Healthcare Data Breach: Cybercriminals Attacked Health Insurance Agency in Ecuador
Cyber Threat Intelligence


Introduction
Cybercriminals targeted Saludsa, the largest prepaid medical company in Ecuador, offering a wide range of health insurance plans and services for citizens. Resecurity is investigating the incident and collaborating with local law enforcement agencies (LEA).
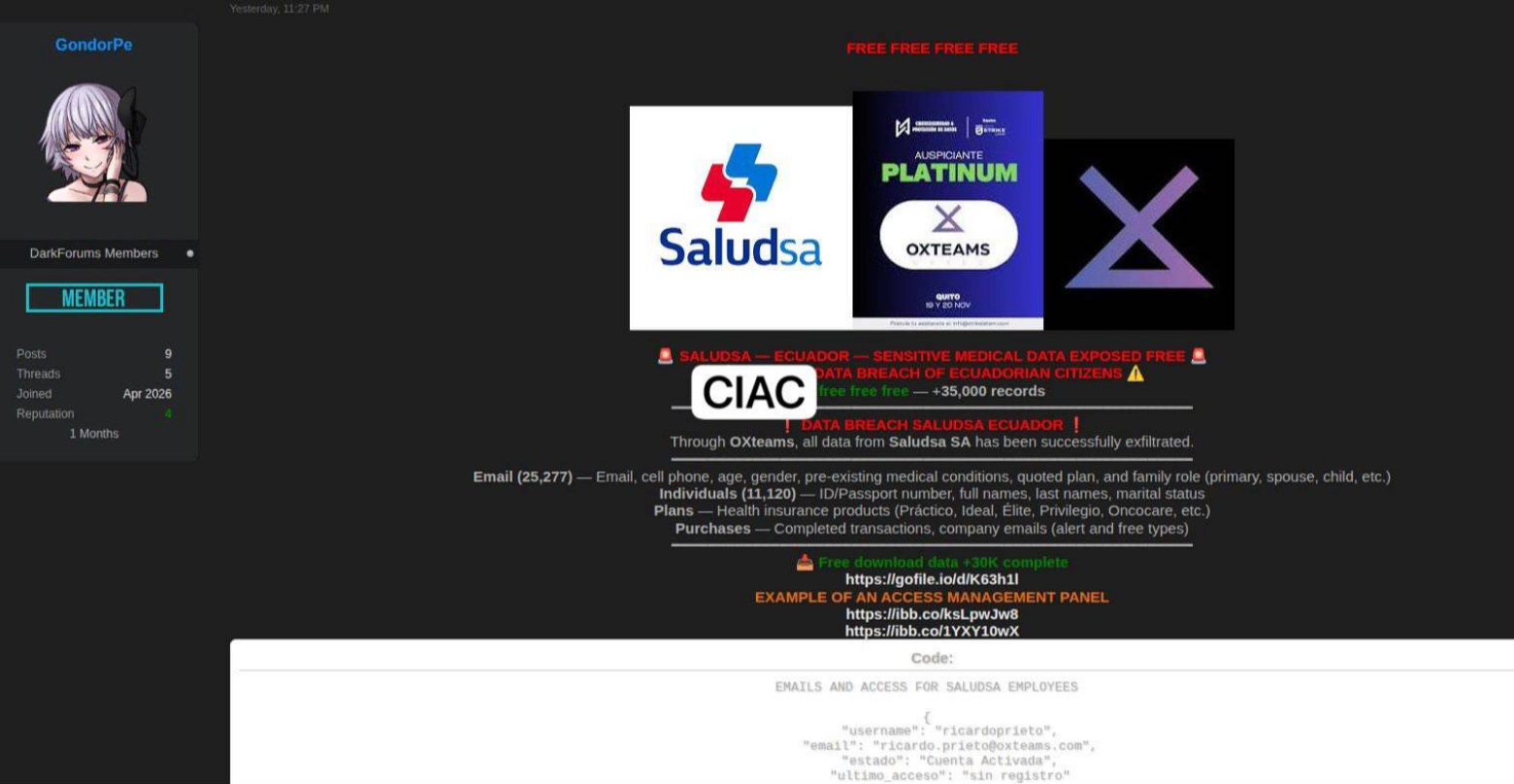
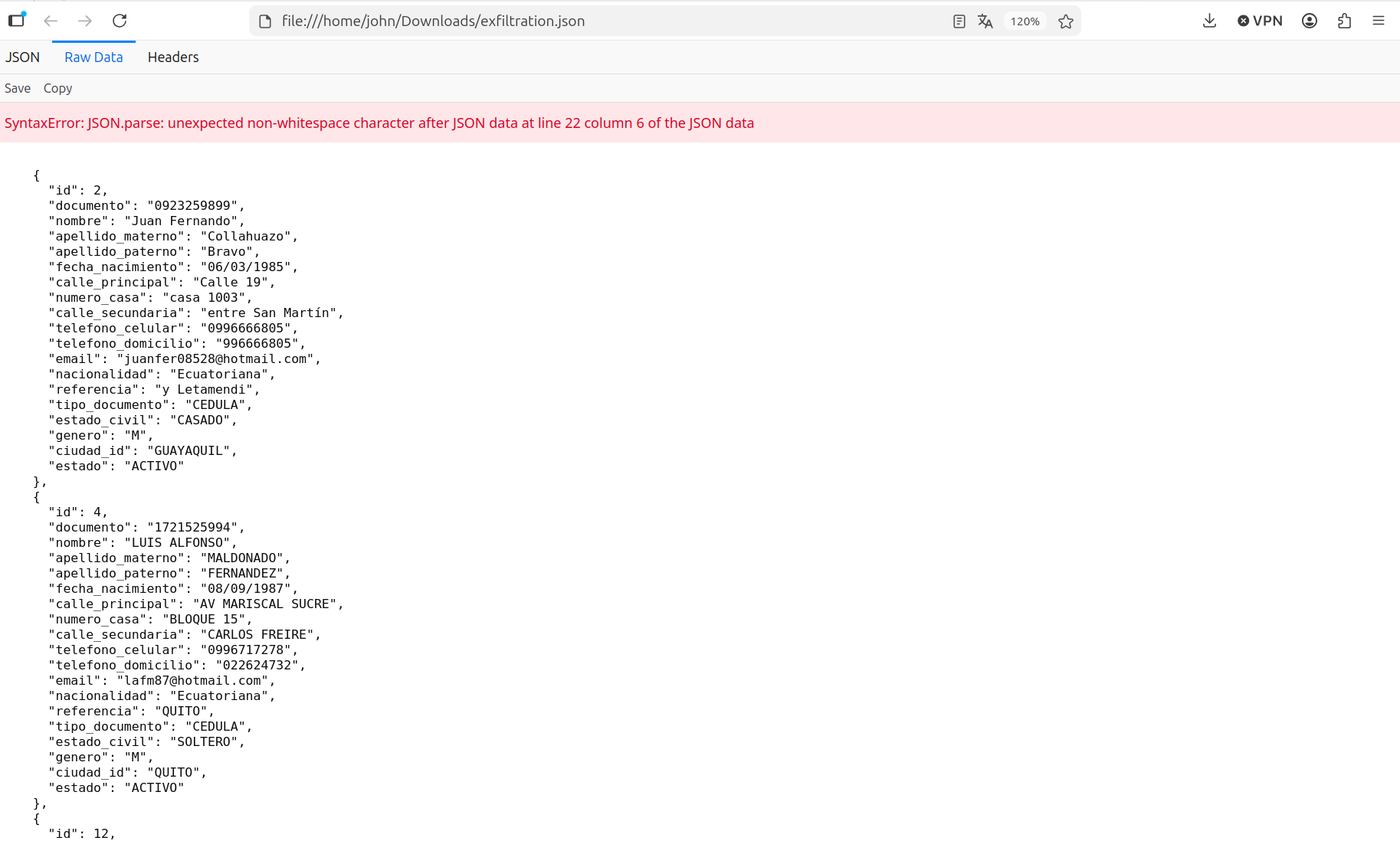
Cybercriminals leaked over 35,000 records containing information about customers of medical services, including their email, cell phone number, gender, pre-existing medical conditions, and insurance plans. Additional context about the victims could