Critical MajorDoMo RCE (CVE-2026-27174): Unauthenticated Remote Code Execution Analysis
Vulnerability Assessment and Penetration Testing (VAPT)


Summary
CVE-2026-27174 is a critical unauthenticated remote code execution vulnerability affecting MajorDoMo. The flaw stems from improper authentication handling combined with unsafe use of PHP’s eval() function, allowing remote attackers to execute arbitrary PHP code through the exposed admin panel without valid credentials. Because MajorDoMo often controls cameras, sensors, automation logic, and internal IoT systems, successful exploitation may lead to full server compromise and broader network exposure.
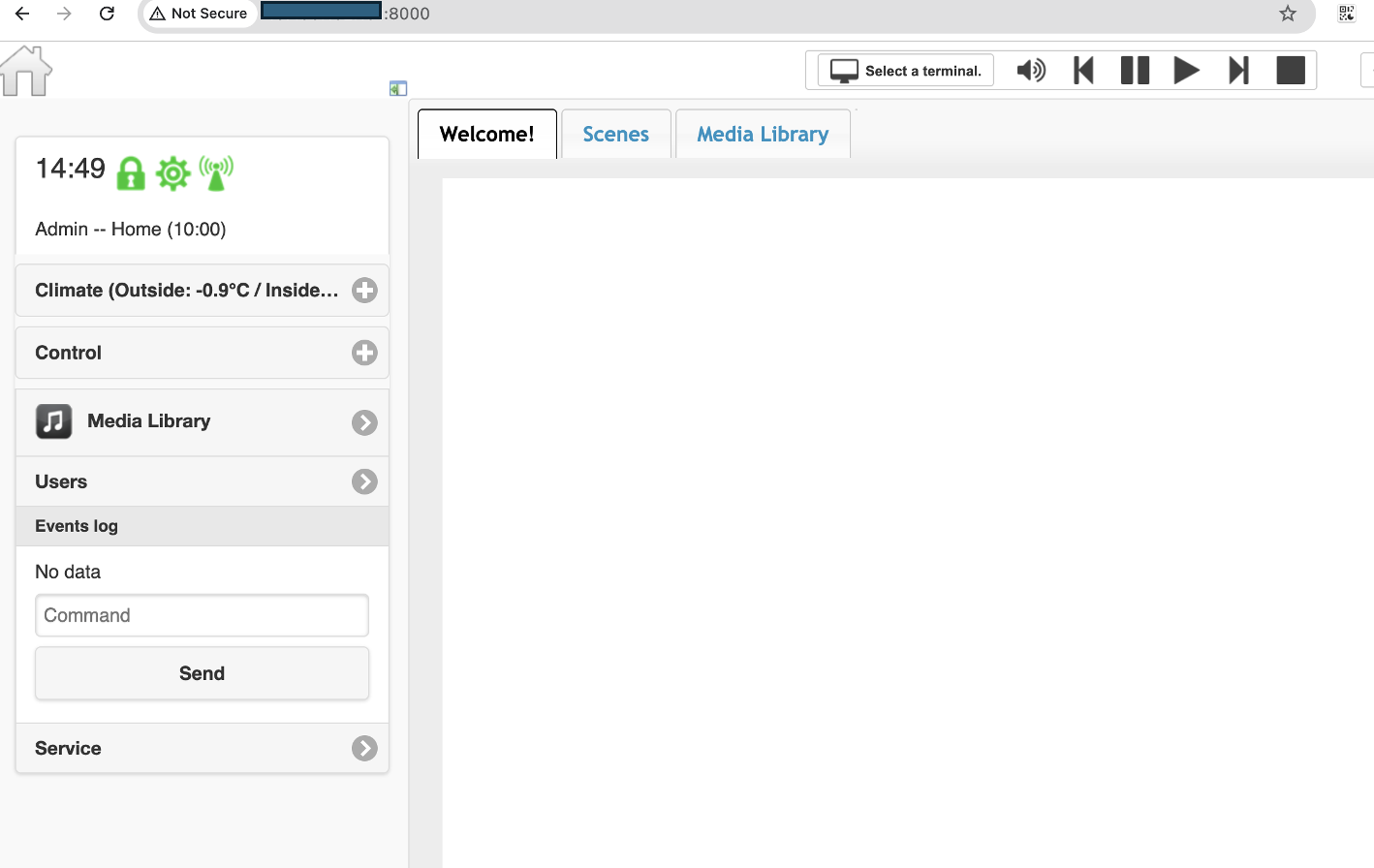
Platform Overview
MajorDoMo is an open-source home automation and IoT management platform designed to control, automate, and monitor smart devices through a centralized web interface. It enables users to connect multiple systems such as lighting, cameras, sensors, climate controls, and other smart devices into one unified dashboard.
