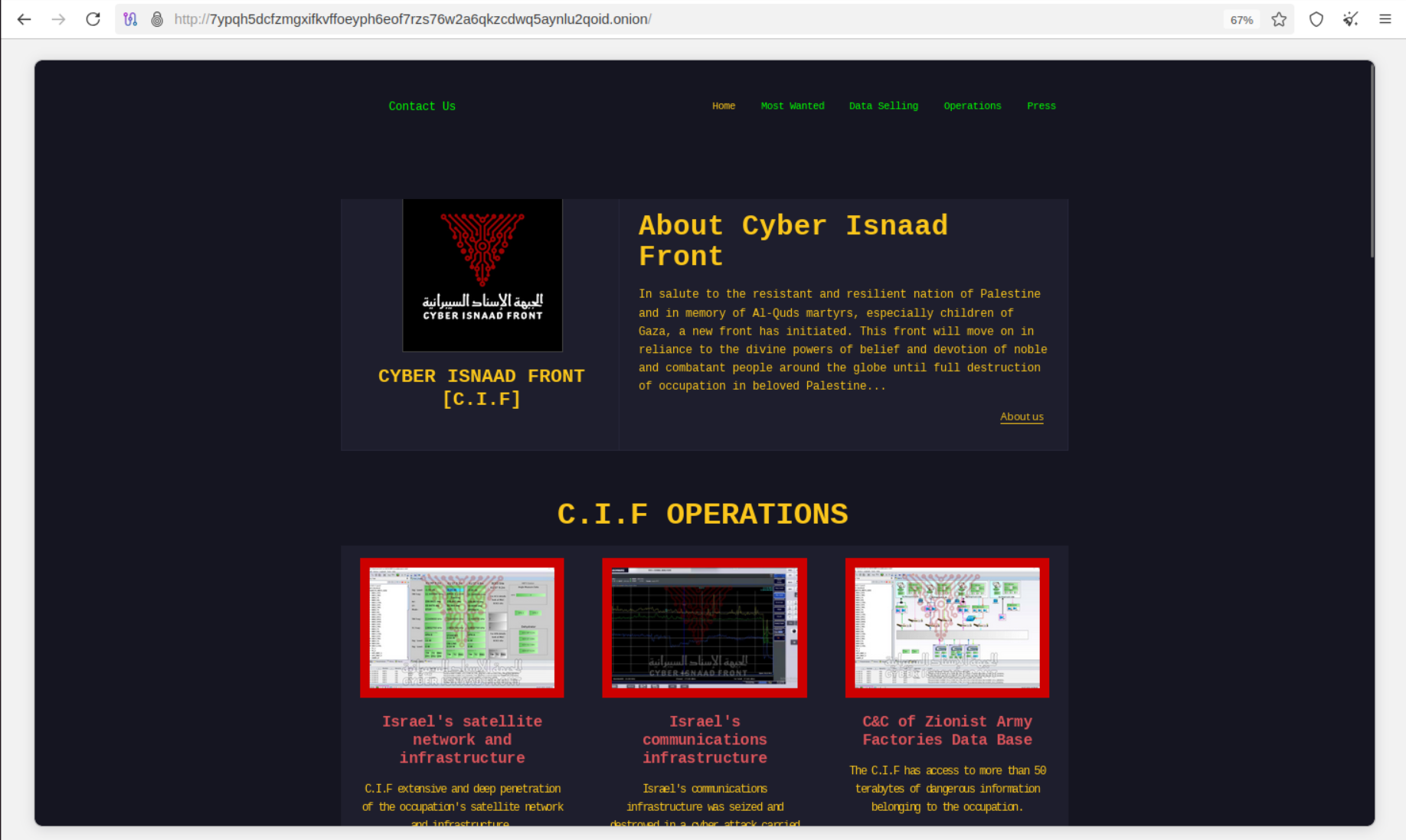
The group has targeted critical infrastructure and telecommunication providers of Israel, but also released a 'hit list' of people operating in various industries.