also reveal payment details, which could be used in fraudulent campaigns. The stolen data has been released as a JSON dump.
Scope of Data Breach
Cybercriminals claim to have stolen a massive amount of data from the affected victim organization. Considering that insurance organizations store customer data, such incidents create substantial privacy risks due to the leak of PII.
Sensitive Medical Information (25,277 records):
Includes pre-existing medical conditions, contracted plan types (Práctico, Ideal, Élite, Oncocare), and family roles.
Citizen Identity Data (11,120 records):
National ID or passport numbers, full names, and marital status.
Contact and Transaction Data:
Email addresses, mobile phone numbers, age, gender, and records of completed purchases/transactions.
Corporate Records:
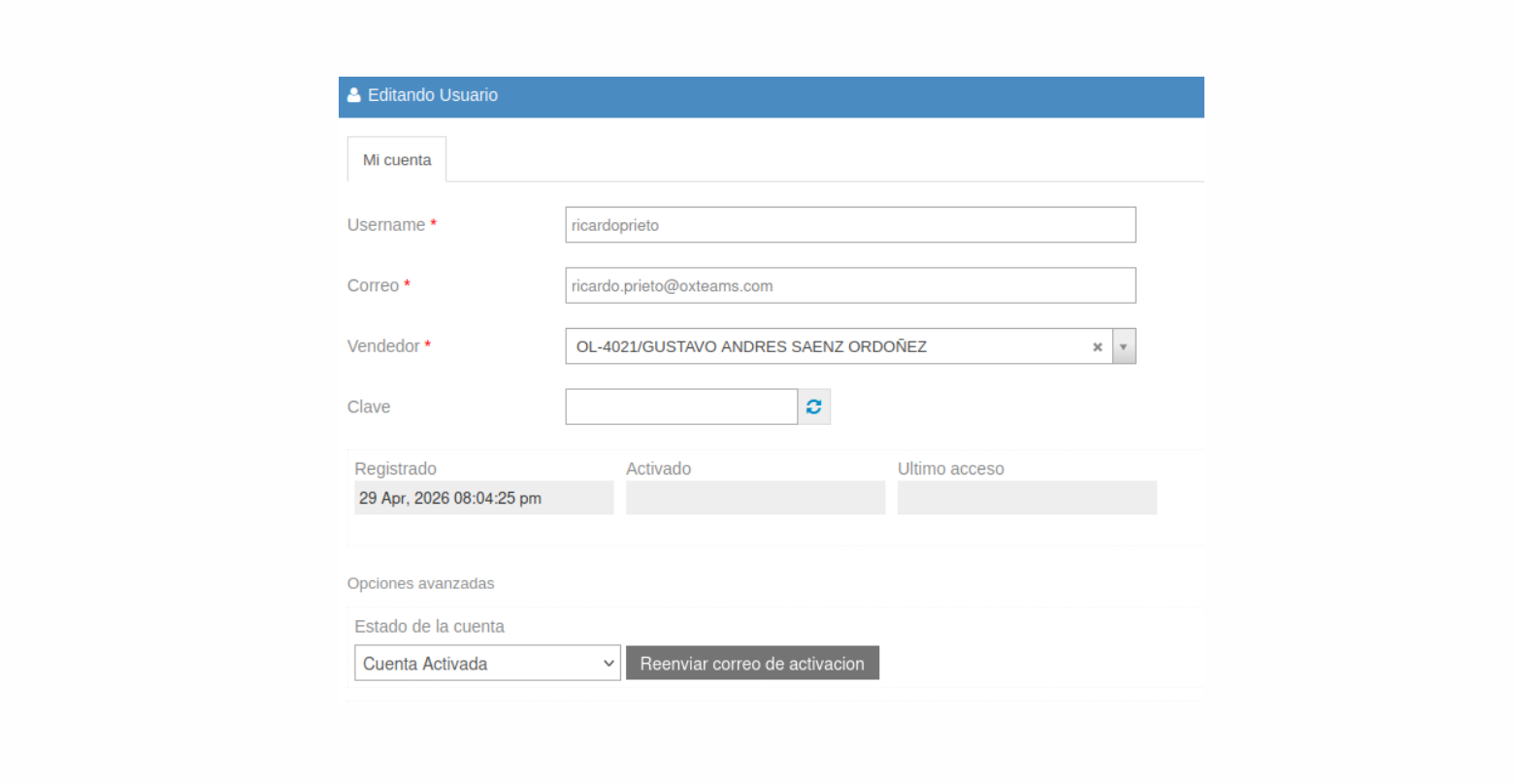
The attacker has published a list of email addresses and usernames belonging to Saludsa, as well as OXTeams, a local cybersecurity provider, with an "Activated Account" status.
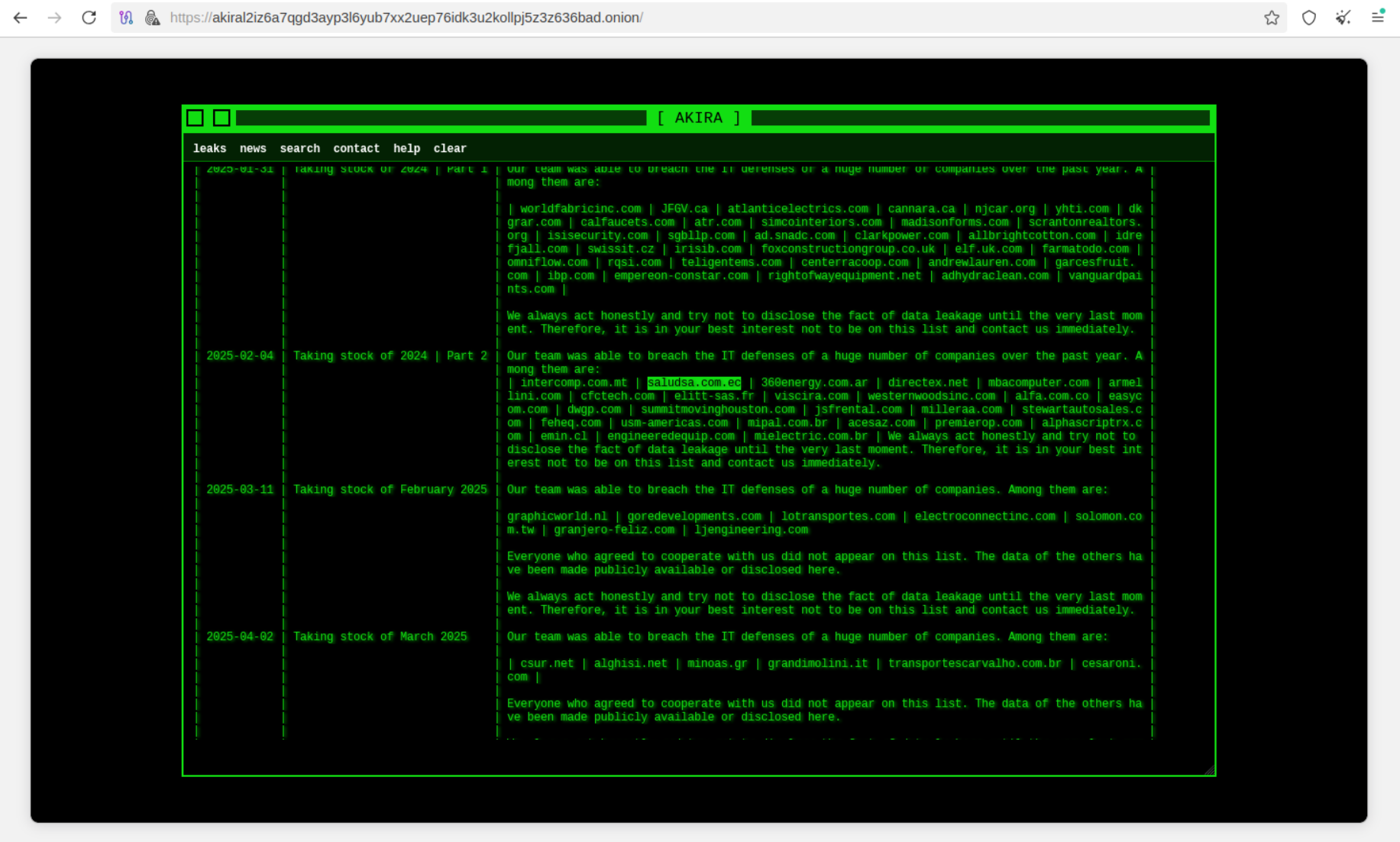
Notably, in February of last year, Saludsa had already been targeted by Akira ransomware, along with many other organizations from Latin America and other regions. At that time, bad actors warned the affected organizations in Argentina, Brazil, Colombia, Chile, and Ecuador that "it is in their best interest to contact them" to negotiate and arrange ransom payments.