MajorDoMo is commonly deployed on home servers, virtual machines, Raspberry Pi devices, or private cloud environments, making it popular among smart-home enthusiasts and organizations that prefer self-hosted solutions.
Its core purpose is to simplify device management and allow users to create custom automation workflows without depending entirely on commercial cloud ecosystems.
Why Is It Important?
MajorDoMo is important because it often acts as the central controller for an entire smart-home or automation environment. Instead of managing many separate apps and devices individually, users can control everything from a single platform.
Key reasons it is widely used include:
- Centralized Management: Manage multiple smart devices from one interface.
- Automation Capabilities: Create rules such as turning lights on when motion is detected or adjusting temperature automatically.
- Broad Compatibility: Supports integration with many IoT brands and protocols.
- Local Control & Privacy: Can run entirely on local infrastructure rather than relying on third-party cloud services.
- Customization: Users can build advanced scripts and workflows tailored to their environment.
Why It Matters for Security
Because MajorDoMo often has access to sensitive systems such as cameras, locks, sensors, and internal networks, any security vulnerability can have significant consequences.
A compromise could potentially allow attackers to:
- Gain access to connected devices
- View surveillance systems
- Manipulate automation routines
- Steal stored credentials
- Pivot deeper into internal networks
For this reason, vulnerabilities affecting MajorDoMo—especially remote code execution flaws—are considered high impact.
Technical Details for CVE-2026-27174
CVE-2026-27174 is a critical unauthenticated remote code execution (RCE) vulnerability affecting MajorDoMo. The issue is caused by a dangerous combination of improper authentication enforcement and unsafe dynamic code execution.
At a high level, the vulnerability arises when the application attempts to redirect unauthenticated users away from the administrative interface but fails to stop script execution afterward. Because execution continues, an attacker can still reach internal administrative functionality that should only be available to authenticated users.
Once this logic flaw is abused, the request reaches an AJAX handler that exposes a console/debugging feature. That feature accepts user-controlled input and passes it directly into PHP’s eval() function, allowing arbitrary PHP code execution on the server.
This creates a highly dangerous attack chain requiring only a crafted HTTP request to the vulnerable admin endpoint.
Root Cause Analysis
The vulnerability results from two separate coding mistakes that become critical when combined.
1. Improper Authentication Enforcement
Inside the administrative request flow, unauthenticated users are redirected, but the script does not terminate with exit; or die;.
Vulnerable Logic Pattern
if (!$authorized) {
redirect('/');
// script should terminate here
}
// remaining code still executes
include('inc_panel_ajax.php');In PHP, issuing a redirect often only sends headers. If execution is not explicitly stopped, the application continues processing the request.
This means an attacker may still reach privileged backend functionality even though the browser receives a redirect response.
2. Unsafe Use of eval()
Within the AJAX console feature, attacker-controlled input is reportedly passed directly into eval().
Vulnerable Pattern
$command = $_REQUEST['command'];
eval($command);eval() executes the supplied string as PHP code. If user input reaches it without strict validation, attackers may run arbitrary commands, modify files, access secrets, or fully compromise the host.
Vulnerable Components Analysis
modules/panel.class.php
This component appears responsible for access control and admin panel routing.
Likely vulnerable behavior:
- Detects unauthenticated users
- Sends redirect response
- Fails to terminate execution
- Continues loading protected modules
inc_panel_ajax.php
This component processes internal admin AJAX actions.