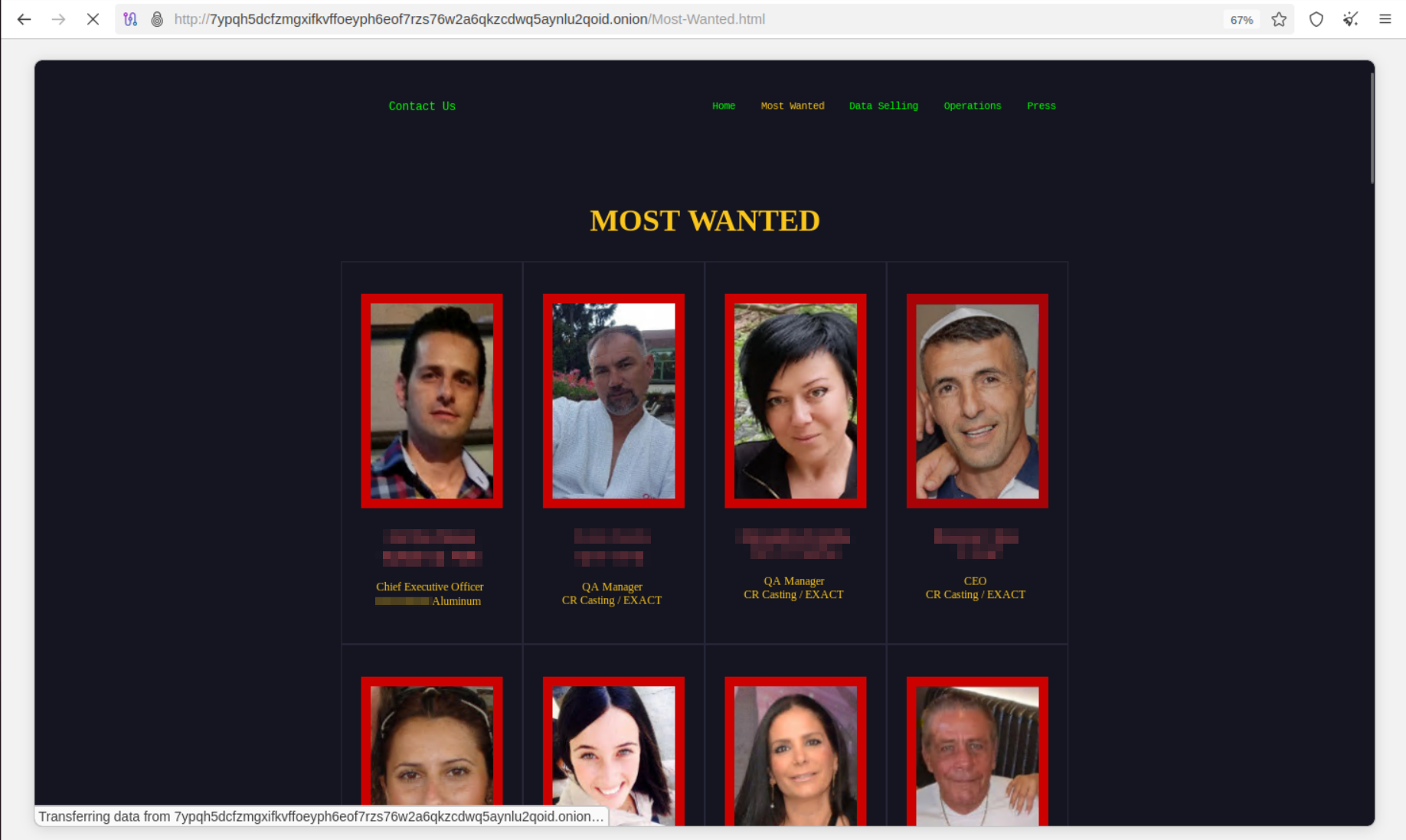
It is expected that Iran will use similar campaigns targeting specific individuals as a means of psychological pressure on executives working in specific sectors of the economy and industry. While unlikely to create a significant impact, these efforts may be combined with extortion and ransom demands.
Resecurity may highlight Handala Hack Team as one of the most credible actors, with increased data theft and ransomware activity during the Iran War. In addition to targeting organizations, they focus on individuals in the defense sector to exert influence.

The group is targeting military officials and has released stolen data as a method of retaliation.