Root Cause
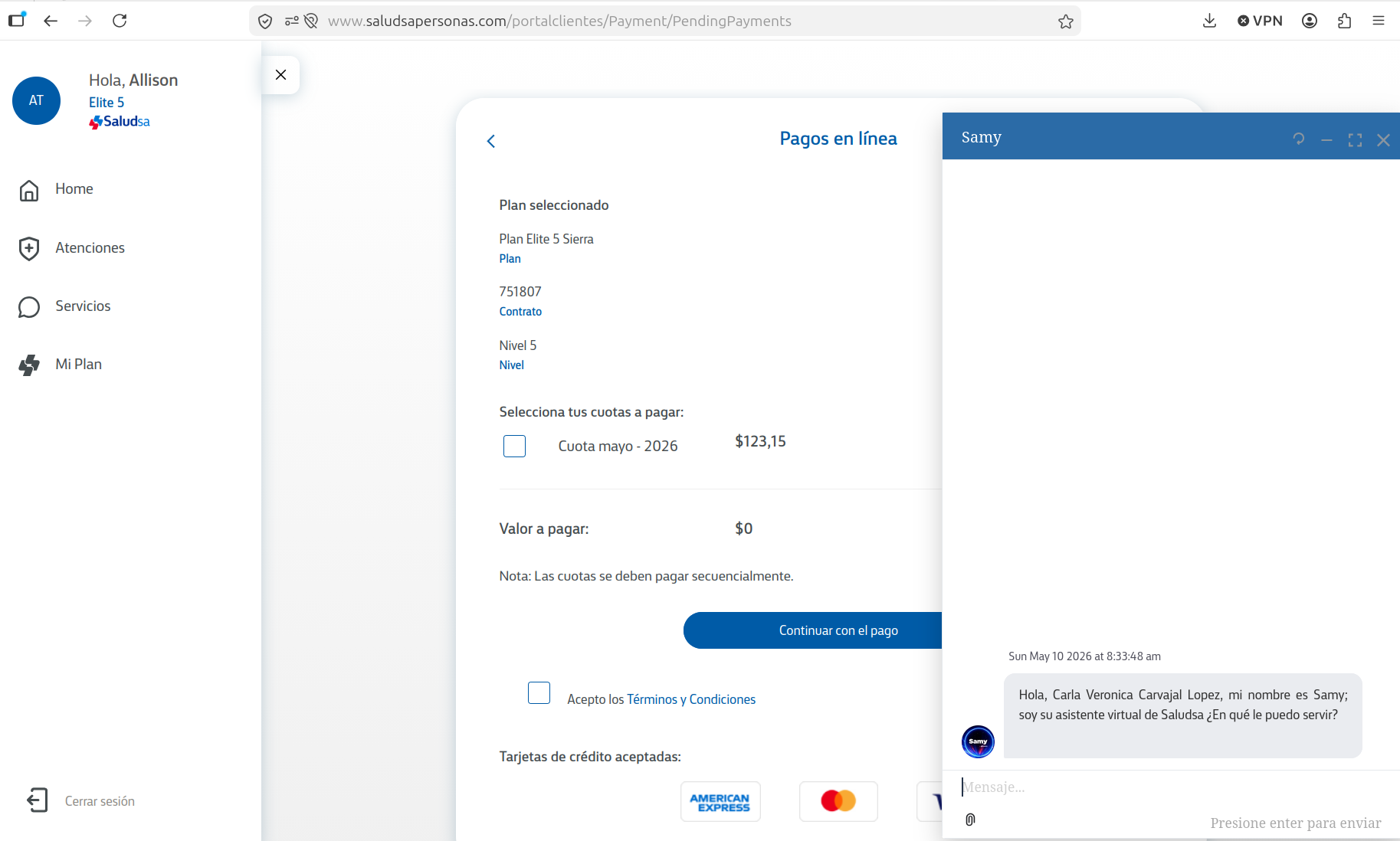
The root cause was likely the compromise of administrative access to the backend, leading to unauthorized access to customer data. With privileged access, attackers could have nearly unlimited opportunities to extract consumer records. Typically, such a level of access should be isolated from remote access. Threat actors have also added an additional administrator account, "pwn2026."