Likely dangerous behavior:
- Reads user-supplied parameters
- Routes based on operation name
- Includes console/debug feature
- Executes supplied code via eval()
Full Attack Chain – Step-by-Step Description
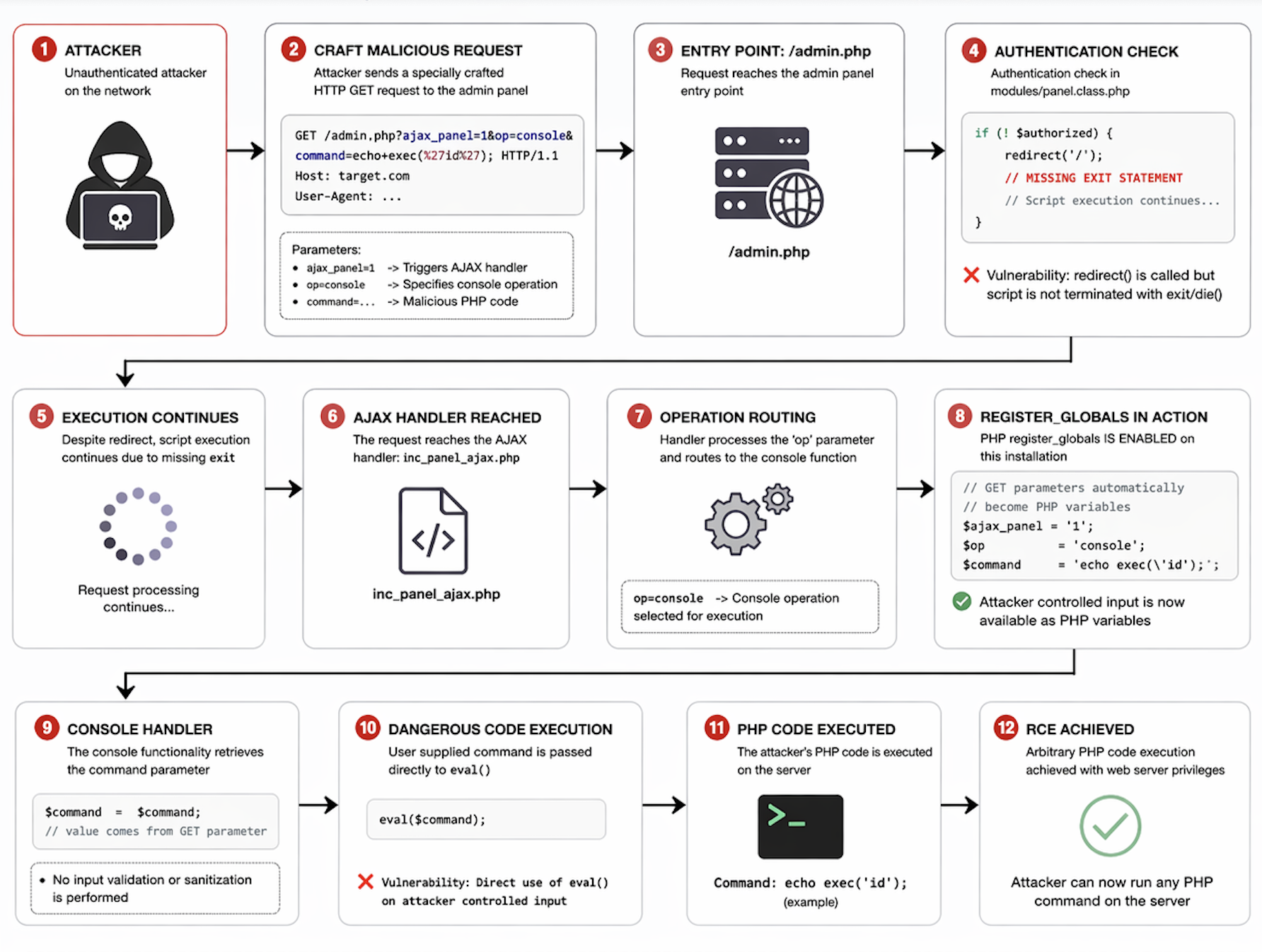
1. Attacker Identifies Exposed MajorDoMo Instance
The attack begins when a threat actor discovers an internet-accessible MajorDoMo server. Public-facing admin panels are often located through search engines, internet scanning, or misconfigured remote access deployments.
2. Malicious HTTP Request Is Crafted
The attacker sends a specially structured request to the vulnerable administrative endpoint.
The request includes parameters that trigger the internal AJAX processing path and select the console/debugging function.
3. Request Reaches /admin.php
The incoming request is handled by the main administrative controller file, typically /admin.php, which is responsible for routing backend administrative actions.
Under normal conditions, this area should only be reachable by authenticated administrators.
4. Authentication Check Is Triggered
The application performs a login/session check to determine whether the requester is authorized.
If the user is not authenticated, the system attempts to redirect the request away from the admin panel.
5. Redirect Happens but Execution Continues
This is the first major flaw.
Although a redirect response is issued, the PHP script does not terminate using exit; or die;.
Because of this, backend execution continues even though the user should have been blocked.
6. Internal AJAX Handler Is Loaded
Since execution continues, the request reaches the internal AJAX processing component (inc_panel_ajax.php).
This file is designed to process privileged asynchronous administrative actions.
7. Operation Routing Uses User Parameters
The handler reads the op parameter from the request.
When the attacker specifies the console operation, the application routes execution into the built-in administrative console functionality.
8. User Input Becomes Server Variables
Request parameters such as command become available to the application logic.
This means attacker-supplied data is now directly accessible inside the backend execution flow.
9. Console Handler Reads command
The console/debugging feature retrieves the supplied command value.
Instead of treating it as harmless text, the application prepares it for execution.
10. Dangerous eval() Is Invoked
The second critical flaw occurs here.
The application passes attacker-controlled input directly into PHP’s eval() function.
eval() interprets the provided string as PHP code and executes it on the server.
11. Arbitrary PHP Code Executes
The attacker’s payload now runs with the privileges of the web server process.