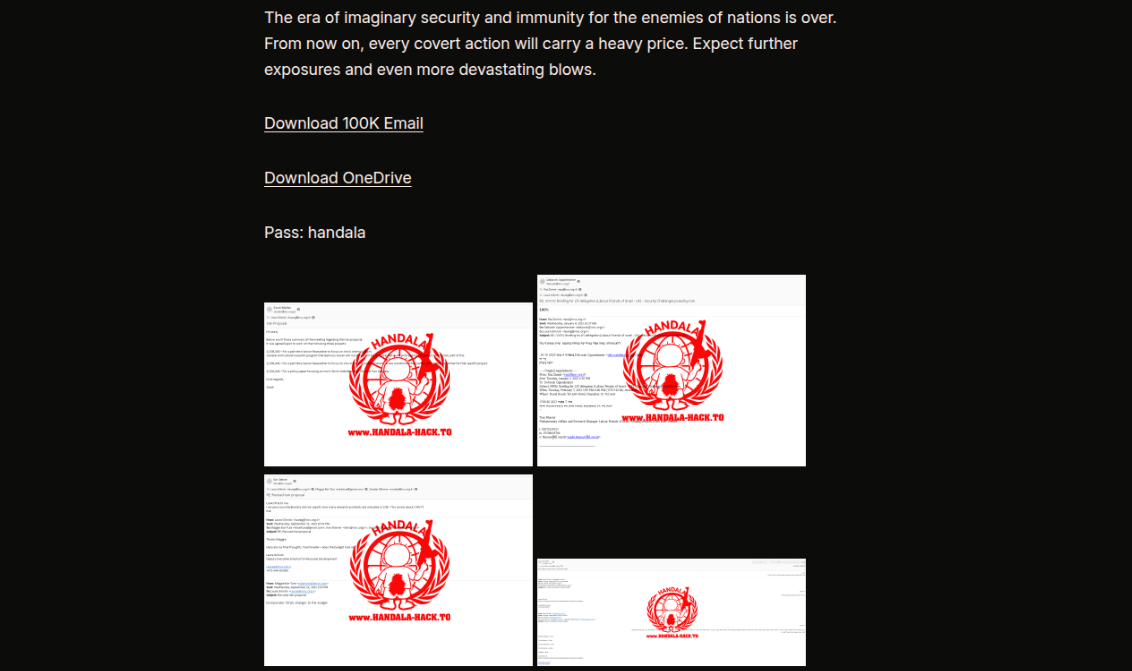
Handala was also responsible for the attack on the U.S.-based medical company Stryker, which impacted systems and applications and involved the theft of a massive volume of data.
3. Psychological Operations
- Hacktivists have engaged in psychological operations, mimicking high-profile hacks such as the BadeSaba incident. These operations aim to spread fear and confusion among the targeted populations.
- Iran is also conducting defensive digital psychological operations to keep the population motivated for the war and aligned with the existing regime. To counter that, the U.S. and its allies conduct attacks against broadcasting infrastructure and state media.
- It is expected that Iran will switch to alternative media channels, likely organized via mobile communications, to spread propaganda and war-focused messaging, encouraging the population to respond further.
4. Misinformation
- Viral images and videos claiming to show attacks, explosions, or military actions by Iran were often AI-generated or taken from unrelated events. Examples include fake visuals of attacks on Dubai (UAE) and dramatic scenes of destruction that never occurred.
- Clips from military video games were circulated as real combat footage, misleading viewers about the reality on the ground. Iranian-aligned cyber groups have carried out cyberattacks and exaggerated their impact to sow confusion and fear.
- In one of the misinformation episodes, a pro-Iranian group was circulating messaging that Khamenei had not been killed.
Resecurity highlights misinformation focused on both cyber activity and kinetic actions. E.g., Iran claims to have struck the USS Abraham Lincoln with missiles and drones, but the US Central Command released images showing the carrier operating as normal. The claims by Iran are part of a bigger misinformation campaign attempting to discredit the US military.
5. Pro-Western Hacktivist Activity
- In addition to Iranian-aligned groups, pro-Western hacktivists have also been active, targeting Iranian apps and websites. These attacks are likely intended to counter Iran’s cyber retaliation and disrupt its digital infrastructure.
Notable Groups Involved
- Iranian-Aligned Hacktivists:
- Groups like the Cyber Islamic Resistance, Fatimion Cyber Team, and Cyber Fattah have been identified as key players in the escalation. Their activities include reconnaissance, DDoS campaigns, website defacements, and data theft.