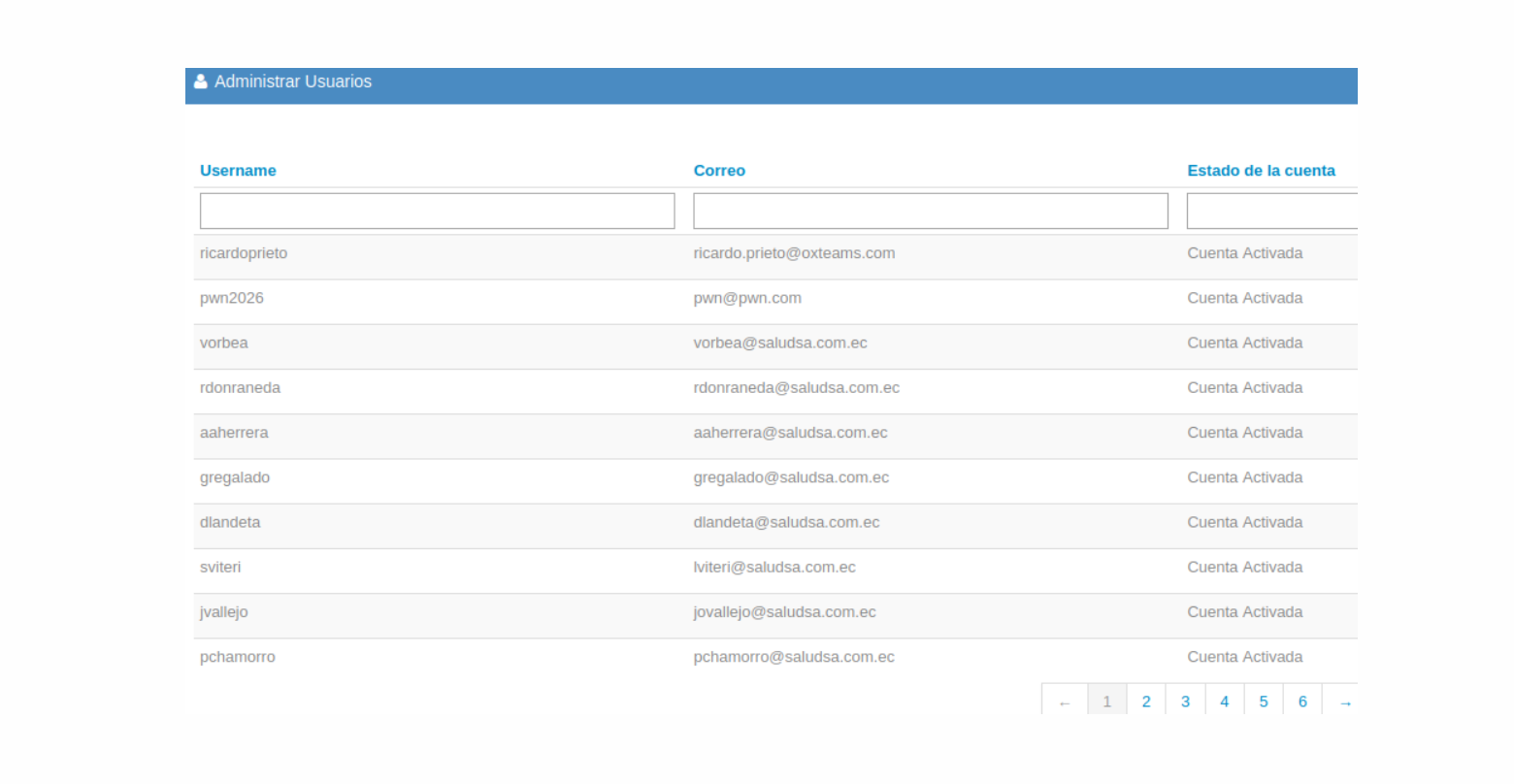
Cybercriminals provided additional proof of the breach by revealing records of vendors responsible for IT and cybersecurity operations, along with their successful login timestamps from April 29, 2026, which may confirm the recent breach.
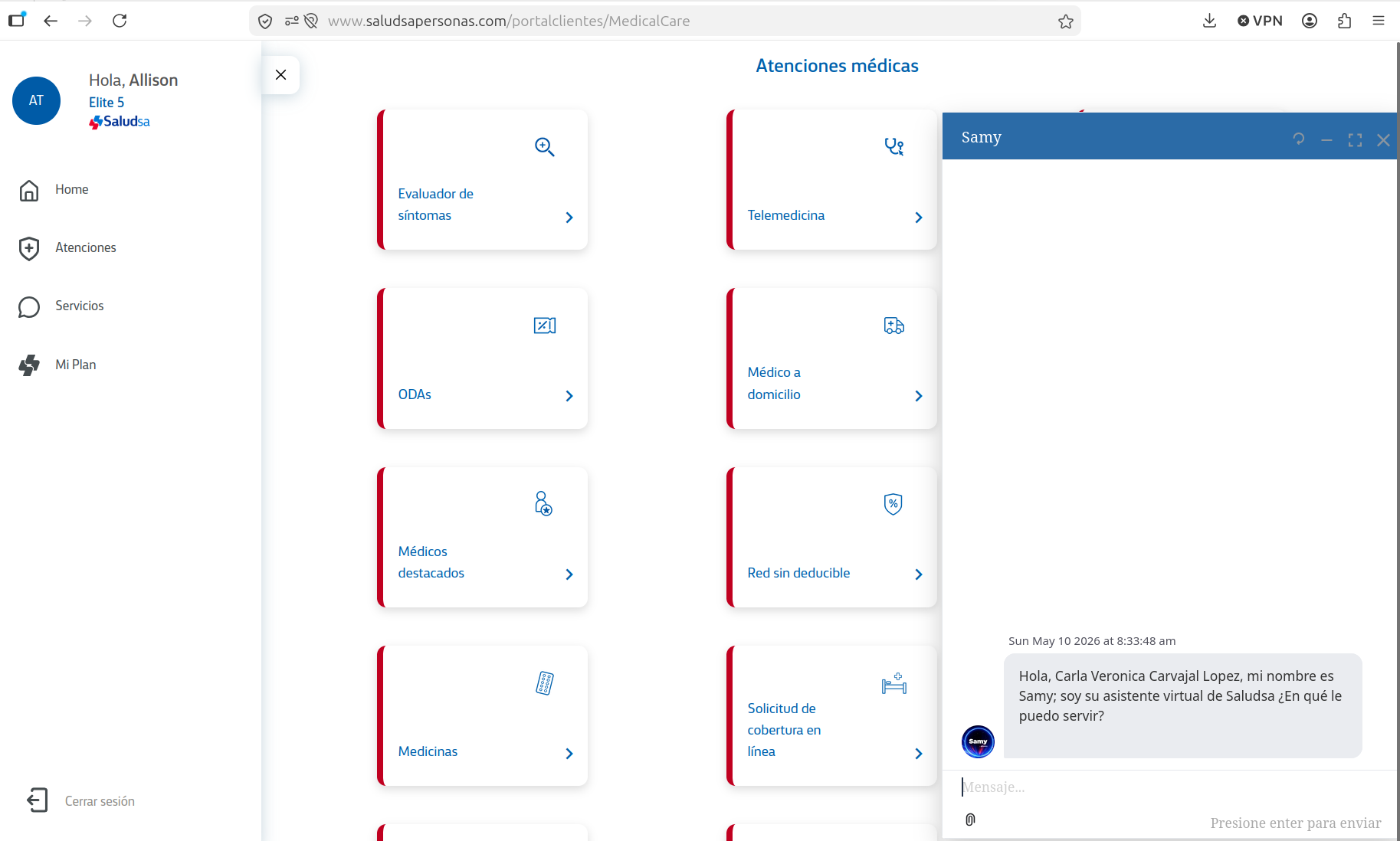
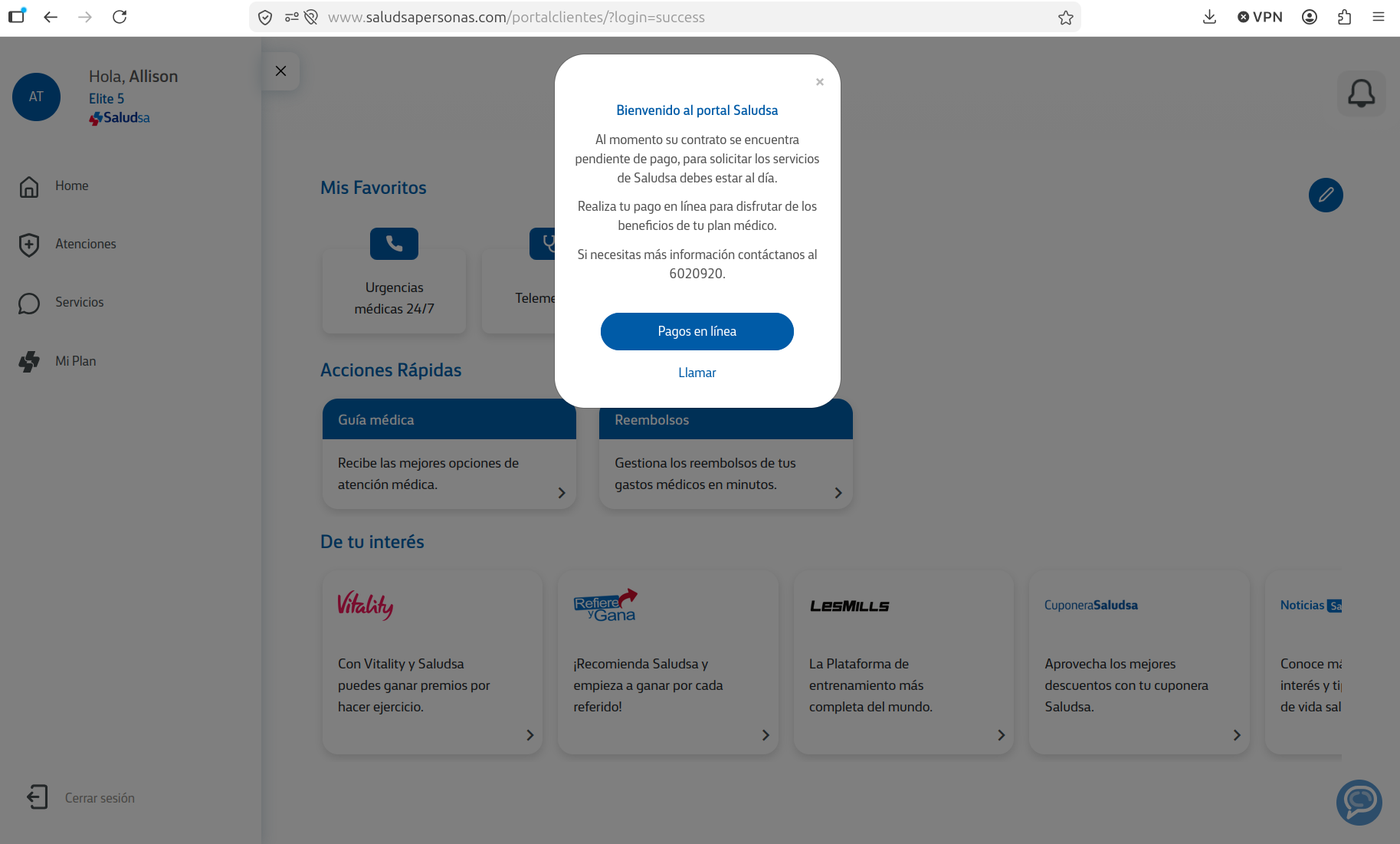
Resecurity has also identified thousands of customers affected by infostealer activity. Their credentials were available on the Dark Web and could be used to scrape data from their profiles. Notably, the platform did not require customers to enable or enforce MFA, which allowed easy access to data simply by entering a login and password—sometimes as simple as "123456."