Depending on server configuration, this may allow:
- Running system commands
- Reading sensitive files
- Accessing databases
- Writing web shells
- Stealing credentials
12. Full Remote Code Execution Achieved
At this stage, the attacker has successfully obtained unauthenticated remote code execution.
The vulnerable MajorDoMo instance may now be fully compromised and used for persistence, lateral movement, or further attacks.
Proof of Concept (PoC)
A public detection template for CVE-2026-27174 has been published in the ProjectDiscovery Nuclei templates repository. This template can be used by defenders and authorized security teams to identify exposed and vulnerable MajorDoMo instances.
Public Template Reference:
Nuclei CVE-2026-27174 detection template (ProjectDiscovery repository)
https://github.com/projectdiscovery/nuclei-templates/blob/main/http/cves/2026/CVE-2026-27174.yaml
nuclei -u http://ip:8000 -t CVE-2026-27174.yaml
Exploit Demonstration
The following example illustrates a crafted HTTP GET request targeting the vulnerable administrative endpoint of MajorDoMo associated with CVE-2026-27174.
curl "http://example.com:8000/admin.php?ajax_panel=1&op=console&command=echo+exec(%27id%27);"This request is designed to reach the internal console/debugging handler through the exposed admin interface and supply attacker-controlled input through the command parameter.
Parameter Breakdown
- /admin.php — Main administrative controller endpoint
- ajax_panel=1 — Triggers the AJAX request processing path
- op=console — Selects the internal console/debugging operation
- command= — Passes user-supplied input to the vulnerable code path

Potential Attacker Capabilities
1. Execute Arbitrary PHP Code
Attackers may run malicious PHP instructions directly through the vulnerable console handler, enabling unrestricted interaction with the application environment.
2. Read Sensitive Files
An attacker may access files such as:
- /etc/passwd
- application configuration files
- database credentials
- API keys
- stored tokens
- automation secrets
3. Write Web Shells for Persistence
Attackers may upload or create PHP backdoors that provide persistent remote access even after the original vulnerability is patched.
4. Escalate to OS Command Execution
If dangerous PHP functions are enabled, attackers may invoke system-level commands using:
- system()
- exec()
- shell_exec()
- passthru()
This may allow deeper compromise of the host operating system.
5. Manipulate Smart-Home Automation
Because MajorDoMo often controls connected devices, attackers may alter schedules, disable automations, or interfere with sensors and cameras.
6. Steal Data and Credentials
Stored passwords, integration secrets, and tokens may be exfiltrated for later use.
7. Pivot into Internal Networks
A compromised MajorDoMo server may be used as a foothold to scan or attack other internal systems.
Mitigation & Remediation
Organizations using MajorDoMo should take urgent steps to reduce exposure and prevent unauthenticated remote code execution.
1. Restrict Access to the Admin Panel
Limit access to /admin.php and other administrative interfaces to trusted internal IP addresses only using firewall rules, ACLs, or reverse proxy restrictions.
2. Place the Admin Interface Behind a VPN
If remote administration is required, expose the platform only through a secure VPN rather than directly to the internet.
3. Deploy Reverse Proxy Authentication
Use an additional authentication layer such as:
- HTTP Basic Auth
- SSO gateway
- MFA-protected identity proxy
4. Disable the PHP Console Feature
If the debugging console or PHP execution feature is not operationally required, disable or remove it entirely.
5. Audit Logs for Prior Exploitation
Review web server, PHP, and system logs for suspicious requests involving:
- /admin.php
- ajax_panel=1
- op=console
- unexpected command strings
6. Rotate Credentials and Secrets
If compromise is suspected, rotate:
- admin passwords
- API tokens
- database credentials
- third-party integration keys
7. Update to the Latest Patched Version
Apply the vendor fix / patched release of MajorDoMo as soon as possible.
Conclusion
CVE-2026-27174 demonstrates how two seemingly minor coding mistakes—failing to terminate execution after an authentication redirect and using PHP’s eval() on user-controlled input—can combine into a critical unauthenticated remote code execution vulnerability. In the case of MajorDoMo, these flaws exposed the platform’s administrative interface to remote attackers without requiring valid credentials.
Because MajorDoMo often serves as the central controller for smart-home devices, sensors, cameras, and internal automation systems, the security impact extends far beyond a single web application. Successful exploitation may result in full server compromise, credential theft, persistent access, and unauthorized control over connected environments.
Organizations using MajorDoMo should treat this vulnerability as a high-priority risk. Immediate patching, restricting access to the admin panel, disabling unnecessary console features, and reviewing systems for indicators of compromise are strongly recommended. This case also reinforces an important secure-development lesson: never rely on redirects for access control, and never execute untrusted input dynamically.