- Pro-Western Hacktivists:
- These groups have targeted Iranian religious apps and news sites, likely as part of a broader effort to undermine Iran’s narrative/propaganda targeting Iranian citizens and supporters.
- Notably, such factors include Iranian opposition groups residing abroad (outside of Iran), targeting the existing regime. Many of these actors reside in the US, the UK, the EU, Canada, and Australia.
Strategic Implications
- Escalation in Cyber Retaliation: The surge in hacktivist activity highlights the growing role of cyber operations as a parallel front in geopolitical conflicts. Hacktivists often act as proxies or independent actors, amplifying the impact of state-sponsored cyber campaigns.
- Volatility in the Cyber Domain: Experts warned that the next 48 hours after the strikes could see "extreme volatility," with hacktivists and proxies leading the escalation while Tehran’s central command regroups.
Historical Retrospective
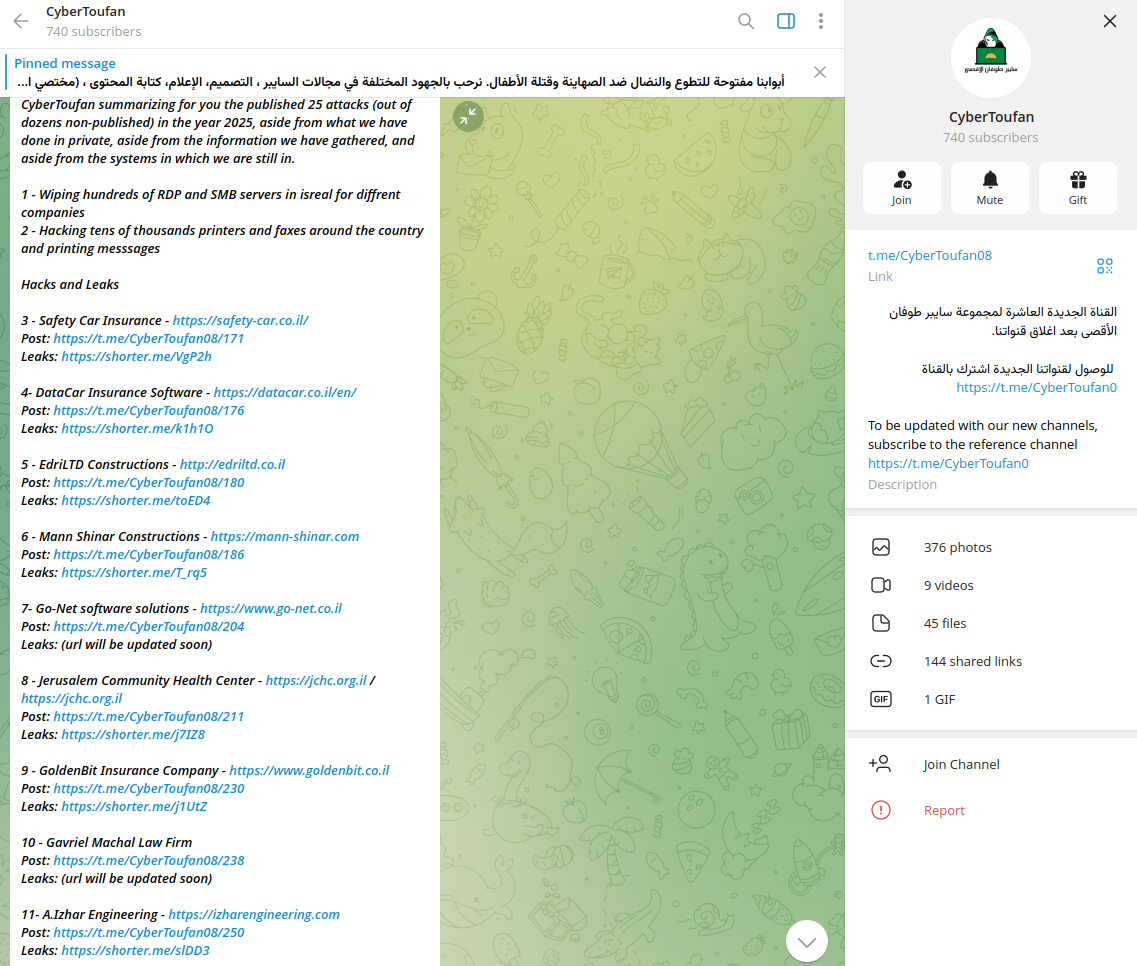
It is important to differentiate between cyber-related events that occurred during Epic Fury and those that happened before it. For example, groups like CyberToufan were actively targeting Israel before the current events. Many of the resources they compromised have been reused in recent attacks. Threat actors did this because they rely on historical data, as they are unable to generate new victims quickly, and leveraging information about previous targets could amplify their counterattacks. In some of their posts, these actors claimed that the stolen data had not been published previously.