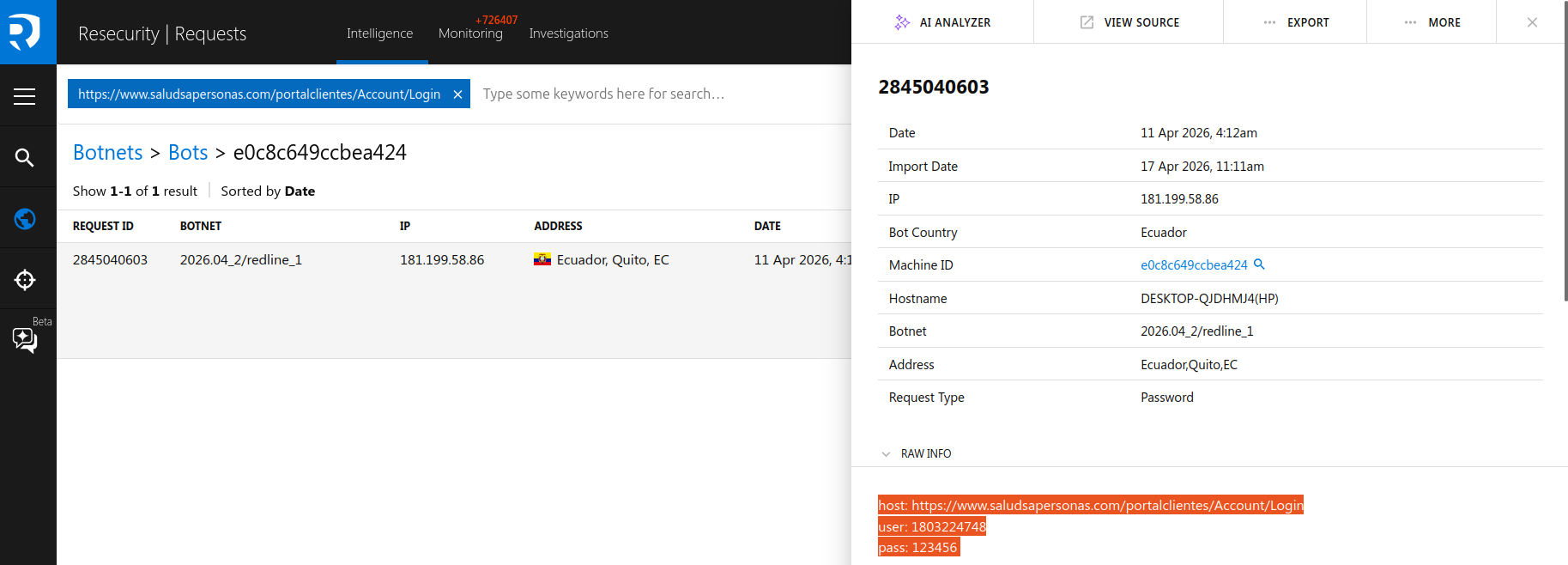
Gained access enabled cybercriminals to view customer profiles and access available services and records. A combination of traditional hacking and the exploitation of web application security vulnerabilities, along with infostealers, may create significant advantages for threat actors to conduct targeted intrusions, leading to data leakage.
The platform was protected only by a basic CAPTCHA, which could be easily bypassed.
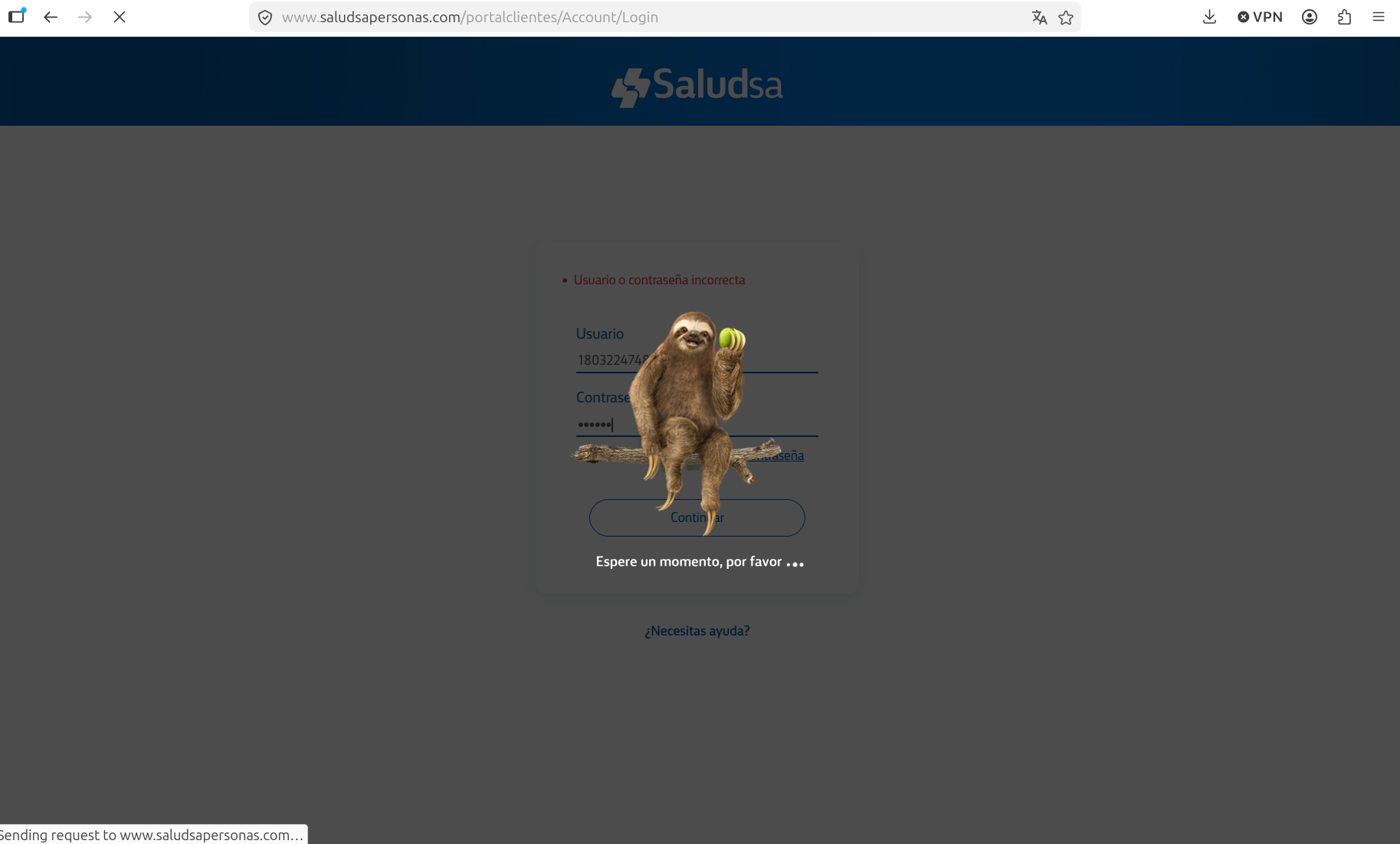
According to best practices, customer portals should have MFA enabled by default during onboarding; otherwise, they may pose data leak risks. As of May 10, following the incident, the customer portal remains operational without MFA.
Resecurity has also identified attempts to conduct insurance fraud and account takeovers using stolen data. Customers should be cautious when responding to any suspicious messages offering new services, discounts, or asking them to change their passwords or provide payment information.
Compliance
The main data protection regulation in Ecuador for healthcare data is the Ley Orgánica de Protección de Datos Personales (LOPDP). This law specifically classifies health data as sensitive personal data and imposes enhanced protections, including strict consent, security, and confidentiality requirements. The law is enforced by the Superintendencia de Protección de Datos Personales, and is complemented by sector-specific regulations from the Ministry of Public Health and the Ley Orgánica de Salud.
Ecuador’s LOPDP is the cornerstone of personal data protection, including healthcare data. It mandates robust safeguards for sensitive health information, enforces strict consent and confidentiality standards, and is supported by sector-specific regulations. The Superintendencia de Protección de Datos Personales ensures compliance and protection of individuals’ rights under this framework.
If you handle or process healthcare data in Ecuador, compliance with the LOPDP (Ley Orgánica de Protección de Datos Personales) and related sector-specific regulations is mandatory, with special attention to health information. Resecurity is assisting businesses of any size in preventing data breaches through proactive cyber threat intelligence (CTI) and ongoing vulnerability assessment and penetration testing (VAPT).
Data Breach Victim Notification Program (DBVNP)