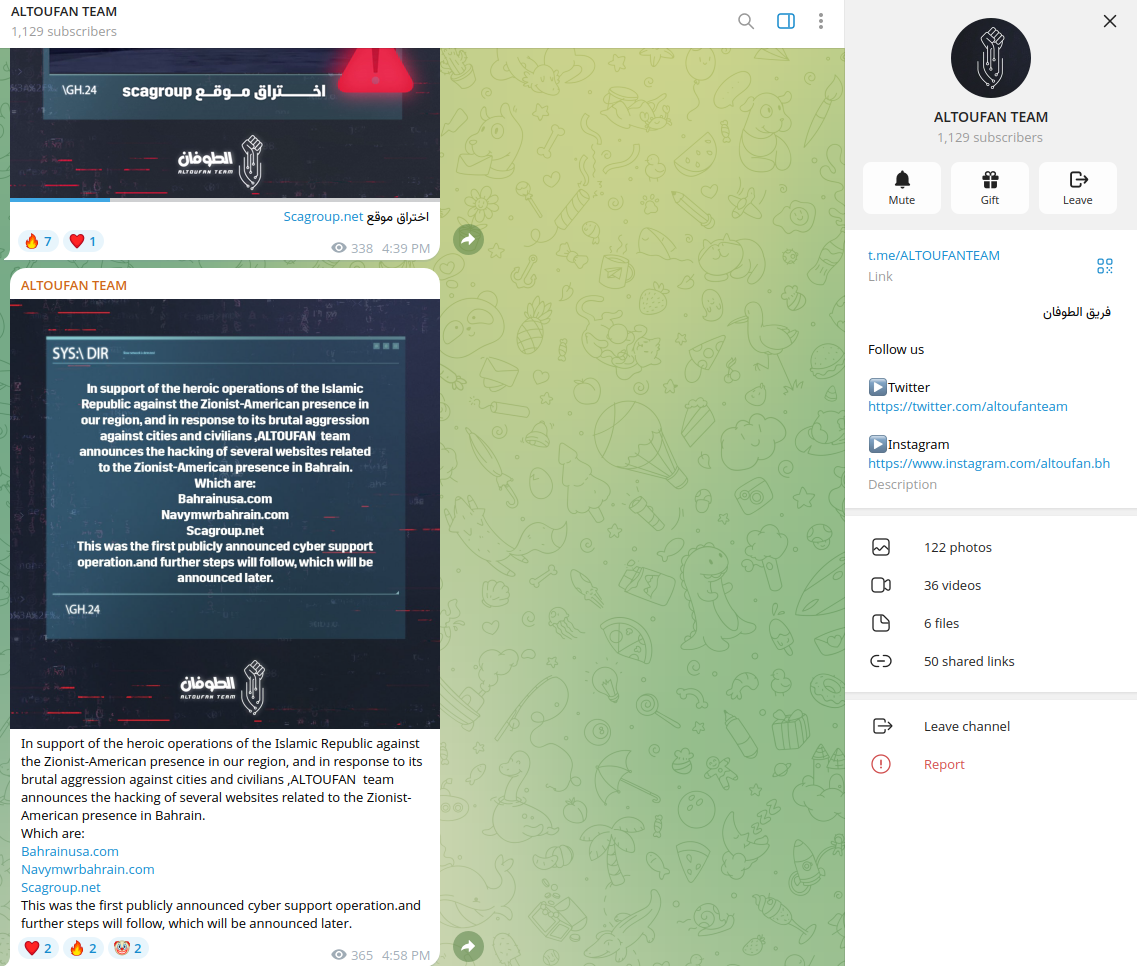
Some of the identified communications by threat actors were anti-American - the goal of such communications was to generate hate and social polarization between nations. Groups like Altoufan Team targeted Bahrain. For example, groups like the Altoufan Team targeted Bahrain to attach the US ally to antisemitic messaging and provoking hate. Iran widely uses such tactics as a mechanism of influence via social media.
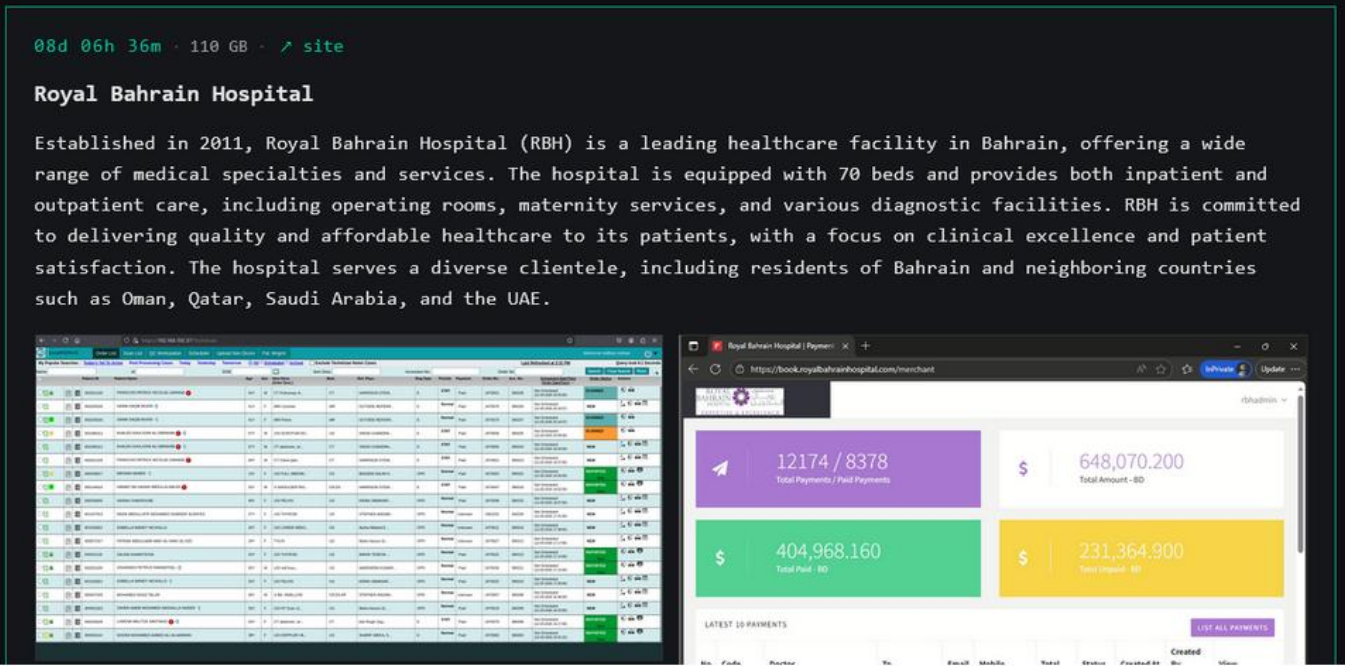
Notably, some cybercriminal groups with no direct relation to Iran, such as Payload Ransomware, accelerated their activities during the Iran war. In one of the recent incidents, the bad actors targeted Bahrain Royal Hospital, claiming to release stolen data affecting residents of Bahrain and neighboring countries such as Oman, Qatar, Saudi Arabia, and the UAE.
Resecurity expects data brokers to accelerate their underground activity to capitalize on the Iraq war and monetize access to relevant enterprise and government resources in the GCC.