Resecurity's Data Breach Victim Notification Program (DBVNP) is a proactive initiative designed to identify data breaches and provide timely notifications to consumers and enterprises worldwide affected by cyber incidents. The program leverages advanced cyber threat intelligence (CTI) and digital identity protection, global monitoring capabilities, and established partnerships with regulators and law enforcement agencies to report compromised data and mitigate potential consequences for victims by increasing transparency about possible incidents and their root causes. By combining technology with a victim-centric approach, the program ensures that affected individuals and organizations are promptly informed, enabling them to take action to secure their information, prevent further harm, and protect their rights.
The goal of the program is to shift from a reactive to a proactive approach by detecting data breaches and supporting existing data protection regulations, especially in complex cross-border incidents affecting US and EU consumers who share their personal information with online services and data processors located abroad. For example, in cases of previously undisclosed data breaches, impacted consumers remain extremely vulnerable due to a lack of proper mechanisms to inform them of such incidents or frameworks to cover potential damages. The program aims to establish transparency in responsible data breach disclosure and to facilitate the harmonization of cybersecurity practices worldwide to protect consumers and organizations.
The need for information sharing about data breaches and security incidents was one of the central topics at the past RSA Conference 2026 in San Francisco. The experts agreed on the importance of increasing transparency around breaches, as well as establishing voluntary reporting channels. Resecurity arranged thousands of victim notifications to increase awareness among the affected consumers. Adding transparency around data breaches will ensure that consumers have the right to protect their privacy and may also be eligible for compensation in case such events cause damage.
The Saludsa data breach is a great example of why this program is so critical. Victims in Latin America remain unaware of such incidents—putting their privacy at risk. Organizations need to implement robust cybersecurity controls to mitigate such incidents before they cause any damage. Resecurity remains committed to protecting consumers and organizations worldwide by providing actionable intelligence and solutions to prevent breaches at an early stage.