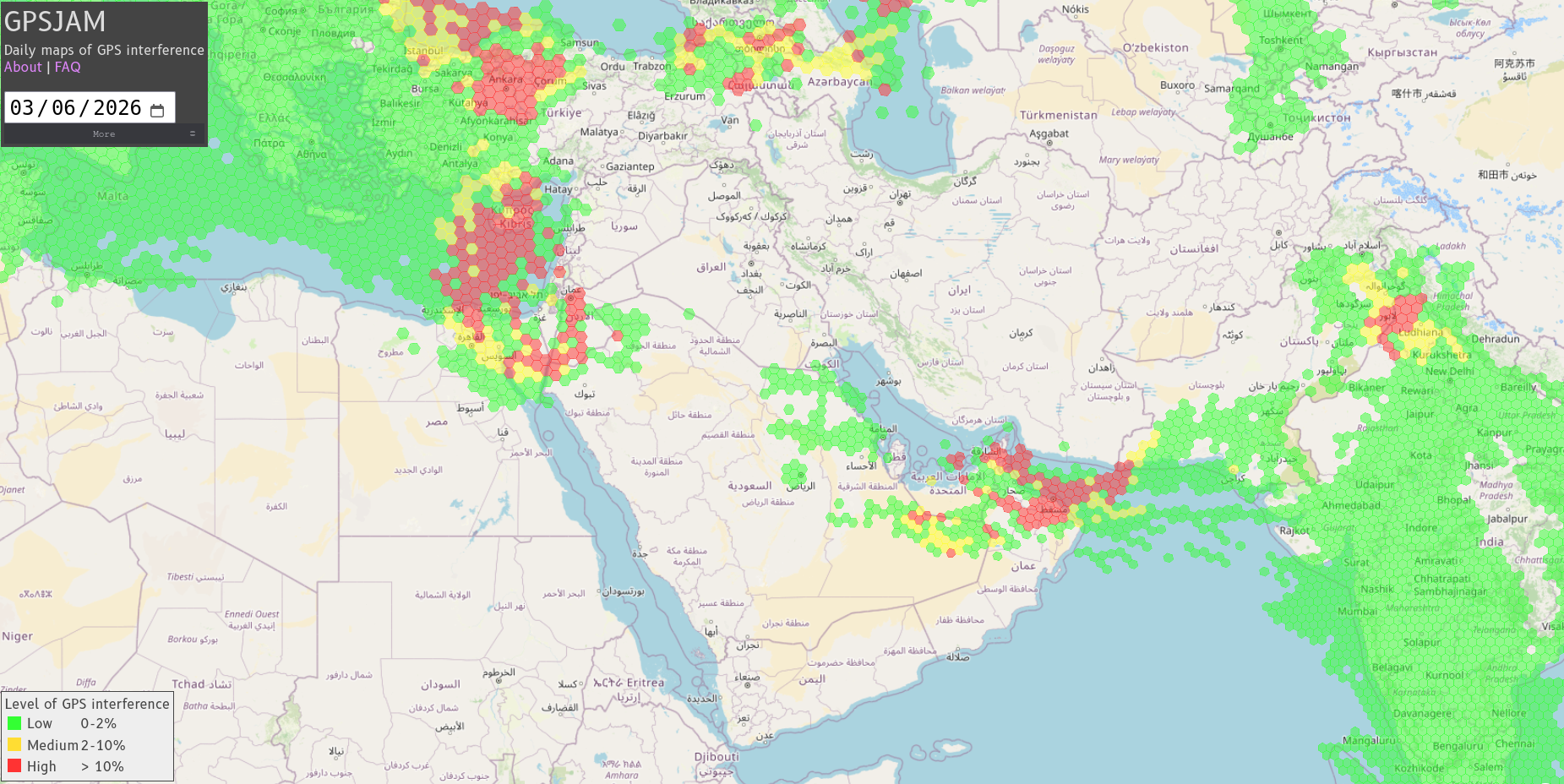
6. SIGINT
The 2025–2026 Iran War witnessed the most extensive and disruptive use of GPS spoofing and jamming ever recorded, severely impacting maritime, aviation, and military operations across the Persian Gulf, Strait of Hormuz, Iraq/Iran airspace, and beyond. Iran was the principal actor, with both state and proxy forces deploying sophisticated electronic warfare (EW) systems, resulting in widespread navigation failures, operational paralysis, and heightened safety risks for civilian and military platforms.
Within 24 hours of the first US-Israeli strikes, over 1,100 commercial ships in the UAE, Qatari, Omani, and Iranian waters experienced navigation failures. Ships’ systems falsely reported positions at airports, nuclear plants, and on land—classic spoofing signatures.
Windward identified 21 new clusters of jamming on the first day, rising to 38 clusters the next day. Lloyd’s List Intelligence logged 1,735 GPS interference events affecting 655 vessels in the first week, with daily incidents nearly doubling. On March 7, over 1,650 vessels experienced interference, a 55% increase over the previous week.
Resecurity may highlight substantial risks for the OT environment, as GNSS and GPS spoofing can affect digital and physical services that depend on geolocation.
Conclusion
Hacktivist activity has significantly escalated following the US-Israeli strikes on Iran. Both Iranian-aligned and pro-Western groups are actively engaging in cyberattacks, including DDoS campaigns, data-wiping operations, and website defacements. These actions underscore the increasing importance of cyber warfare and hacktivism as tools of retaliation and influence in modern conflicts.
Both Iranian-aligned and pro-Western groups are actively engaging in cyberattacks, including DDoS campaigns, data-wiping operations, and website defacements. These actions underscore the increasing importance of cyber warfare and hacktivism as tools of retaliation and influence in modern conflicts.
This escalation manifests through increased proxy militia attacks (rocket, drone, and IED strikes), cyber operations, and asymmetric tactics such as maritime harassment and influence campaigns. These responses are strategically designed to retaliate, deter further US action, and advance Iran’s regional objectives, while carefully managing the risk of uncontrollable escalation.
The Iran war has shifted global attention and resources, placing other ongoing conflicts like Russia-Ukraine, Israel-Gaza, and Pakistan-Afghanistan in a secondary position. This shift is due to the Iran war's scale, its direct involvement of global powers (the US and Israel), its impact on global energy markets, and its potential to destabilize the entire Middle East.
While these other conflicts remain significant, their relative importance has diminished in the face of the immediacy and broader implications of the war in Iran. However, the long-term trajectory of global attention will depend on how the war in Iran evolves and whether it escalates further or stabilizes.
Forecast
The Iran war is forecast to remain a protracted, disruptive conflict with severe humanitarian and economic consequences. While the risk of a full-scale regional war is low, the likelihood of continued missile, drone, and cyberattacks is high. Iran’s nuclear program remains a significant concern, with increased breakout risk despite recent setbacks. The closure of the Strait of Hormuz and turmoil in the oil market are driving global inflation and supply chain disruptions. Diplomatic resolution appears unlikely in the near term, and the world faces sustained instability in the region.
Iraq is likely to become—and in some respects already is—a new front in the ongoing Iran–US/Israel conflict. While the Iraqi government seeks neutrality and sovereignty, its limited control over militias and the frequency of cross-border strikes make Iraq a key arena for proxy warfare and potential confrontation. Major groups involved include the Popular Mobilization Forces (PMF/Hashd al-Shaabi), Kataib Hezbollah, and other Iranian-aligned factions.
The Iran war is already having significant and multi-dimensional impacts on countries outside of the GCC, including Bangladesh, Pakistan, and India. These effects span energy security, trade and supply chains, remittances and diaspora safety, and strategic geopolitics. Both countries face heightened economic risks, direct disruptions, and new diplomatic challenges as the conflict persists. Large multinational corporations in France with stakes in the region's oil and gas business have also been affected by these events. Energy price shocks threaten macroeconomic stability and industrial output.
Disinformation will grow dramatically in both scale and sophistication during an Iran war, driven by advances in AI, social media manipulation, and coordinated state and proxy operations.
New cyberattacks by Iranian proxies are expected during the ongoing Iran war. Due to the near-total internet blackout in Iran, state-sponsored groups may be less active, but proxies and recruited operatives operating outside Iran are likely to increase their activity.
Resecurity may also highlight the growing risk of hate-motivated violence linked to global conflicts. Multiple communities—including Jewish-Americans, Iranian-Americans, Muslim-Americans, and Arab-Americans—are experiencing increased incidents of violence, harassment, and threats. The risk is amplified by online radicalization, extremist mobilization, and a polarized political climate. Heightened vigilance, robust security measures, and community solidarity are essential to mitigate these threats. The FBI released a Public Service Announcement on hate-motivated threats tied to global conflicts.

